Allow applications to register feature privileges which are excluded from the base privileges#41300
Conversation
…m-base-privileges
Prior to these changes, if we gave the user global base all and then a custom set of privileges at a space granting access to the reservedAndNormal feature, it'd show "All" for the space specific privileges.
💔 Build Failed |
…m-base-privileges
💚 Build Succeeded |
|
Reviewing today |
 legrego
left a comment
legrego
left a comment
There was a problem hiding this comment.
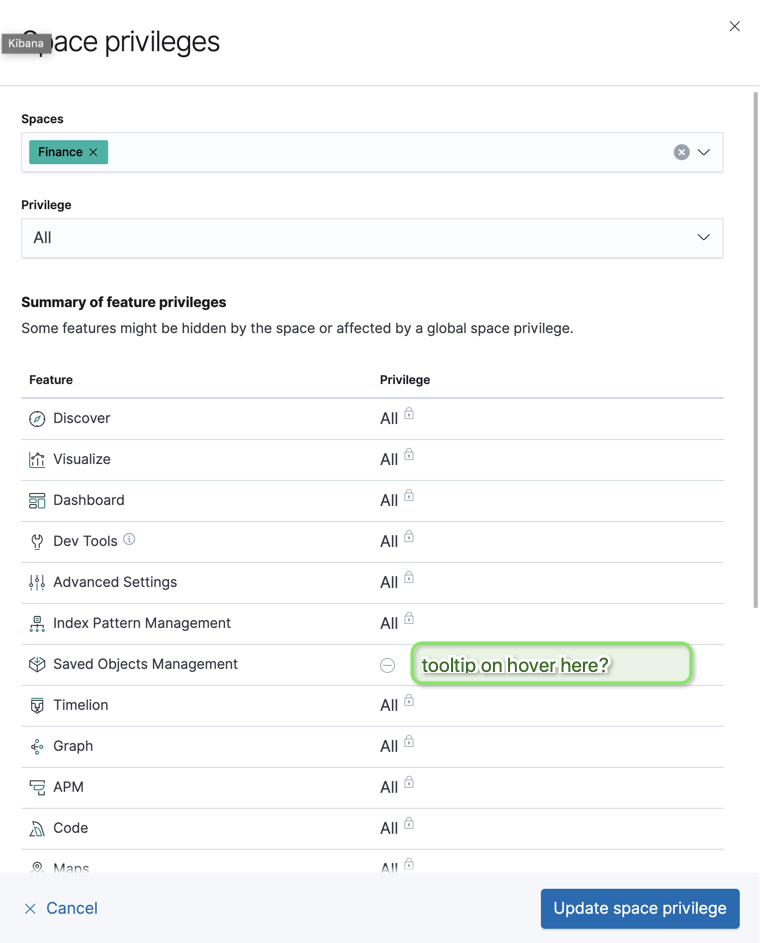
Small UI Bug:
There is logic in place which only lets users create/update a space privilege if there is something to actually save. It seems this is getting triggered when updating an existing privilege when setting the excluded feature to "None":
- Exclude any feature from the base privileges. I chose Saved Objects Management.
- On the create role screen, add a space-specific privilege, setting Saved Objects Management to either "all" or "read"
- Add the "Global base all" privilege
- Edit the space privilege from step 2, and try to set Saved Objects Management to "None"
Result:
The "Update space privilege" button is disabled, preventing edits.
Expected:
I could see this going one of two ways. Either allow the edit to take place, or prevent "None" from being a selectable option in this scenario. Thoughts?
…m-base-privileges
We currently have a similar experience without the changes this PR implements.
Since this is already an issue, I'd prefer we address this in a separate PR. |
|
@legrego I've added the tooltip that you suggested, ready for another review! |
💚 Build Succeeded |
| this.props.role.kibana[this.props.spacesIndex].base.length > 0; | ||
| const tooltipContent = | ||
| assignedBasePrivilege && actualPrivilegeValue === NO_PRIVILEGE_VALUE | ||
| ? `Use "Custom" to grant access. ${featureName} isn't part of the base privileges.` |
There was a problem hiding this comment.
We'll need to i18n'ify this string
There was a problem hiding this comment.
Good catch, I'll make it so.
💔 Build Failed |
💚 Build Succeeded |
 legrego
left a comment
legrego
left a comment
There was a problem hiding this comment.
LGTM once CI goes green against latest master
💔 Build Failed |
💚 Build Succeeded |
…from the base privileges (#41300) (#42300) * Allowing features with reserved and normal privileges to be listed * Allowing privileges to be excluded from the base privileges * Defaulting to custom when creating new privilege entries * Adjusting logic for the privilege space table and adding tests Prior to these changes, if we gave the user global base all and then a custom set of privileges at a space granting access to the reservedAndNormal feature, it'd show "All" for the space specific privileges. * Better naming for tests * Using a common rawKibanaPrivileges fixture * Rendering tooltip when feature isn't part of the base privileges * i18n'ing a string * Properly i18n'ing the string?
|
/cc @elastic/ml-ui |
…-or-edit-existing-rollup-job * 'master' of github.com:elastic/kibana: (114 commits) [ML] Fixing empty index pattern list (elastic#42299) [Markdown] Shim new platform - cleanup plugin (elastic#41760) [Code] Enable hierarchicalDocumentSymbolSupport for java language server (elastic#42233) Add New Platform mocks for data plugin (elastic#42261) Http server route handler implementation (elastic#41894) [SR] Allow custom index pattern to be used instead of selectable list when choosing indices to restore (elastic#41534) [Code] distributed Code abstraction (elastic#41374) [SIEM] Sets page titles to the current page you are on (elastic#42157) Saved Objects export API stable type order (elastic#42310) cancellation of interpreter execution (elastic#40238) [SIEM] Fixes a crash when Machine Learning influencers is an undefined value (elastic#42198) Changed the job to work with a dedicated index (elastic#42297) FTR: fix testSubjects.missingOrFail (elastic#42290) Increase retry timeout to prevent flaky tests (elastic#42291) Spaces - make space a hidden saved object type (elastic#41688) Allow applications to register feature privileges which are excluded from the base privileges (elastic#41300) Disable flaky log column reorder test (elastic#42285) Fixing add element in element reducer (elastic#42276) Fix infinite loop (elastic#42228) [Maps][File upload] Remove geojson deep clone logic, handle on maps side (elastic#41835) ...
Resolves #38571
#40073 implements the non-test changes as well with ML utilizing the
excludeFromBaseoption if you'd like to play around with the UI itself.