Conversation
**Why**: Security release. Reference: https://rubyonrails.org/2022/4/26/Rails-7-0-2-4-6-1-5-1-6-0-4-8-and-5-2-7-1-have-been-released changelog: Internal, Dependencies, Update dependencies to resolve security advisories
* add failing spec * Ensure sp redirect_url exists before sending to completions page changelog: Bug Fixes, Authentication, Avoid 500 error by not incorrectly redirecting to service provider consent page * Update app/controllers/concerns/verify_sp_attributes_concern.rb Co-authored-by: Andrew Duthie <andrew.duthie@gsa.gov> Co-authored-by: Andrew Duthie <andrew.duthie@gsa.gov>
[skip changelog]
* Add missing costs tracking for async doc auth **Why**: So that we are consistently tracking costs between sync and async implementations * Add changelog changelog: Upcoming Features, Async Document Authentication, Consistently log costs for document capture * Improve specs by filtering costs by expected issuer
Updates were made to require AAL2 if partners request it. changelog: Single SIgn On, Authentication, support requested aal timeout,
…a user reproofs without liveness (#6260) We use the proofing components on a profile to ensure a user's profile has a liveness check when a liveness check is required. This commit adds a spec to ensure that a user is not marked as having a liveness check present if they reproof without liveness. changelog: Internal, Testing, A test was added to cover an edge case when re-proofing without facial matching
[skip changelog]
changelog: Internal, Optimization, Do not create sp_costs for unused cost types
Liveness checking specific functionality is being discarded in favor of a full IAL2 compliant flow which may include additional deltas. That makes this flag confusing and hopefully unnecessary so this commit removes it. A follow on commit will be required to drop the column. * changelog: Internal, Service provider management, An unnecessary flag for setting liveness checking requirements on an SP was removed
[skip changelog]
* Add and fix spec coverage for JS-enabled, IAL2 strict doc auth **Why**: Because it appears we did not have coverage for this flow previously, evidenced by the fact that the current test helpers are currently broken. changelog: Internal, Automated Testing, Improve test coverage for proofing flow * Use translated labels for field association
* Add form validation for present TOTP name **Why**: For consistency with other MFA setup, and for consistency with the JS-enabled user experience, where the input is rendered as required. changelog: Bug Fixes, MFA Setup, Consistently validate TOTP name * Pass name parameter for controller specs * Improve specs for TOTP setup controller * Fill in name * More forms! * Try non-unique app names in specs should be unique user / MFA setup between specs
The letter flow as it is implemented may not meet the bar for strict IAL2. This commit adds a method for checking whether a letter was used to verify a user to enable building conditionals around that in a future change. * changelog: Internal, Proofing, A helper was added to the Profile model to determine if a user verified their address with a letter or by phone
* Fix SAML auth context handling for IAL2 strict request **Why**: So that an IAL2 strict request behaves similar to a standard IAL2 request, particularly in how a user should be directed to enter their password to decrypt PII if encrypted. [skip changelog] * Check explicitly for ial2_strict in SAML requested_attributes Avoid disambiguating IAL2 as meaning either "IAL2" or "IAL2 strict", since we don't seem to have a tendency to do that
…ure-flagged) (#6269) * LG-6193: Integrate IdV app personal key step into proofing flow **Why**: So that a user can functionally complete the proofing process using the new IdV app. changelog: Upcoming Features, Identity Verification, Add personal key step screen * Move completion behavior to pack * Add spec for VerifyFlow * Revert feature specs covering personal key page deal with it later * Fix VerifyFlow spec Maybe bug with testing-library? Seems to struggle querying by role "TypeError: style.getPropertyValue is not a function" * Stub applicant for VerifyController spec copied from personal_key_controller_spec.rb
**Why**: Because `encrypt_recovery_pii` is already called as part of the preceding `encrypt_pii`. changelog: Internal, Automated Testing, Reduce redundancy in test data setup
* personal-key repo
* update route to verify/complete/personal_key
* get request working with postman to return empty hash for now
* add_proofing_component to get_personal_key
* add analytics for personal key
* update complete_controller
* update error messages for the 2 factor auth so api can get proper json response
* cleanup code
* update the application controller
* changes made to return proper json error responses
* latest changes
* update code
* create the profile and cache the pii
* create the profile creation form correctly
* clean up the JWT code, use idv certificate pair
* update code
* changes made to cleanup code
* update FormResponse to return a {} if extra_attributes is nil
* changes made to fix the correct jwt to return user key
* specs for Api::ProfileCreationForm
* specs for Api::ProfileCreationForm (for reals)
* add rspec tests
* cleanup test
* cleanup code
* fix profile creation form spec on recovery key
* changes made to make it a post instead of a get
* cleanup lint
* fix some more linter errors
* Include "personal_key" as alertable key in analytics PiiDetector
**Why**: Since we don't want to be including this detail in any logs, as it is password-like.
* Revert "Include "personal_key" as alertable key in analytics PiiDetector"
This reverts commit 3f00de9.
* implement/test complete_session
* changes made to fix the code review feedacks
* get rid of aliased methods
* lints
* fix linter error
* remove parenthesis
* code review feedback
* changelog: Upcoming Features, Identity Verification, API endpoint for IdV completion
* fix line space
* code review feedback
* fix lint error
* add feature flagging
* move the personal_key to a dedicated method, encapsulate the JWT in a decorator
* lints
* convert profile_completion_form to return the personal_key separately from the response.
* remove unused custom form response class
* Update config/routes.rb
Co-authored-by: Andrew Duthie <andrew.duthie@gsa.gov>
* Update app/forms/api/profile_creation_form.rb
to fetch pii from the PII::Cacher
Co-authored-by: Mitchell Henke <mitchell.henke@gsa.gov>
* remove `gpo_otp` as a method on the form
* move the feature flag check from routes.rb to the controller
* remove unnecessary session usage
* default keys for IdV JWTs
* guard against small IdV JWT keys in production envs
Co-authored-by: Douglas Price <douglas.price@gsa.gov>
Co-authored-by: Andrew Duthie <andrew.duthie@gsa.gov>
Co-authored-by: Mitchell Henke <mitchell.henke@gsa.gov>
…6272) changelog: Internal, Continuous Integration, Fix issue with validating the changelog on long branch histories in GitLab
changelog: Internal, Maintenance, Drop unused columns on users table
* Upload artifact and sync static assets in GitLab CI changelog: Internal, Continuous Deployment, Enable uploading application artifacts and static assets from GitLab CI * add execute permissions to script * fix sources for running pipeline * add ruby cache to coverage step * return early if current branch is not configured
changelog: Bug Fixes, Logging, Fix error during SAML authentication when receiving invalid referer
[skip changelog]
…proofing (#6270) We may need to make a change in the future to require strict IAL2 users to proof with phone. This commit does some work towards making that possible. It makes changes to the authorization controller to prevent a user from being redirected at strict IAL2 unless they have proofed with phone. This change is not totally complete, there are changes that will need to go in place to remove the option during proofing. changelog: Upcoming feature, Proofing, A user will need to proof with a phone before being sent back to the IdP for strict IAL2 proofing
* Implement client session secret store **Why**: As a demonstration of secure client-side storage decrypted with key provided by server per session. changelog: Upcoming Features, Identity Proofing, Add client-side encrypted storage * Collapse readStorage try blocks * Clarify AES cipher key/iv generation To avoid magic number and make it clearer what's happening #6183 (comment) * Simplify cipher assignment logic * Refactor SecretsContextProvider as observable initializer - Avoid waiting to render the app - Manage subscribers automatically via context value change * Rename encode as s2ab Consistency #6183 (comment) * iv per encrypt #6183 (comment) * Make setItem await-able * Reference crypto consistently from window object * Add SecretSessionStorage inline comment docs * Add SecretSessionStorage specs * Merge useSecretValue to context implementation * Remove demo value from SecretValues * Add docs for SecretsContext * Use flow values as secrets * Split VerifyFlow from index Avoid dependency cycle, make room for more index-exported * Destructure storeKey in same way as other data attributes * Use user_session instead of session Route now authenticated * Inline encryption cipher initialization to memoized session assignment See: https://github.com/18F/identity-idp/pull/6183/files#r865355166 Co-Authored-By: Zach Margolis <zbmargolis@gmail.com> Co-authored-by: Zach Margolis <zbmargolis@gmail.com>
* TypeScript-ify Alert component * Components: Assign Alert role by type **Why**: - Alignment to AlertComponent Rails ViewComponent implementation - To avoid assertively announcing alert text for non-urgent alerts changelog: Improvements, Accessibility, Use status role for non-urgent alert content
[skip changelog]
* LG-5929-document-analytics-11 * Patch: analytics events 11 (#6303) * Remove @identity.idp.event_name - As of #6294, having it will cause build breakage since it's an unknown tag * Remove blank lines * Add clearer comments for each event Co-authored-by: Zach Margolis <zachmargolis@users.noreply.github.com>
There is a chance we won't be able to roll out a compliant IAL2 flow with the USPS letter flow in place. This commit adds the ability to remove the letter flow option from strict IAL2 if that does become the case. * changelog: Upcoming Features, Proofing, The ability to disable the option to proof with a letter during IAL2 strict was added
changelog: Analytics, Document authorization, updates
* Translate labels for IdV app step indicator **Why**: So that labels are shown in the user's preferred language. changelog: Upcoming Features, Identity Verification, Add personal key step screen * Create type for step indicator steps See: https://github.com/18F/identity-idp/pull/6310/files#r866030157 Co-Authored-By: Zach Margolis <zbmargolis@gmail.com> Co-authored-by: Zach Margolis <zbmargolis@gmail.com>
…p into lg-6202-create-accordion
| redirect_to account_url if idv_session.profile.blank? | ||
| end | ||
|
|
||
| def personal_key |
There was a problem hiding this comment.
I wouldn't expect this change to be here. Is it from a merge conflict?
There was a problem hiding this comment.
It was there before. But now not needed.
There was a problem hiding this comment.
It's still called here:
| it('renders the active step', async () => { | ||
| const { getByText } = render(<FormSteps steps={STEPS} />); | ||
|
|
||
| await userEvent.click(getByText('forms.buttons.continue')); |
There was a problem hiding this comment.
I wouldn't expect this change to be here. Is it from a merge conflict?
|
|
||
| export default { | ||
| name: 'password_confirm', | ||
| title: t('titles.idv.session.review'), |
There was a problem hiding this comment.
Via build failure, this locale key doesn't exist. I think it should be....
| title: t('titles.idv.session.review'), | |
| title: t('idv.titles.session.review'), |
| import type { FormStepComponentProps } from '@18f/identity-form-steps'; | ||
| import type { VerifyFlowValues } from '../..'; | ||
| import { Accordion } from '@18f/identity-components'; | ||
| import parsePhoneNumber from 'libphonenumber-js'; |
There was a problem hiding this comment.
Earlier review comment still stands.
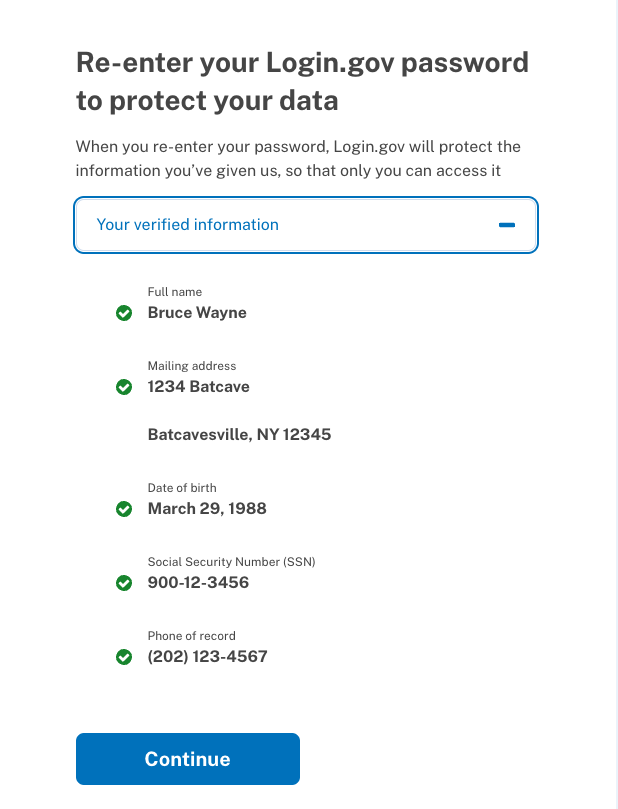
| <> | ||
| <PageHeading>{t('idv.titles.session.review', { app_name: 'Login.gov' })}</PageHeading> | ||
| <p>{t('idv.messages.sessions.review_message', { app_name: 'Login.gov' })}</p> | ||
| <Accordion header={t('idv.messages.review.intro')}>{PersonalInfoSummary(value)}</Accordion> |
There was a problem hiding this comment.
If we're treating PersonalInfoSummary as a component, we should use JSX, which will also require updating the parameters to accept a props object.
| <Accordion header={t('idv.messages.review.intro')}>{PersonalInfoSummary(value)}</Accordion> | |
| <Accordion header={t('idv.messages.review.intro')}><PersonalInfoSummary pii={value} /></Accordion> |
package.json
Outdated
| "webpack": "^5.65.0", | ||
| "webpack-assets-manifest": "^5.0.6", | ||
| "webpack-cli": "^4.9.1", | ||
| "yarn-deduplicate": "^5.0.0", |
There was a problem hiding this comment.
I wouldn't expect this to be installed to the project, and instead should be installed as a global package on a developer's machine.
| "yarn-deduplicate": "^5.0.0", |
| branch_environments.map do |upload_environment| | ||
| static_bucket = ENV["#{upload_environment.upcase}_STATIC_BUCKET"] | ||
| if static_bucket.nil? | ||
| puts "skipping #{upload_environment} because it is missing static bucket config!" |
There was a problem hiding this comment.
I wouldn't expect this change to be here. Is it from a merge conflict?
|
cleaned up branch and moved here. #6338 |
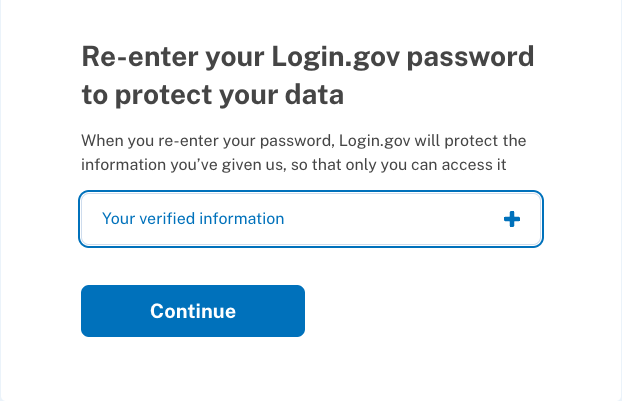
This pull request, refactors the password confirmation page to be in react. This particular code only focuses on the accordion that is on the password confirmation page.