capg/nightly: remove check credentials#625
capg/nightly: remove check credentials#625k8s-ci-robot merged 1 commit intokubernetes-sigs:masterfrom
Conversation
|
/approve |
|
Steps I did to simulate the prow job using this PR change
It starts to run but then failed because
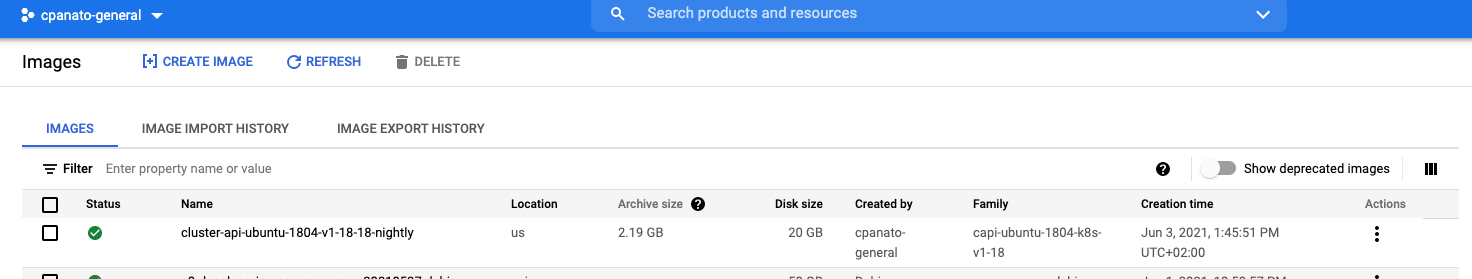
some snippet of the logs We need this PR to get in + a new role for the service account in k/k8s.io which I can add next here the screenshot of one image created |
|
/test pull-azure-vhds |
|
/retest |
1 similar comment
|
/retest |
|
/retest |
|
all green now @codenrhoden /hold cancel |
|
/approve |
|
[APPROVALNOTIFIER] This PR is APPROVED This pull-request has been approved by: codenrhoden, cpanato, dims The full list of commands accepted by this bot can be found here. The pull request process is described here DetailsNeeds approval from an approver in each of these files:
Approvers can indicate their approval by writing |
|
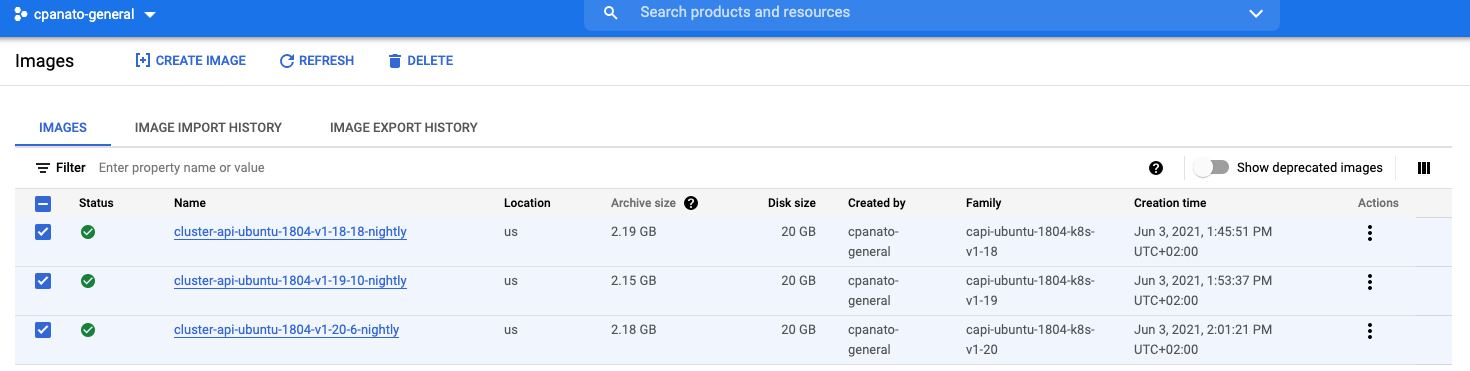
@cpanato Images are successfully built: gcloud compute images list --filter=\"family=capi-ubuntu-1804-k8s-\" --filter="name~^cluster-api" --format="value(name)" --project=k8s-staging-cluster-api-gcp
cluster-api-ubuntu-1804-v1-18-18-nightly
cluster-api-ubuntu-1804-v1-19-10-nightly
cluster-api-ubuntu-1804-v1-20-6-nightly |
|
I have a security concern with the way the k8s-infra role was assigned, ref: kubernetes/k8s.io#2124 (comment) Which specific service account needs to be used? We should be binding the role against that. Not the whole project |
|
lets address the issues in this discussion here: kubernetes/k8s.io#2124 (comment) and get that fixed. there are other things I would like to do after this, like make the images public, so we can use in the CAPG jobs and avoid to recreate that everytime |
What this PR does / why we need it:
Trying to setup the job to run the image builds for CAPG.
The nightly job: https://github.com/kubernetes/test-infra/blob/master/config/jobs/kubernetes/wg-k8s-infra/trusted/image-builder/image-builder-periodics.yaml uses a service account so in theory, we don't need to expected the
GOOGLE_APPLICATION_CREDENTIALSwill be injected.Per this document: https://github.com/kubernetes/test-infra/tree/master/workload-identity#pods we can just use it
but not sure if require more changes here or in the job definition. This is a debug PR to check.
I will try to set up something similar using my personal account and see if I can simulate a similar thing.
/assign @dims @ameukam @codenrhoden @spiffxp
Which issue(s) this PR fixes (optional, in fixes #(, fixes #<issue_number>, ...) format, will close the issue(s) when PR gets merged): Fixes #
Additional context
Add any other context for the reviewers