For pushing ibm-vpc-csi-driver images#2618
Conversation
|
@nikhita @thockin Not sure the reason for below error Could you please help me find what went wring in the commit |
infra/gcp/infra.yaml
Outdated
| k8s-staging-storage-migrator: | ||
| k8s-staging-test-infra: | ||
| k8s-staging-txtdirect: | ||
| k8s-staging-cloud-provider-ibm: |
There was a problem hiding this comment.
@ambiknai Please, respect the alphabetic order of this list.
There was a problem hiding this comment.
I have moved it as per this comment.
|
/lgtm |
|
/assign @cblecker |
|
/lgtm |
|
/approve |
|
[APPROVALNOTIFIER] This PR is APPROVED This pull-request has been approved by: ambiknai, ameukam, arahamad, spiffxp The full list of commands accepted by this bot can be found here. The pull request process is described here DetailsNeeds approval from an approver in each of these files:
Approvers can indicate their approval by writing |
|
@spiffxp Thanks for approving the PR |
|
@ameukam shouldnt it be Not sure if I missed something here. I just changed the above url to point to |
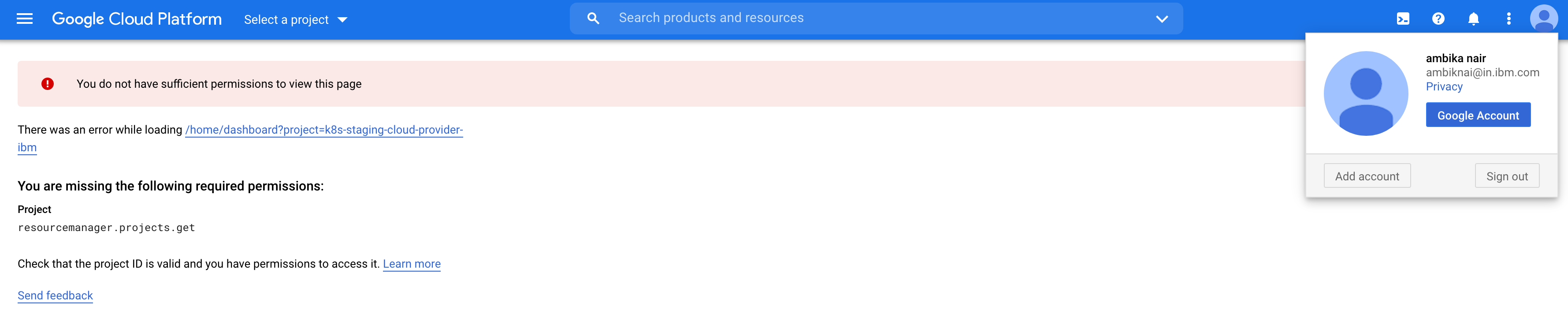
@ambiknai Sorry wrong project ID: https://console.cloud.google.com/home/dashboard?project=k8s-staging-cloud-provider-ibm. |
But I dont have permission as shared in screenshot. |
|
Forgot to mention earlier I ran It's possible the groups reconciliation didn't happen for |
|
@ameukam Ok. So how can this be fixed. I still don't see project in my dashboard |
|
Somehow when I ran I'm re-running for all staging projects now just to make sure everything is up to date, and I caught this. You should be good to go now |
No description provided.