[Fleet][Endpoint][RBAC V2] Update fleet router and config to allow API access via RBAC controls#145361
Conversation
020caa1 to
b29cd19
Compare
c01607f to
b82e709
Compare
## Summary RBAC UI features for Trusted Applications. To test, enable `endpointRbacEnabled` feature-flag, create a non-superuser user with _Security: ALL_ privilege and (All | Read | None) sub-privilege for _Trusted Applications_. <img width="541" alt="image" src="https://user-images.githubusercontent.com/39014407/203073992-fb71e293-2cd8-4639-8d61-4867e39ef071.png"> The modification should: - hide Trusted Apps from Manage navigation items if privilege is NONE, (note: it is still displayed for non-superusers, if the feature flag is disabled) - disable add/edit/delete for Trusted Applications if privilege is READ. ##⚠️ Note This PR focuses on _Read_ and _None_. The sub-privilege _All_ does not work perfectly at the moment, because of unauthorised API calls. A follow-up PR will fix this, after this PR is merged: #145361 ### Checklist Delete any items that are not applicable to this PR. - [x] [Unit or functional tests](https://www.elastic.co/guide/en/kibana/master/development-tests.html) were updated or added to match the most common scenarios
e2d3807 to
e7a4db3
Compare
e7a4db3 to
7f5102a
Compare
|
Re:
I'm not sure yet about how this one should be implemented and it warrants some discussions. Our Endpoint use cases don't need @ashokaditya, |
 paul-tavares
left a comment
paul-tavares
left a comment
There was a problem hiding this comment.
@ashokaditya ,
I took a look through and am good with the changes. I'm not going to approve it just because I worked with you on this. I'll defer approval to the Fleet team
|
The code looks good to me, I'll do a few manual tests locally before I approve. |
|
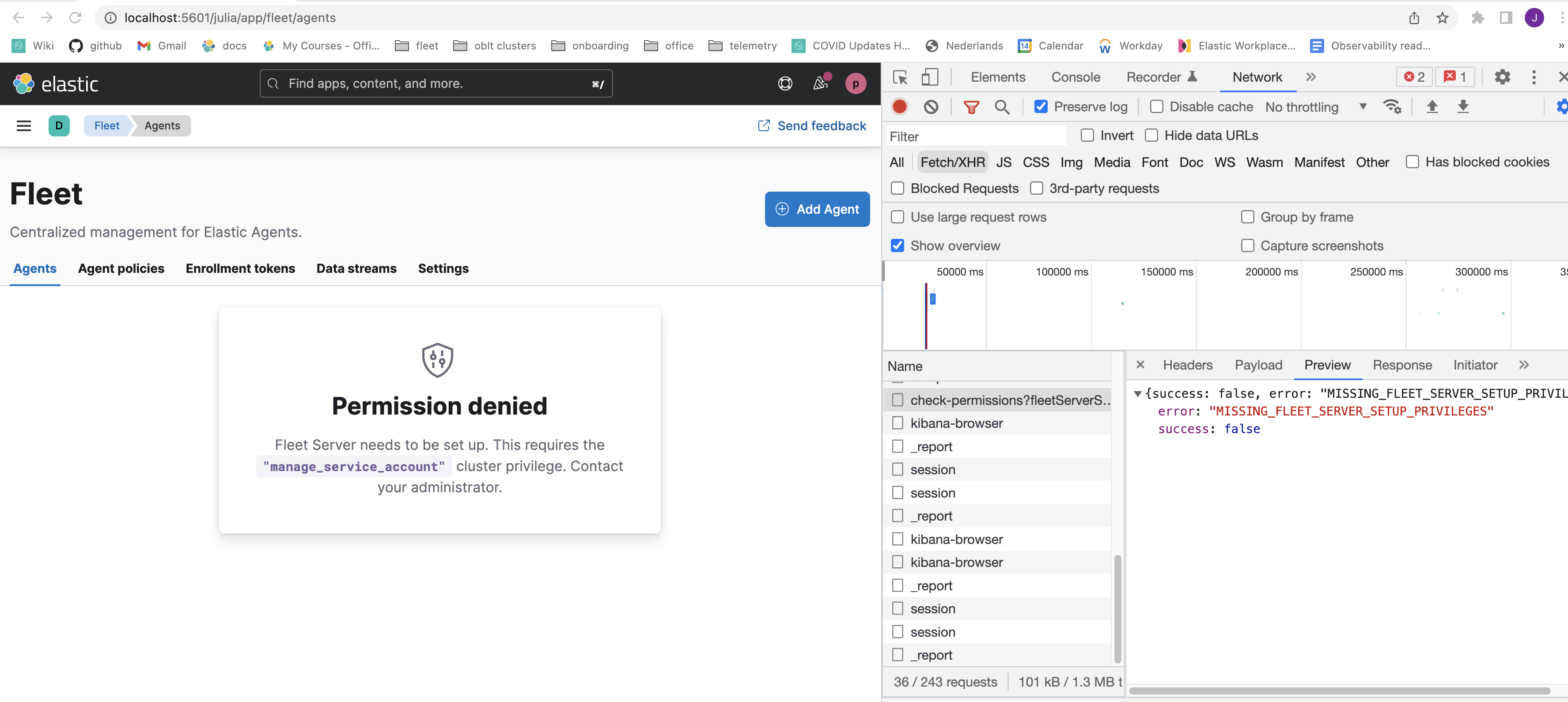
I noticed something strange, I created a role that has access to Fleet:All and Integrations:Read, and I'm getting a permission denied error on Fleet/Agents screen. Though it might be a difference between environments, as the dev-oblt doesn't use the EDIT: seeing the same behavior on |
 juliaElastic
left a comment
juliaElastic
left a comment
There was a problem hiding this comment.
LGTM, tested locally with the endpoint role and existing fleet/integrations role
💚 Build Succeeded
Metrics [docs]Public APIs missing comments
Page load bundle
Unknown metric groupsAPI count
ESLint disabled in files
ESLint disabled line counts
Total ESLint disabled count
History
To update your PR or re-run it, just comment with: cc @ashokaditya |
* main: (21 commits) [Profiling] Remove link to 'Other' bucket (elastic#147523) [Synthetics UI] Add missing configuration options to the add/edit monitor forms (elastic#147265) [DOCS] Updates what's new pages (elastic#147483) [Fleet][Endpoint][RBAC V2] Update fleet router and config to allow API access via RBAC controls (elastic#145361) [Guided onboarding] Update guide IDs (elastic#147348) [Synthetics] Add synthetics settings alerting default (elastic#147339) [Security Solution][Endpoint] Fix Policy form being displayed as Read Only when displayed in Fleet pages (elastic#147212) [Cases] Save draft user comment (elastic#146327) [API Docs] Fix `--plugin` filter (elastic#147500) [Fleet] added a logic to use `destinationId` when tagging imported SOs (elastic#147439) Do not skip UPDATE_TARGET_MAPPINGS if upgrading to a newer stack version (elastic#147503) [Discover] Validate if Data View time field exists on Alert creation / editing (elastic#146324) [Discover] Fix Discover navigation from Lens embeddable (elastic#147000) Allow users to Update API Keys (elastic#146237) Update dependency xstate to ^4.35.0 (main) (elastic#147463) [Behavioral Analytics] Remove feature flag to hide functionality (elastic#147429) [Fleet] Add agent policy `inactivity_timeout`experimental setting (elastic#147432) [APM] Switching service groups from grid to flex layout (elastic#147448) [Fleet] Add missing endpoints to openApi specs (elastic#147452) [AO] Allow providing custom time range for Alert Summary Widget (elastic#147253) ...
Summary
Note
This PR is adding changes only to some of
api/fleet/package_policiesAPI routes, there will be subsequent PRs after this to update
api/fleet/epm/packages,api/fleet/agent_policeisand,api/fleet/agent_status.This PR introduces the framework needed in fleet in order to be able to
support Package level Privileges - meaning: if a user does not have
authorization granted via Fleet and/or Integration privileges, then
package level privileges are check and API access granted. When access
is granted based on Package Privileges, the data is also validated to
ensure that it is limited to the integration package names that were
given authorization to the API.
The following APIs were updated to leverage this new framework:
Example of API error for Package policies api:
To test:
Log in as
elastic/superuser and create some agent policies.Under

Stack Management, create a rolepolicy_rolewith thefollowing RBAC settings. DO NOT select
Fleet -> Allor toggleIntegrations. Leave those RBAC toggles set toNoneCreate a user e.g.
policy_userand assign them only the aboverole. NOT
superuser.Login with this user and navigate to
app/security/administration/policyor curl/postman.Expect to see the following:
api/fleet/epm/packages?category=securityshould return a403status.
api/fleet/package_policies?page=1&perPage=10&kuery=ingest-package-policies.package.name%3A%20endpointshould return a list of policies.
/api/fleet/package_policies/<packagePolicyId>should return a200and a signle item that has the policie's details. Note that thepackage name of this item is
endpoint.api/fleet/agent_policies/_bulk_get, and should return a403.Policy ManagementRBAC set toAllhttp://localhost:5601/api/fleet/package_policies/<packagePolicyId>should return a
200with the updated policy details as responseChecklist
Unit or functional
tests
were updated or added to match the most common scenarios
This was checked for breaking API changes and was labeled
appropriately
Co-authored-by: Paul Tavares paul.tavares@elastic.co