[Security Solution][Endpoint] Improve endpoint performance with TA wildcard paths#120349
Merged
ashokaditya merged 20 commits intoelastic:mainfrom Dec 16, 2021
Conversation
8d7340e to
06fb215
Compare
2e5a11d to
27fa87c
Compare
27fa87c to
da1d1be
Compare
da1d1be to
5757522
Compare
Contributor
|
Pinging @elastic/security-onboarding-and-lifecycle-mgt (Team:Onboarding and Lifecycle Mgt) |
Member
Author
|
@elasticmachine merge upstream |
review suggestions
…f github.com:ashokaditya/kibana into fix/olm-improve_endpoint_perf_with_TA_wildcards-2293
Member
Author
|
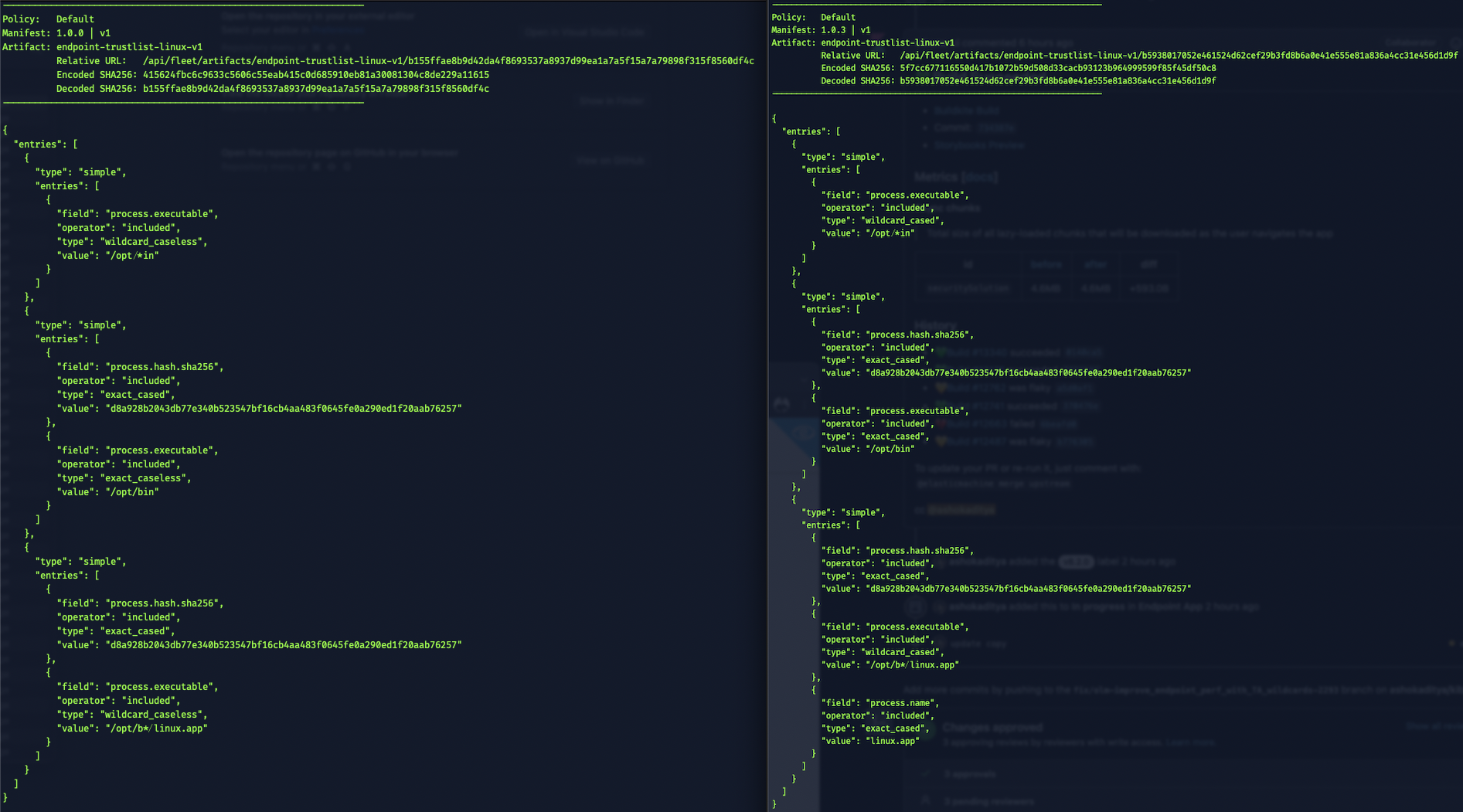
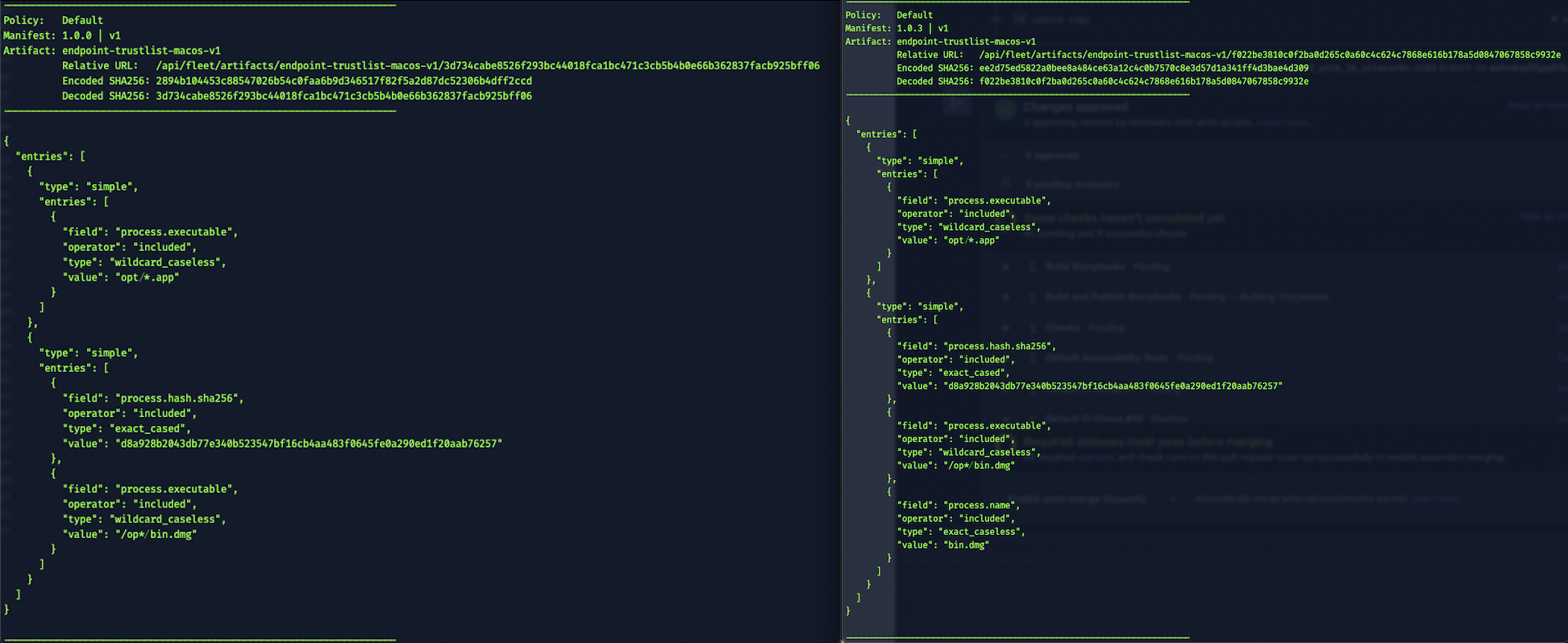
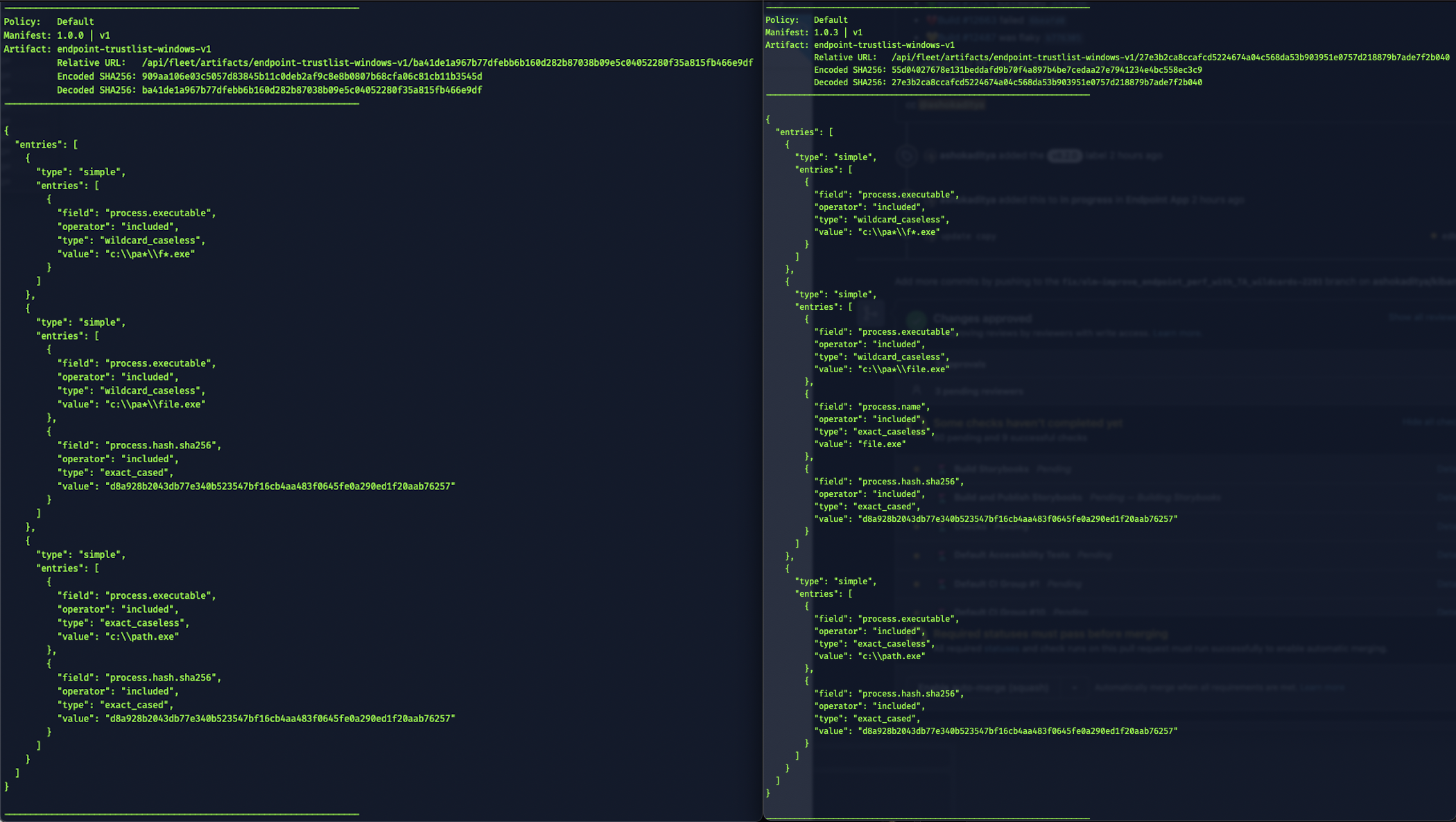
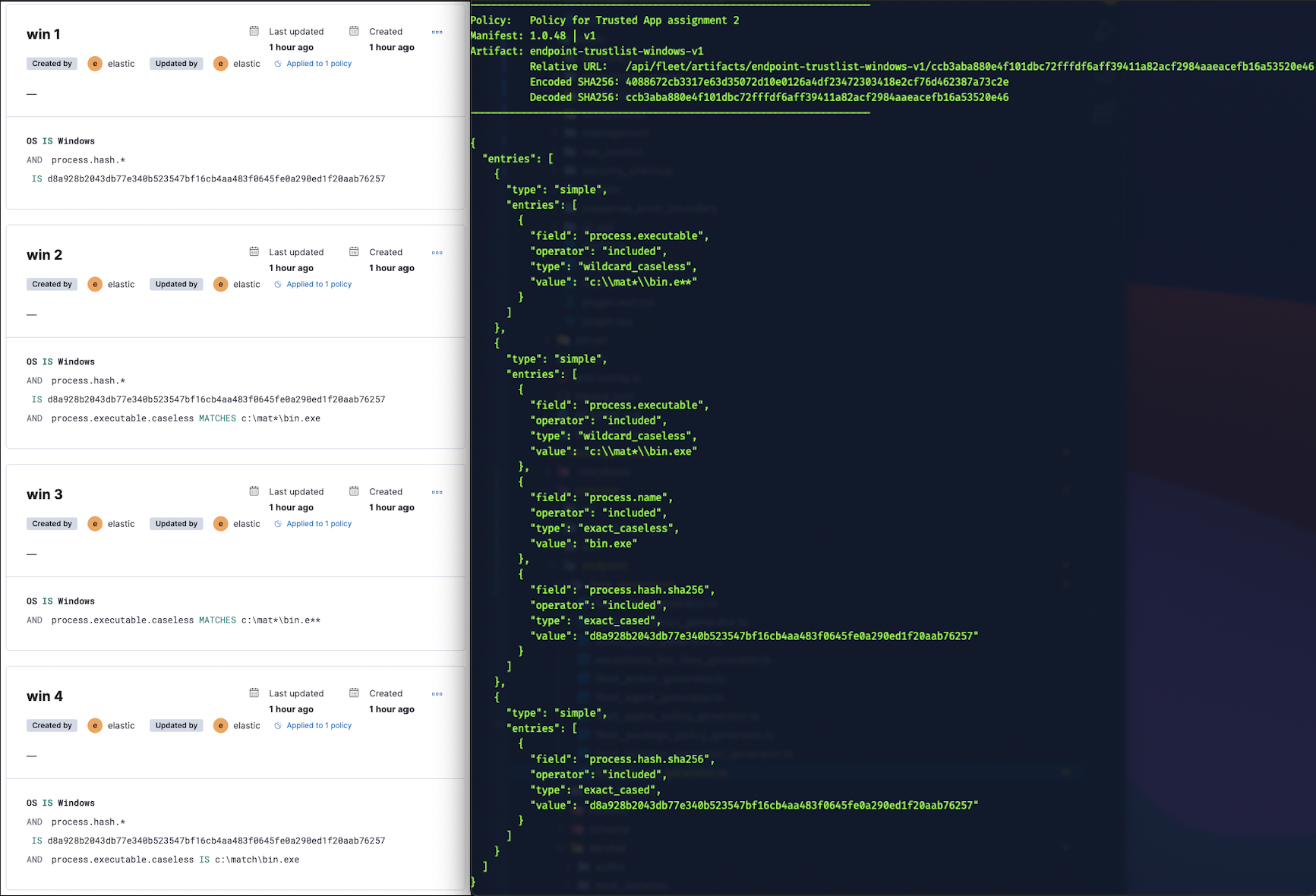
Tested this with artifacts (7.15.3 on left) |
💚 Build Succeeded
Metrics [docs]Async chunks
History
To update your PR or re-run it, just comment with: cc @ashokaditya |
Contributor
💔 Backport failed
To backport manually run: |
ashokaditya
added a commit
to ashokaditya/kibana
that referenced
this pull request
Dec 16, 2021
…ldcard paths (elastic#120349) * Show full executable names in placeholder for wildcard paths fixes elastic/security-team/issues/2293 * Show soft warning when wildcard also in executable names fixes elastic/security-team/issues/2293 * add wildcard path entries to fake TA list refs elastic/security-team/issues/2293 * Append a process.name entry when executable name in wildcard path fixes elastic/security-team/issues/2293 * commit using ashokaditya@elastic.co * linux should always use `_cased` types review changes * use better TS * use matcher functions to compute operator value for linux review suggestions * use path to extract filenames on server side review suggestions * improve regex for windows and unix filepaths review suggestions * update test mocks review changes * update regex to match multi spaces and single chars with spaces in filenames * add comment to explain review suggestions * update copy Co-authored-by: Kibana Machine <42973632+kibanamachine@users.noreply.github.com> # Conflicts: # x-pack/plugins/security_solution/public/management/pages/policy/view/trusted_apps/layout/policy_trusted_apps_layout.test.tsx
ashokaditya
added a commit
to ashokaditya/kibana
that referenced
this pull request
Dec 16, 2021
…ldcard paths (elastic#120349) * Show full executable names in placeholder for wildcard paths fixes elastic/security-team/issues/2293 * Show soft warning when wildcard also in executable names fixes elastic/security-team/issues/2293 * add wildcard path entries to fake TA list refs elastic/security-team/issues/2293 * Append a process.name entry when executable name in wildcard path fixes elastic/security-team/issues/2293 * commit using ashokaditya@elastic.co * linux should always use `_cased` types review changes * use better TS * use matcher functions to compute operator value for linux review suggestions * use path to extract filenames on server side review suggestions * improve regex for windows and unix filepaths review suggestions * update test mocks review changes * update regex to match multi spaces and single chars with spaces in filenames * add comment to explain review suggestions * update copy Co-authored-by: Kibana Machine <42973632+kibanamachine@users.noreply.github.com> # Conflicts: # x-pack/plugins/security_solution/common/endpoint/data_generators/exceptions_list_item_generator.ts # x-pack/plugins/security_solution/public/management/pages/mocks/trusted_apps_http_mocks.ts # x-pack/plugins/security_solution/public/management/pages/policy/view/trusted_apps/layout/policy_trusted_apps_layout.test.tsx # x-pack/plugins/security_solution/public/management/pages/trusted_apps/view/trusted_apps_page.test.tsx
ashokaditya
added a commit
that referenced
this pull request
Dec 16, 2021
…ldcard paths (#120349) (#121443) * Show full executable names in placeholder for wildcard paths fixes elastic/security-team/issues/2293 * Show soft warning when wildcard also in executable names fixes elastic/security-team/issues/2293 * add wildcard path entries to fake TA list refs elastic/security-team/issues/2293 * Append a process.name entry when executable name in wildcard path fixes elastic/security-team/issues/2293 * commit using ashokaditya@elastic.co * linux should always use `_cased` types review changes * use better TS * use matcher functions to compute operator value for linux review suggestions * use path to extract filenames on server side review suggestions * improve regex for windows and unix filepaths review suggestions * update test mocks review changes * update regex to match multi spaces and single chars with spaces in filenames * add comment to explain review suggestions * update copy Co-authored-by: Kibana Machine <42973632+kibanamachine@users.noreply.github.com> # Conflicts: # x-pack/plugins/security_solution/public/management/pages/policy/view/trusted_apps/layout/policy_trusted_apps_layout.test.tsx
ashokaditya
added a commit
that referenced
this pull request
Dec 16, 2021
…ldcard paths (#120349) (#121448) * Show full executable names in placeholder for wildcard paths fixes elastic/security-team/issues/2293 * Show soft warning when wildcard also in executable names fixes elastic/security-team/issues/2293 * add wildcard path entries to fake TA list refs elastic/security-team/issues/2293 * Append a process.name entry when executable name in wildcard path fixes elastic/security-team/issues/2293 * commit using ashokaditya@elastic.co * linux should always use `_cased` types review changes * use better TS * use matcher functions to compute operator value for linux review suggestions * use path to extract filenames on server side review suggestions * improve regex for windows and unix filepaths review suggestions * update test mocks review changes * update regex to match multi spaces and single chars with spaces in filenames * add comment to explain review suggestions * update copy Co-authored-by: Kibana Machine <42973632+kibanamachine@users.noreply.github.com> # Conflicts: # x-pack/plugins/security_solution/common/endpoint/data_generators/exceptions_list_item_generator.ts # x-pack/plugins/security_solution/public/management/pages/mocks/trusted_apps_http_mocks.ts # x-pack/plugins/security_solution/public/management/pages/policy/view/trusted_apps/layout/policy_trusted_apps_layout.test.tsx # x-pack/plugins/security_solution/public/management/pages/trusted_apps/view/trusted_apps_page.test.tsx
Closed
2 tasks
ashokaditya
added a commit
to ashokaditya/kibana
that referenced
this pull request
Mar 17, 2022
ashokaditya
added a commit
that referenced
this pull request
Mar 23, 2022
…wildcard) in wildcard-ed event filter `file.path.text` (#127432) * update filename regex to include multiple hyphens and periods Uses a much simpler pattern that covers a whole gamut file name patterns. fixes elastic/security-team/issues/3294 * remove duplicated code * add tests for `process.name` entry for filenames with wildcard path refs /pull/120349 /pull/125202 * Add file.name optimized entry when wildcard filepath in file.path.text has a filename fixes elastic/security-team/issues/3294 * update regex to include unicode chars review changes * add tests for `file.name` and `process.name` entries if it already exists This works out of the box and we don't add endpoint related `file.name` or `process.name` entry when it already is added by the user refs /pull/127958#discussion_r829086447 elastic/security-team/issues/3199 * fix `file.name` and `file.path.text` entries for linux and mac/linux refs /pull/127098 * do not add endpoint optimized entry Add `file.name` and `process.name` entry for wildcard path values only when file.name and process.name entries do not already exist. The earlier commit 8a516ae was mistakenly labeled as this worked out of the box. In the same commit we notice that the test data had a wildcard file path that did not add a `file.name` or `process.name` entry. For more see: /pull/127958#discussion_r829086447 elastic/security-team/issues/3199 * update regex to include gamut of unicode characters review suggestions * remove regex altogether simplifies the logic to check if path is without wildcard characters. This way it includes all other strings as valid filenames that do not have * or ? * update artifact creation for `file.path.text` entries Similar to when we normalize `file.path.caseless` entries, except that the `type` is `*_cased` for linux and `*_caseless` for non-linux
8 tasks
gergoabraham
added a commit
that referenced
this pull request
Dec 5, 2023
…on (#166002) ## Summary This PR adds `matches` (`wildcard include`) and `does not match` (`wildcard exclude`) to fields which support them when creating an Endpoint exception. For backwards compatibility with Endpoints < 8.2.0, Manifest Manager adds the following entry to Endpoint Exceptions containing _only_ wildcards: ```json { "field": "event.module", "operator": "included", "type": "exact_cased", "value": "endpoint" } ``` > [!Note] > Warnings for wrongly formatted wildcards don't seem to work correctly at the moment. #170495 will bring some changes in the related functions, so this PR is waiting on that to be merged. <img width="1465" alt="image" src="https://github.com/elastic/kibana/assets/39014407/db04fe0b-4cb3-4cba-a6d7-622a2239f059"> ## Sample manifests ### Linux⚠️ On Linux, the type is always `wildcard_cased`, see the following comment for details: #120349 (comment) ```json { "entries": [ { "type": "simple", "entries": [ { "field": "file.path", "operator": "included", "type": "wildcard_cased", "value": "*/test/*" }, { "field": "event.module", "operator": "included", "type": "exact_cased", "value": "endpoint" } ] } ] } ``` ### Windows ```json { "entries": [ { "type": "simple", "entries": [ { "field": "file.path", "operator": "included", "type": "wildcard_caseless", "value": "*/test/*" }, { "field": "event.module", "operator": "included", "type": "exact_cased", "value": "endpoint" } ] } ] } ``` ### Checklist Delete any items that are not applicable to this PR. - [ ] Any text added follows [EUI's writing guidelines](https://elastic.github.io/eui/#/guidelines/writing), uses sentence case text and includes [i18n support](https://github.com/elastic/kibana/blob/main/packages/kbn-i18n/README.md) - [ ] [Documentation](https://www.elastic.co/guide/en/kibana/master/development-documentation.html) was added for features that require explanation or tutorials - [ ] [Unit or functional tests](https://www.elastic.co/guide/en/kibana/master/development-tests.html) were updated or added to match the most common scenarios - [ ] Any UI touched in this PR is usable by keyboard only (learn more about [keyboard accessibility](https://webaim.org/techniques/keyboard/)) - [ ] Any UI touched in this PR does not create any new axe failures (run axe in browser: [FF](https://addons.mozilla.org/en-US/firefox/addon/axe-devtools/), [Chrome](https://chrome.google.com/webstore/detail/axe-web-accessibility-tes/lhdoppojpmngadmnindnejefpokejbdd?hl=en-US)) - [ ] If a plugin configuration key changed, check if it needs to be allowlisted in the cloud and added to the [docker list](https://github.com/elastic/kibana/blob/main/src/dev/build/tasks/os_packages/docker_generator/resources/base/bin/kibana-docker) - [ ] This renders correctly on smaller devices using a responsive layout. (You can test this [in your browser](https://www.browserstack.com/guide/responsive-testing-on-local-server)) - [ ] This was checked for [cross-browser compatibility](https://www.elastic.co/support/matrix#matrix_browsers)
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
Summary
Displays a soft warning when the matching path has wildcard executable name. If the wildcard path has a proper executable in the path then it adds a
process.namevalue to the TA artifact.Linux entries
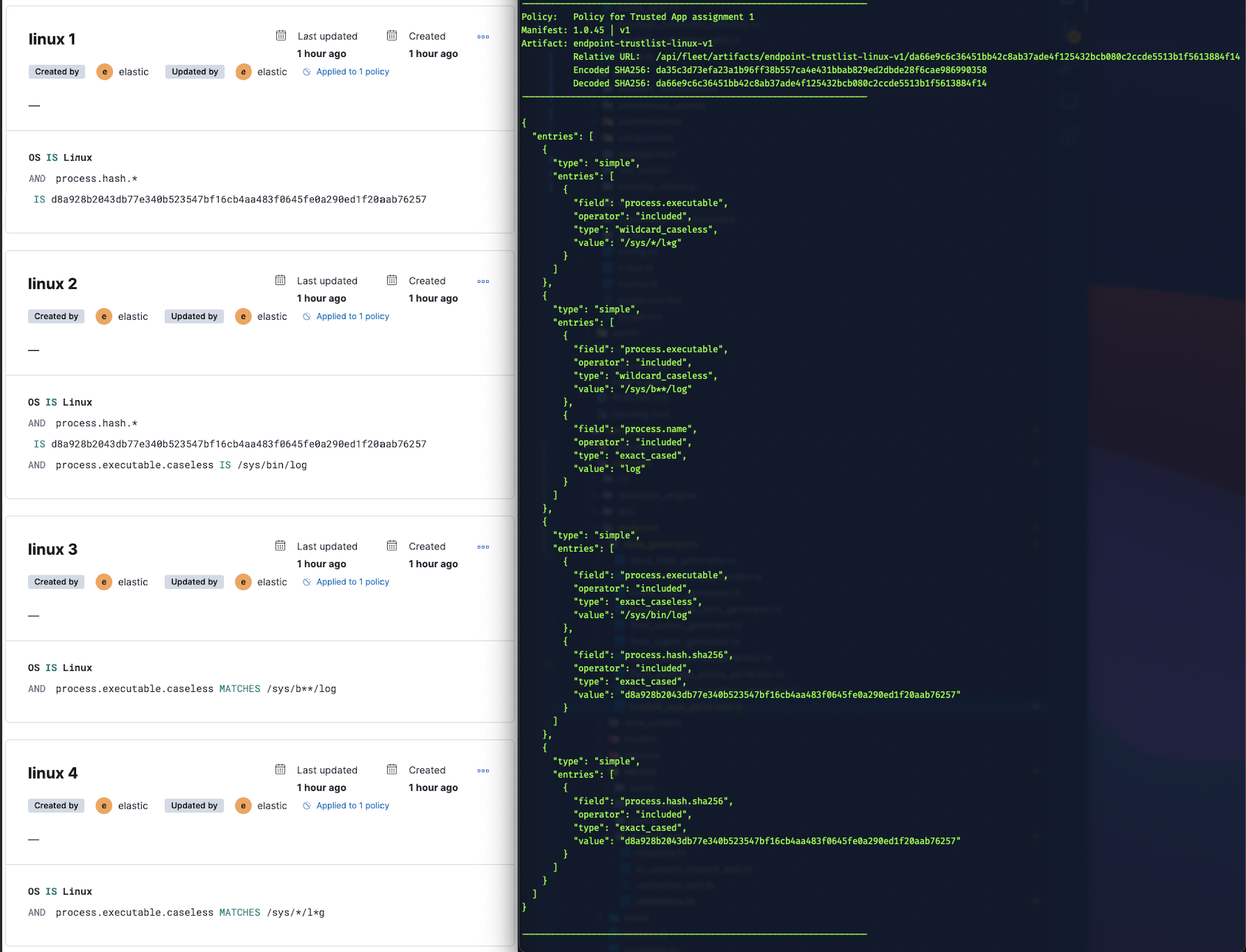
Mac entries

Windows entries
Checklist
Delete any items that are not applicable to this PR.
Risk Matrix
Delete this section if it is not applicable to this PR.
Before closing this PR, invite QA, stakeholders, and other developers to identify risks that should be tested prior to the change/feature release.
When forming the risk matrix, consider some of the following examples and how they may potentially impact the change: