Revert "add extra role to be able to create gcp vms"#2147
Revert "add extra role to be able to create gcp vms"#2147k8s-ci-robot merged 1 commit intokubernetes:mainfrom
Conversation
There was a problem hiding this comment.
I would replace with ensure_removed_project_role_binding instead of deleting the line
And maybe try adding
ensure_serviceaccount_role_binding "${serviceaccount}" "serviceAccount:${serviceaccount}" "roles/iam.serviceAccountUser"
to see if my wild guess in #2124 (comment) is correct?
Running |
Fix exposure to privilege escalation introduced in kubernetes#2124. Signed-off-by: Arnaud Meukam <ameukam@gmail.com>
 spiffxp
left a comment
spiffxp
left a comment
There was a problem hiding this comment.
/approve
/lgtm
/hold
To remove when ready to deploy
|
[APPROVALNOTIFIER] This PR is APPROVED This pull-request has been approved by: ameukam, spiffxp The full list of commands accepted by this bot can be found here. The pull request process is described here DetailsNeeds approval from an approver in each of these files:
Approvers can indicate their approval by writing |
|
/hold cancel |
|
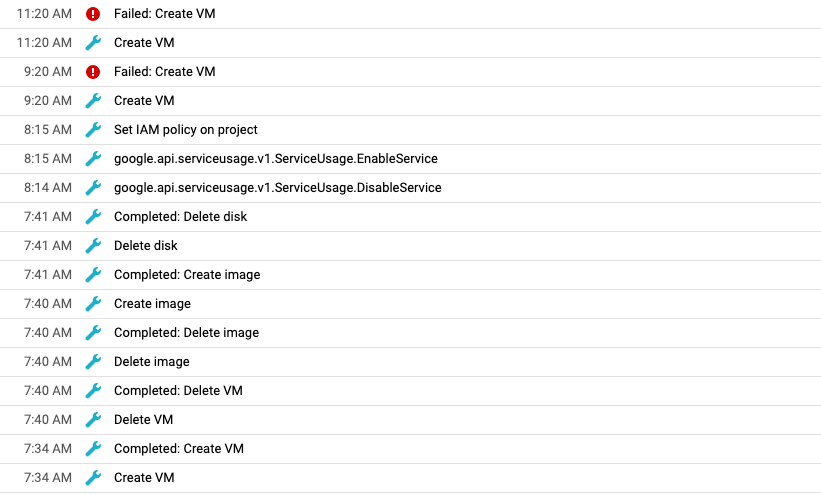
To help with troubleshooting I'm going to temporarily enable all Audit Logs (Admin Activity and Data Access) for IAM and Compute, via the console at https://console.cloud.google.com/iam-admin/audit?folder=&organizationId=&project=k8s-staging-cluster-api-gcp |
|
If set both we got I will set up only the service_account_email PR in image-builder: kubernetes-sigs/image-builder#641 |
Revert of #2124 which
introduces an exposure to privilege escalation.
Signed-off-by: Arnaud Meukam ameukam@gmail.com