[Security Solution] blocklist create/edit form#127098
Conversation
|
Still doing some cleanup, validation, and missing tests but functionally it's complete and works. Feel free to start reviewing. |
f97fdb0 to
77b13d6
Compare
|
Pinging @elastic/security-onboarding-and-lifecycle-mgt (Team:Onboarding and Lifecycle Mgt) |
|
still working on tests but everything works now so ready for review. |
94e471d to
b35b9bd
Compare
|
@joeypoon this is looking great! I checked it out and tried it. The basic functionality is there, I can add/edit/delete entries and the manifest creates the entries. I did find some issues. Width of
|
 paul-tavares
left a comment
paul-tavares
left a comment
There was a problem hiding this comment.
Left some feedback and will try to check this out tomorrow and run it locally.
Overall, I found the approach to keeping track of error/warning/visited a little confusing by storing it in a simple object with two properties that hold array's of React nodes, but lets see how others feel about that. I asked for a quick explanation on the Type you defined on how that data is used and what it holds
x-pack/plugins/security_solution/public/management/components/artifact_list_page/types.ts
Outdated
Show resolved
Hide resolved
...rity_solution/public/management/components/artifact_list_page/components/artifact_flyout.tsx
Outdated
Show resolved
Hide resolved
...rity_solution/public/management/components/artifact_list_page/components/artifact_flyout.tsx
Outdated
Show resolved
Hide resolved
...rity_solution/public/management/components/artifact_list_page/components/artifact_flyout.tsx
Outdated
Show resolved
Hide resolved
...rity_solution/public/management/components/artifact_list_page/components/artifact_flyout.tsx
Outdated
Show resolved
Hide resolved
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
There was a problem hiding this comment.
Why are these react nodes?
I'm also having a hard time understanding the fact that they are both arrays. What is stored in them exactly?
There was a problem hiding this comment.
helpText (warnings) and errors on EuiFormRow are typed as React.ReactNode[]. these are the actual warning/error messages we're passing directly into EuiFormRow.
There was a problem hiding this comment.
Ok. thanks for that. ReactNode alway accepts string, but Its ok to store JSX here if that is preferable.
Can you explain the relation ship between the array of nodes for name and the array of nodes for value in the same object? thats the part that is confusing me.
There was a problem hiding this comment.
I can probably have better naming here. the only places we need validation messages are on the name input and value input. the values under ItemValidation.name are all the validation messages for the name input and the values under ItemValidation.value are all the validation messages for the value input.
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
b35b9bd to
fcfa3cc
Compare
 dasansol92
left a comment
dasansol92
left a comment
There was a problem hiding this comment.
This is looking awesome! Left some questions/suggestions, let me know if anything is not clear at all 🙂
x-pack/plugins/security_solution/public/management/components/artifact_list_page/types.ts
Outdated
Show resolved
Hide resolved
packages/kbn-securitysolution-utils/src/path_validations/index.ts
Outdated
Show resolved
Hide resolved
x-pack/plugins/security_solution/common/utils/path_placeholder.test.ts
Outdated
Show resolved
Hide resolved
...rity_solution/public/management/components/artifact_list_page/components/artifact_flyout.tsx
Outdated
Show resolved
Hide resolved
x-pack/plugins/security_solution/public/management/pages/blocklist/view/blocklist.tsx
Outdated
Show resolved
Hide resolved
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
...ecurity_solution/public/management/pages/blocklist/view/components/create_blocklist_form.tsx
Outdated
Show resolved
Hide resolved
d3cc4ce to
69abec6
Compare
 ashokaditya
left a comment
ashokaditya
left a comment
There was a problem hiding this comment.
Look good so far.
I took it for a spin and I noticed a few things
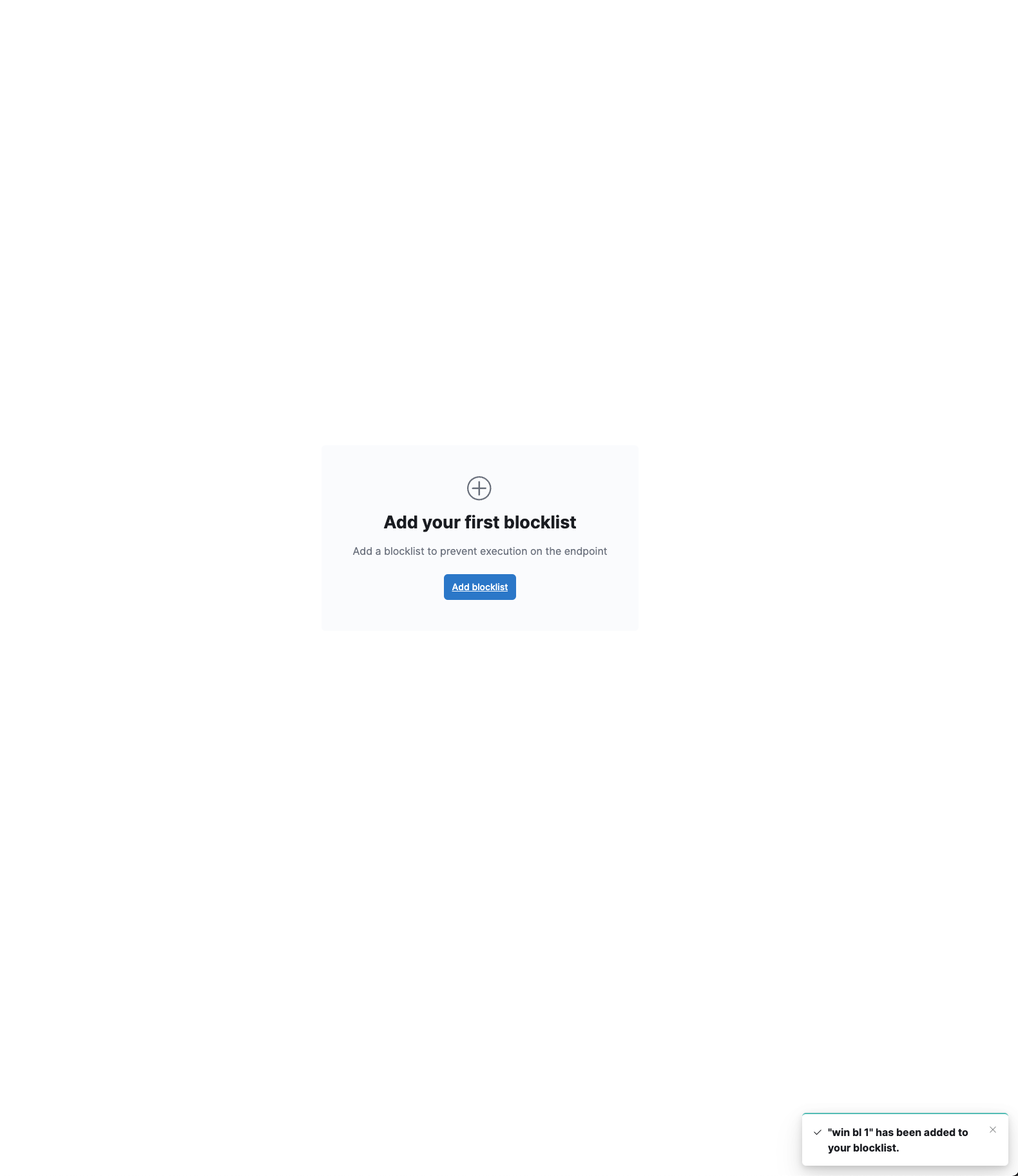
- upon creating a blocklist from the empty page, the item is added and a success toast is shown, but the entry doesn't show on the list page right away. It does show up on a refresh.
- Also, I could add an entry without a name.
- On editing the entry, changing the field from hash/signature (with its corresponding input value) to path doesn't trigger a warning. Same if you change to hash/signature from path. I would expect the same kind of warnings as we see in TA for field changes when input value already exists.
There was a problem hiding this comment.
Agree with @dasansol92. Better to keep this as a separate type from TA entry types. Besides blocklist expects only match_any for now and not the other two.
cde9d37 to
6bcf21a
Compare
5f9f492 to
e55a91f
Compare
|
linux manifest + policy edit selection fixed. noticed an issue with validation state being out of sync, looking into that now. |
There was a problem hiding this comment.
considered making this more extensible such as passing entry overrides or something but figured we shouldn't over-engineer it right now.
0c37ced to
429a6b7
Compare
 paul-tavares
left a comment
paul-tavares
left a comment
There was a problem hiding this comment.
🔥 🔥
This is awesome. Thanks for all the changes from the prior review. I left a few more, but nothing that should hold this from commit.
There was a problem hiding this comment.
maybe on next commit, consider renaming this to isLoadingPolicies instead?
There was a problem hiding this comment.
I would like @dasansol92 comment here.
Ideally , we should not have read/write transforms in this base class because it should all be using ExceptionListItemSchema and so there should be no need for transformation of data. I understand from our discussion over slack that this was in response to the UI using just a hash field for the user to enter any of the supported hashes, which we then calculate the field name based on the value entered (ex. process.hash.md5|sha1|sha256).
I'm just not sure if pushing that data value manipulation down to the API service is the right thing to do - to me, it feels move like a UI component prop type of mapping when setting/reading the value the user entered.
That being said, having a "middleware" callback for read/write is not a bad idea, so I'm 👍 this for now. We should really discuss if we want to continue to use those TrustedApp** types, since we have been trying to remove all of them in support of only ExceptionListItemSchema
(FYI: the mappers you moved around were originally in the server API for trusted apps, but moved to the UI when we deleted the TA specific API and started using the List Exceptions API. Our intent was to then have a second pass through to delete all of the types and adjust TA to be just like every other artifact)
cc/ @ashokaditya since he also recently moved around some TA types to the @kbn/** library
There was a problem hiding this comment.
After thinking a bit more about it and after reading the comment above, I'm agree with what @paul-tavares has written.
As this is needed for UI maybe would be better to have it in an upper level. Also, we have plans to remove this types so we can just add this on that removal plan.
I would say let's move forward with this approach but let's take note about it in order to move/remove it when we get rid of the TA types.
PS: I like the way @joeypoon included this as a kind of hooks in this class. Let's keep this in mind for future pre/post validations, modifications, transformations, etc in frontend side.
|
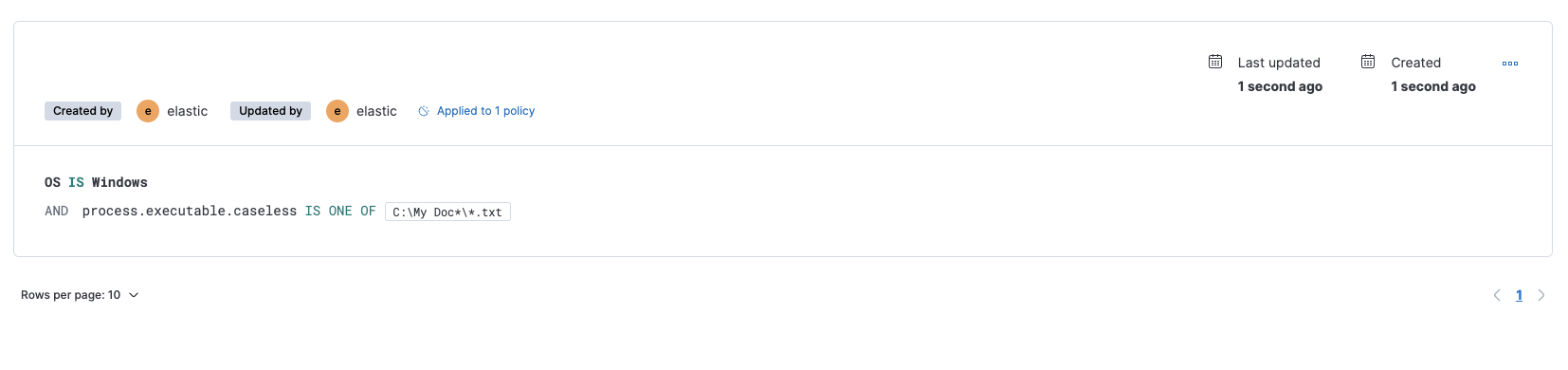
check it out again and the earlier issues are resolved! ✅ Process path entries for Linux should be I am now seeing {
"entries": [
{
"type": "simple",
"entries": [
{
"field": "process.executable",
"operator": "included",
"type": "exact_cased_any",
"value": [
"/usr/bin"
]
}
]
}
]
}and Windows paths are also correct: {
"entries": [
{
"type": "simple",
"entries": [
{
"field": "process.executable",
"operator": "included",
"type": "exact_caseless_any",
"value": [
"C:\\Name\\Name"
]
}
]
}
]
}✅ Policy selection on Edit |
429a6b7 to
672faf1
Compare
I like this idea. I bumped it up to L size along with test fix. |
672faf1 to
7422451
Compare
7422451 to
641f261
Compare
|
@elasticmachine merge upstream |
💚 Build SucceededMetrics [docs]Module Count
Public APIs missing comments
Async chunks
Page load bundle
History
To update your PR or re-run it, just comment with: |
…wildcard) in wildcard-ed event filter `file.path.text` (#127432) * update filename regex to include multiple hyphens and periods Uses a much simpler pattern that covers a whole gamut file name patterns. fixes elastic/security-team/issues/3294 * remove duplicated code * add tests for `process.name` entry for filenames with wildcard path refs /pull/120349 /pull/125202 * Add file.name optimized entry when wildcard filepath in file.path.text has a filename fixes elastic/security-team/issues/3294 * update regex to include unicode chars review changes * add tests for `file.name` and `process.name` entries if it already exists This works out of the box and we don't add endpoint related `file.name` or `process.name` entry when it already is added by the user refs /pull/127958#discussion_r829086447 elastic/security-team/issues/3199 * fix `file.name` and `file.path.text` entries for linux and mac/linux refs /pull/127098 * do not add endpoint optimized entry Add `file.name` and `process.name` entry for wildcard path values only when file.name and process.name entries do not already exist. The earlier commit 8a516ae was mistakenly labeled as this worked out of the box. In the same commit we notice that the test data had a wildcard file path that did not add a `file.name` or `process.name` entry. For more see: /pull/127958#discussion_r829086447 elastic/security-team/issues/3199 * update regex to include gamut of unicode characters review suggestions * remove regex altogether simplifies the logic to check if path is without wildcard characters. This way it includes all other strings as valid filenames that do not have * or ? * update artifact creation for `file.path.text` entries Similar to when we normalize `file.path.caseless` entries, except that the `type` is `*_cased` for linux and `*_caseless` for non-linux
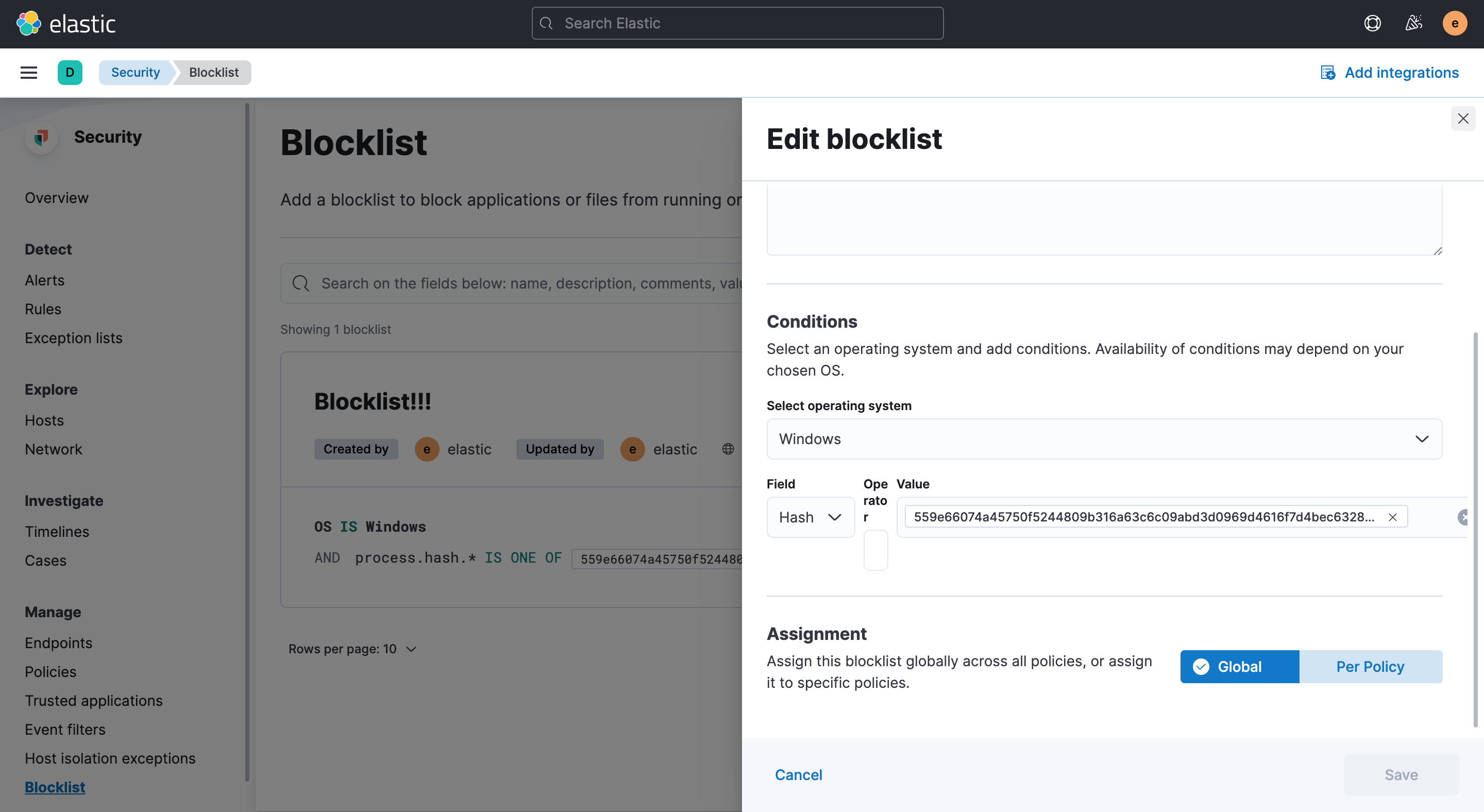
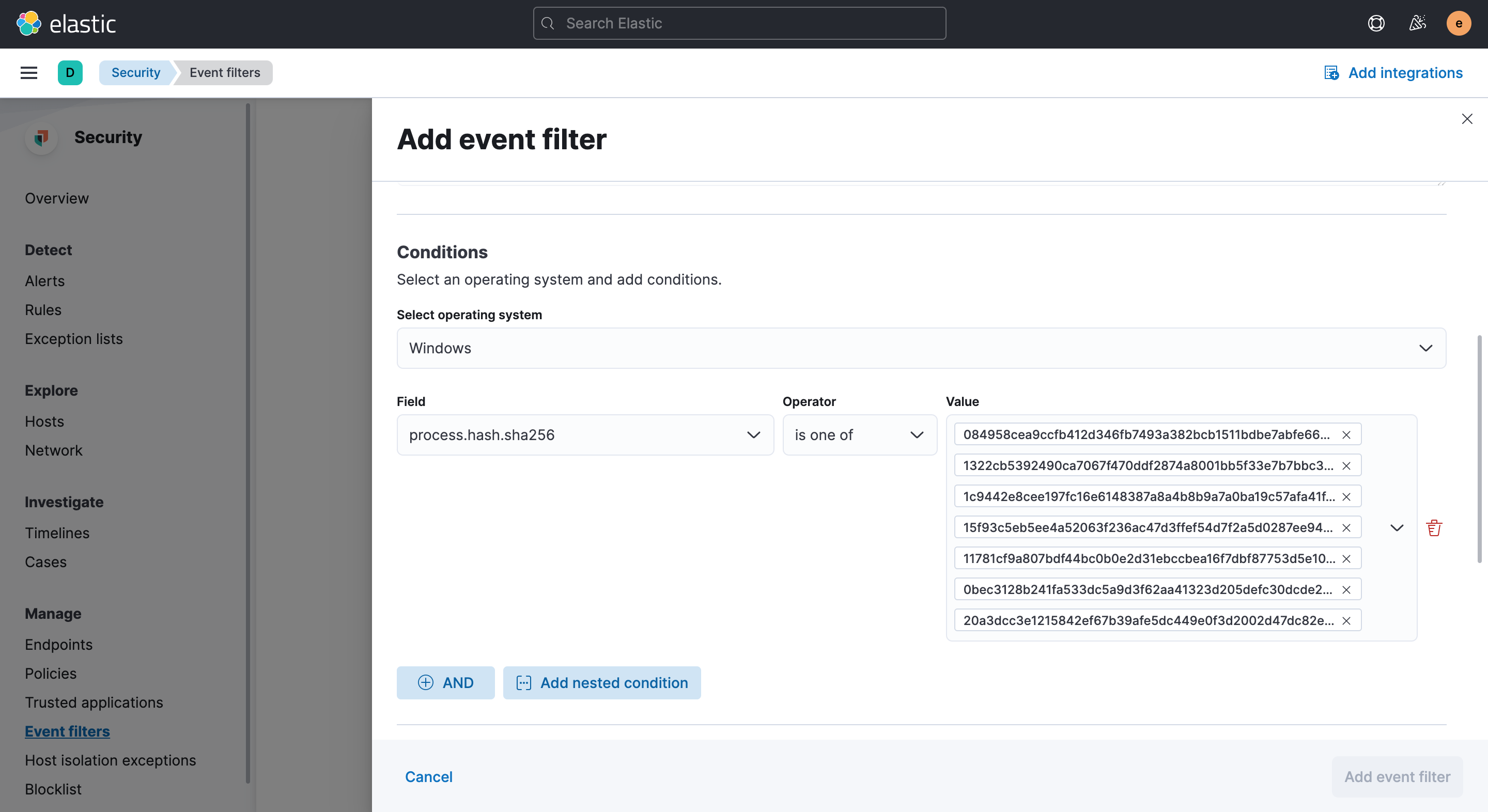
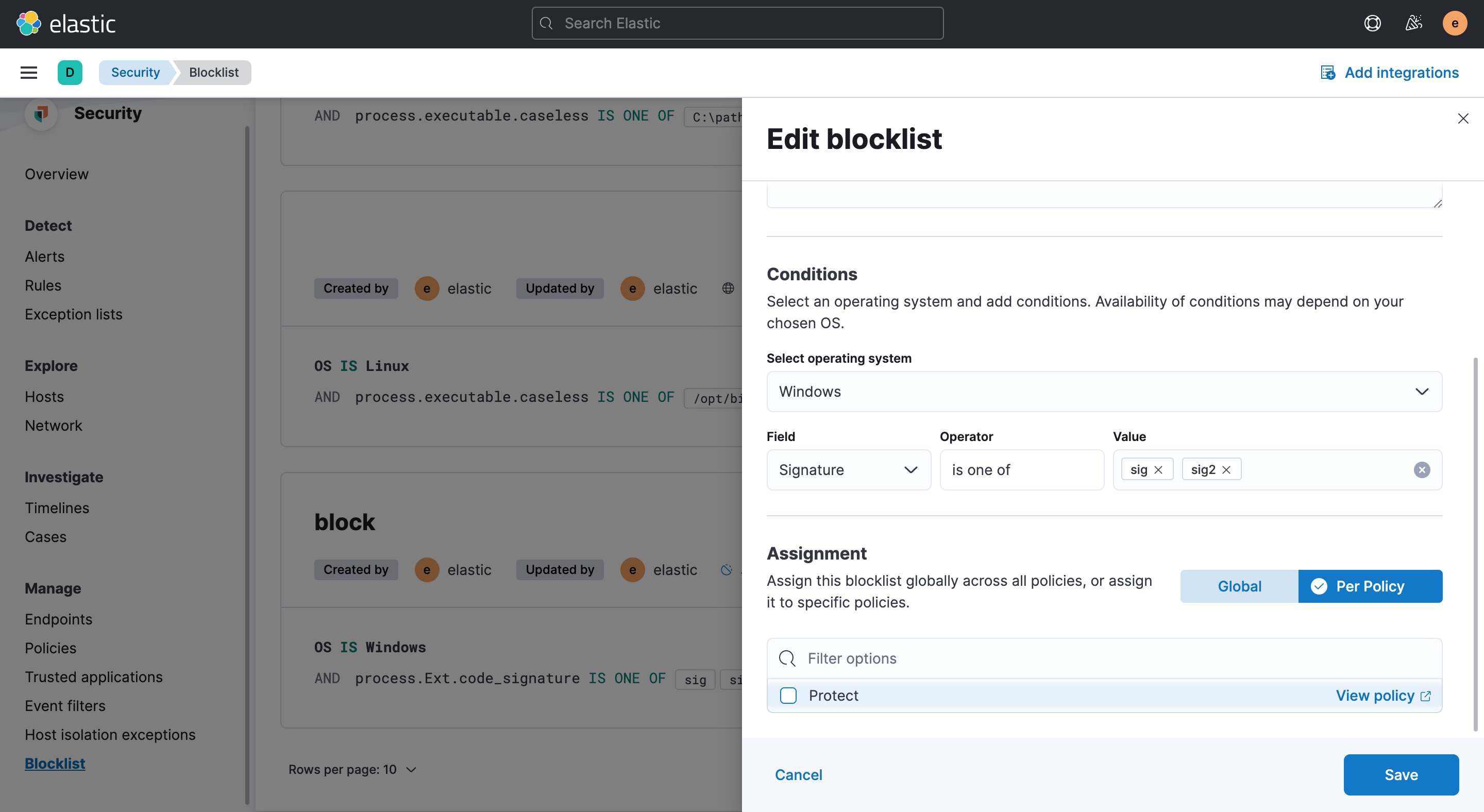
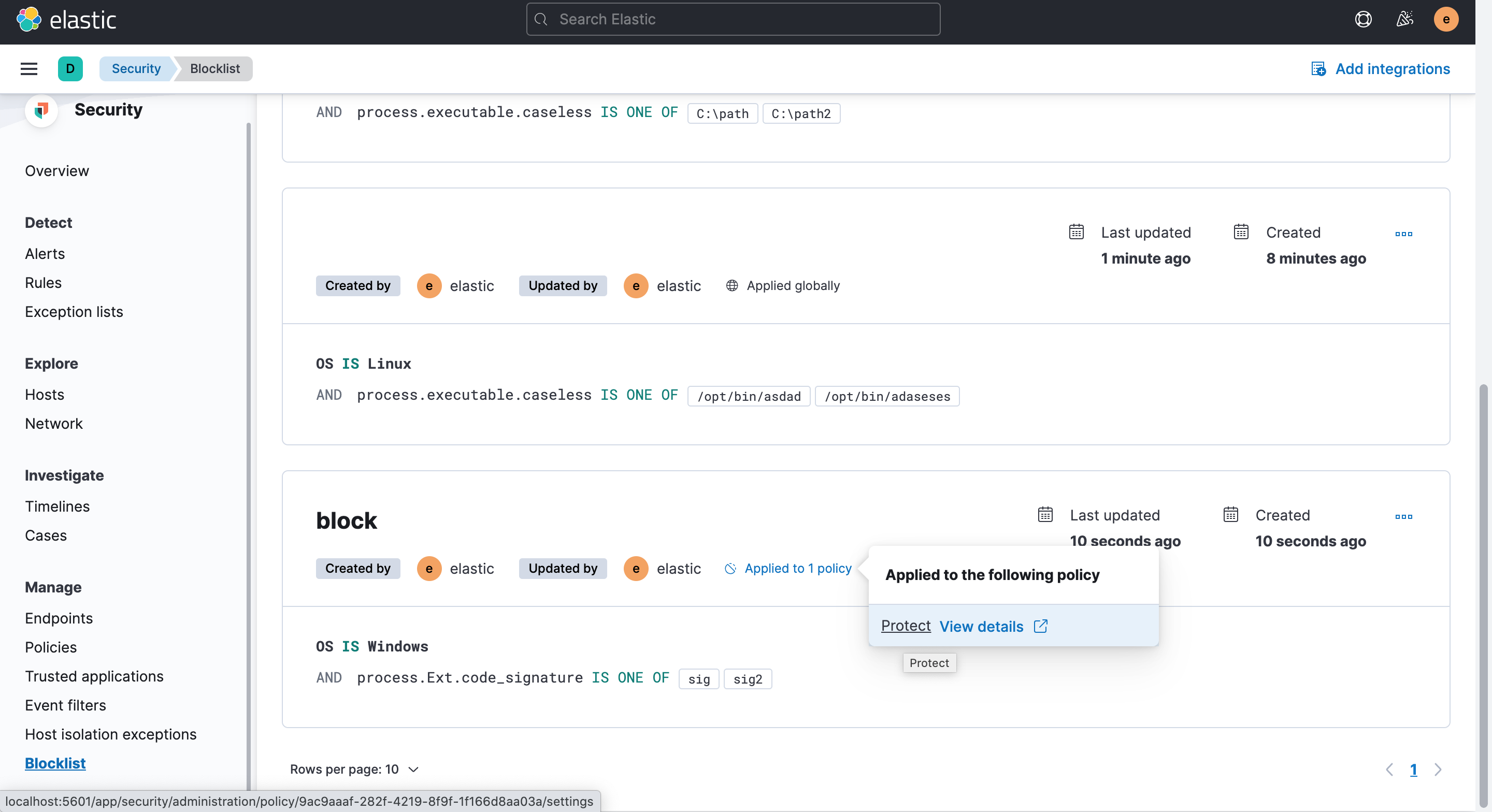
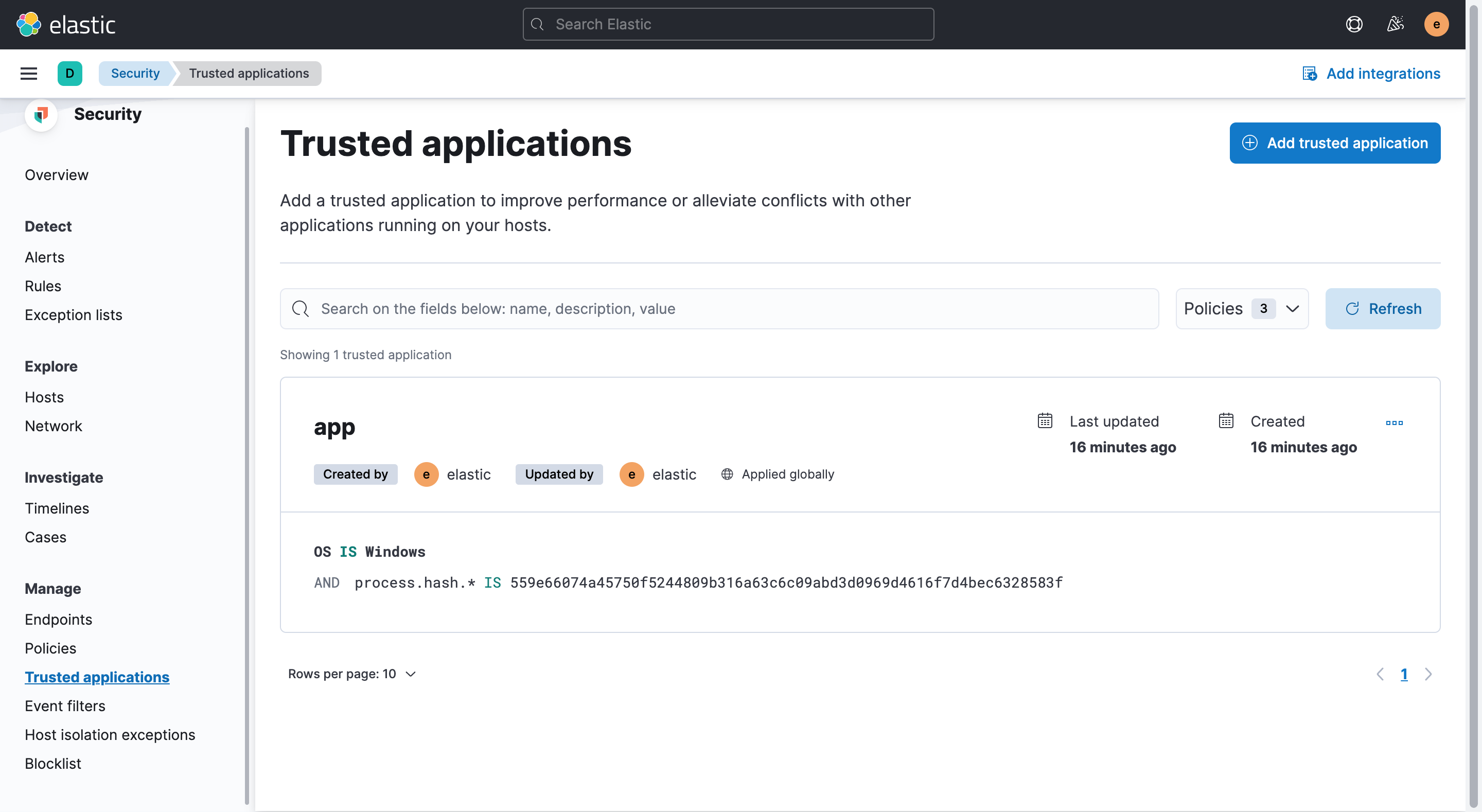
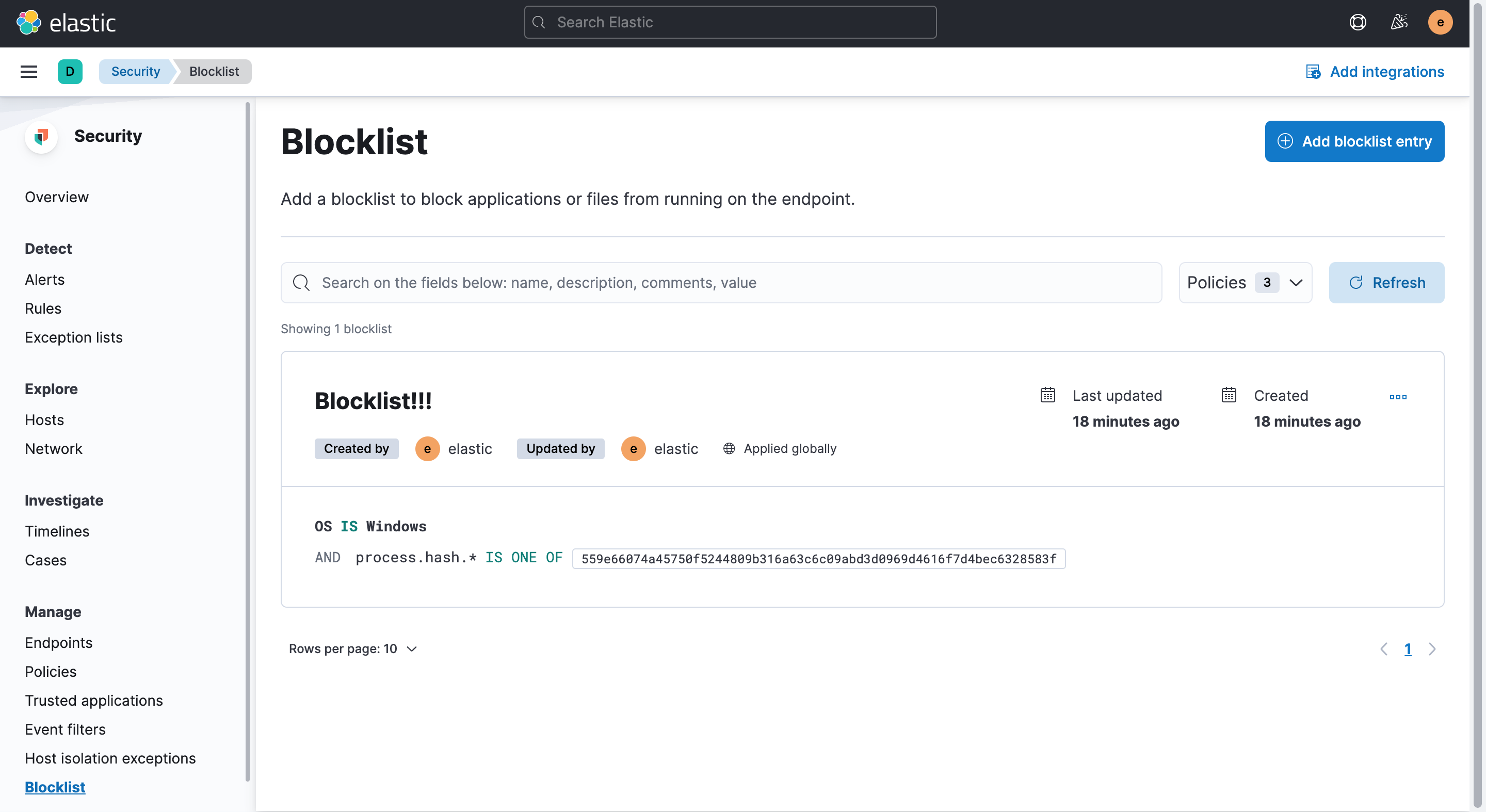
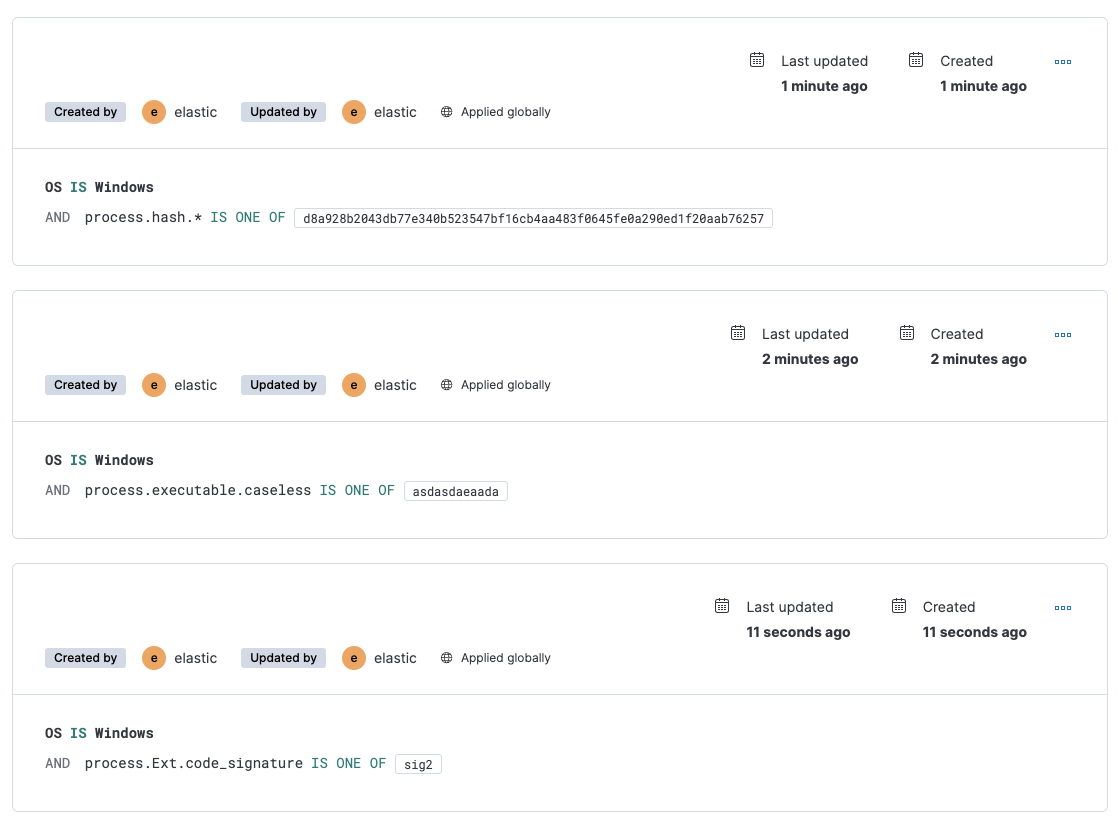
Summary
Add blocklist create/edit form.
Checklist
Delete any items that are not applicable to this PR.
For maintainers