This repository was archived by the owner on Feb 8, 2024. It is now read-only.
Merged
Conversation
|
@kimlisa suggested copy: Web UI Login Disabled - This Teleport Cluster requires that user private keys be stored on hardware authentication devices. Since these keys are not accessible by web browsers, Web UI login has been disabled. Please use Teleport Connect or tsh to log in. |
cc93fe3 to
7b5e033
Compare
Contributor
Author
|
friendly ping @JanKaczmarkiewicz @ryanclark |
JanKaczmarkiewicz
approved these changes
Oct 27, 2022
ryanclark
approved these changes
Oct 28, 2022
kimlisa
added a commit
that referenced
this pull request
Oct 28, 2022
There are three ways we determine if use of private key is enabled:
-Cluster config: this setting won't render the login form,
it will just direct user to login with other supported methods
- 'privateKeyPolicyEnabled' flag: only returned with a 200 for resets
and invites. This flag was required so that we can additionally render
recovery codes if any (only for Teleport Cloud)
- Checking if the error returned contains the backend hard coded
keywords ('hardware_key' or 'hardware_key_touch'). Role configs
will require an attempt (either logging in or assuming an access request)
before the backend checks if this user requires use of private keys.
2 tasks
kimlisa
added a commit
that referenced
this pull request
Nov 1, 2022
There are three ways we determine if use of private key is enabled:
-Cluster config: this setting won't render the login form,
it will just direct user to login with other supported methods
- 'privateKeyPolicyEnabled' flag: only returned with a 200 for resets
and invites. This flag was required so that we can additionally render
recovery codes if any (only for Teleport Cloud)
- Checking if the error returned contains the backend hard coded
keywords ('hardware_key' or 'hardware_key_touch'). Role configs
will require an attempt (either logging in or assuming an access request)
before the backend checks if this user requires use of private keys.
* Update e-ref
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to subscribe to this conversation on GitHub.
Already have an account?
Sign in.
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
resolves gravitational/teleport#16168
Description
There are three ways we determine if use of private key is enabled:
privateKeyPolicyEnabledflag: only returned with a 200 forresets and invites. This flag was required so that we can additionally render recovery codes if any (only for Teleport Cloud)hardware_keyorhardware_key_touch, this is used for:TODO
v11Test cases to add to test plan (added screenshots for UI and copy review)
Enforce use of private keys by cluster config or by role config.
Private key policy card should render for:
With a access request role that requires private key, a private key required dialogue pops up for:
access request listview access requestscreen(For waiting room, action button says
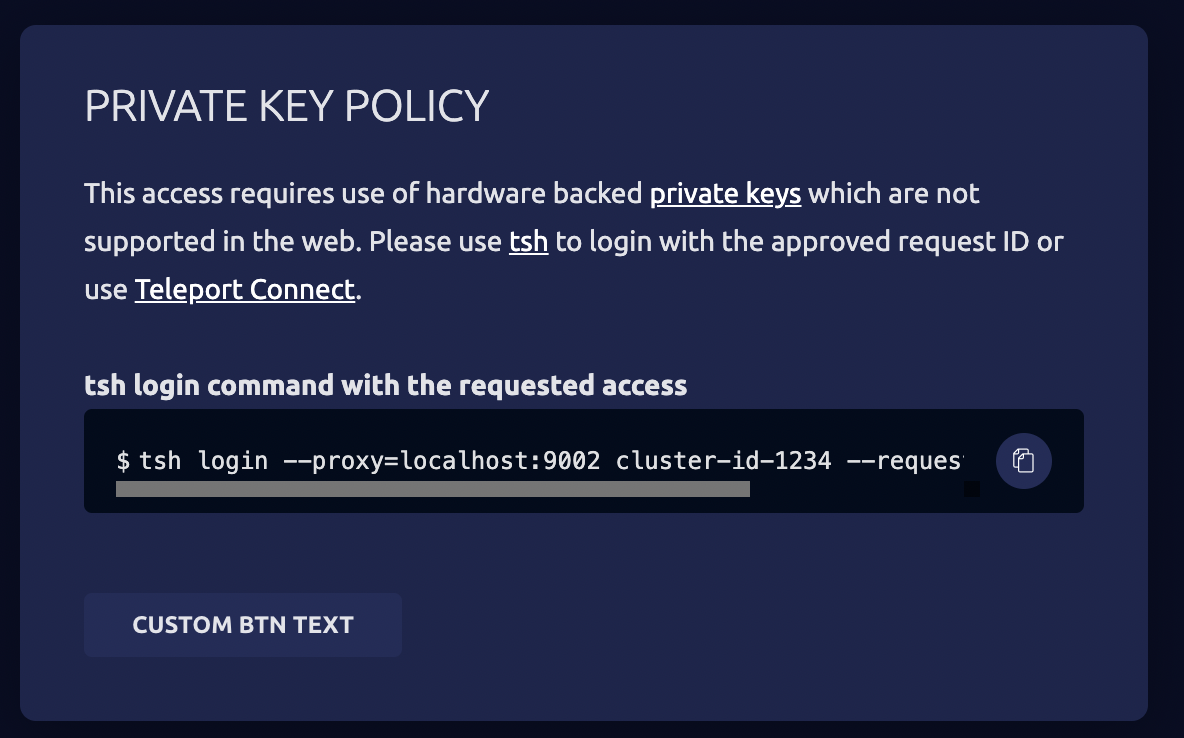
Logout, but when logged in and you get this error from trying to assume requests, the action button saysOkay)Below tests, it shouldn't matter if private key enforcement is set through cluster or role setting.
Private key policy card should render for Invites and Resets: