Add Synology DSM Security API#35305
Conversation
|
Hey there @ProtoThis, mind taking a look at this pull request as its been labeled with a integration ( |
|
I'll look in detail when I have a free moment. #35106 |
|
OK, will check that tomorrow |
d172a53 to
acec2a6
Compare
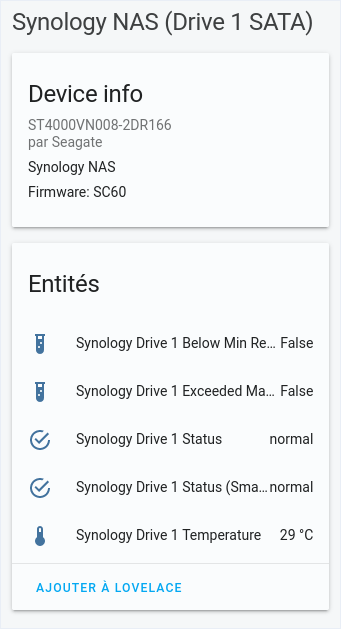
It takes several seconds to clean the device (was instant before), but it did clean automatically (I've created a "Synology NAS (security)" device for testing). |
acec2a6 to
36d3e35
Compare
36d3e35 to
ac56962
Compare
|
@Quentame Did you consider the Its fine to do it either way, but it might be easier to maintain. |
|
I did not consider But I after reading the doc I think it should be better for I prefer using option flow to prevent fetching an API we are not using. Concerning maintainability, I don't think this code is hard to read, but checking if all entries of a specific API is disabled to prevent fetching is gonna be harder. (maybe I'm wrong) |
| @property | ||
| def state(self): | ||
| """Return the state.""" | ||
| return getattr(self._api.security, self.sensor_type) |
There was a problem hiding this comment.
The state here is "safe", but maybe I should create a binary sensor of it instead of a sensor.
Like "Synology security safe" : on if safe, off if not, and maybe a details of it in attrs.
(I don't know all possible values)
What do you think @balloob ?
There was a problem hiding this comment.
I think you are spot on and it should be a binary sensor.
There was a problem hiding this comment.
binary sensor yes. There is even a safety device class :)
https://developers.home-assistant.io/docs/entity_binary_sensor#available-device-classes
Note that off means safe.
|
Next PR, see commit "Refactor Synology DSM device" : https://github.com/Quentame/home-assistant/commits/synology_dsm/platform-rework |
| vol.Optional( | ||
| CONF_SECURITY, | ||
| default=self.config_entry.options.get( | ||
| CONF_SECURITY, DEFAULT_SECURITY | ||
| ), | ||
| ): bool, |
There was a problem hiding this comment.
Agree with Nick. This should not be an option but just disabled by default.
There was a problem hiding this comment.
So you are ok to make a request to fetch security data even if we don't use it ?
There was a problem hiding this comment.
Searching to not make that with entity_registry_enabled_default
There was a problem hiding this comment.
Ideally the update function is smart enough to know that if it has no subscribers listening for the data that is should skip requesting those data sets.
There was a problem hiding this comment.
There was a problem hiding this comment.
@bdraco Yes, but in the case we have one DataUpdateCoordinator per API:
When requesting a storage fetch (and with a security coordinator somewhere) the lib update will fetch storage + security
After, the security DataUpdateCoordinator will also update with fetch storage + security.
So it doubles requests !
OR,
Every DataUpdateCoordinator should have its own instance of SynoApi or SynologyDSM, it will do even more requests and will login to the NAS for every DataUpdateCoordinator, I beat it will have an error at login (logged multiple times)
There was a problem hiding this comment.
You would need to some refactoring remove the the update and only have the coordinator instances for each endpoint share the single SynologyDSM so you aren't logging in multiple times.
There is a good example on how to accomplish this in nws/__init__.py:async_setup_entry
There was a problem hiding this comment.
If I turn off the security sensor
self._securitywill have already have been set here https://github.com/ProtoThis/python-synology/blob/674dfb3c943e464680c33c8bc4975139d8c72f5c/synology_dsm/synology_dsm.py#L297 so it going to continue to poll here https://github.com/ProtoThis/python-synology/blob/674dfb3c943e464680c33c8bc4975139d8c72f5c/synology_dsm/synology_dsm.py#L264
Yes totally, setting the sensor to off will make the API continue to fetch on it.
Your original approach of the option to turn on/off the sensor does eliminate this issue. The downside is that every new sensor type would have to be added to the options flow which will make it a lot more difficult to refactor later to tie specific sensors to specific api calls to avoid the ones that are disabled.
Not totally, one option per API, not per sensor.
Maybe, at SynoApi.async_update I can check all entities of this config, and if all entities of a specific API are disabled: something like this self.dsm._security = None.
@bdraco Do you know how to get all entities of one config ?
There was a problem hiding this comment.
Like this:
registry = await entity_registry.async_get_registry(hass)
conditions: List[Dict[str, Any]] = []
# Get all the integrations entities for this device
for entry in entity_registry.async_entries_for_device(registry, device_id):I suppose
EDIT: async_entries_for_config_entry
There was a problem hiding this comment.
Generally in this case we would want each entity to subscribe to updates and then we can look at the list of subscribers and determine which endpoints to poll. august/subscriber.py has an example
|
Closing in favor of #35565 |
Proposed change
Add security sensor via config options
Type of change
Additional information
Checklist
black --fast homeassistant tests)If user exposed functionality or configuration variables are added/changed:
If the code communicates with devices, web services, or third-party tools:
Updated and included derived files by running:
python3 -m script.hassfest.requirements_all.txt.Updated by running
python3 -m script.gen_requirements_all..coveragerc.The integration reached or maintains the following Integration Quality Scale: