[Connect] Add Document Access Requests#1203
Conversation
|
Sorry for the messy commit history. Had some weird submodule issues and merge conflicts so ended up nuking my local and bringing changes over. |
| }); | ||
| } | ||
|
|
||
| export function makeResourceID({ |
There was a problem hiding this comment.
I'd inline this function :)
| export type ReviewAccessRequestParams = { | ||
| state: string; | ||
| reason: string; | ||
| roles: [string]; |
There was a problem hiding this comment.
I think you meant string[]
| width: '100%', | ||
| })} | ||
| > | ||
| <DialogHeader justifyContent="space-between" mb={0}> |
There was a problem hiding this comment.
We should have a simpler DialogConfirmation component... it is a lot of code to just show confirmation.
But this is out of scope for this PR.
| const rootClusterUri = workspacesService.getRootClusterUri(); | ||
| const accessRequestsService = | ||
| workspacesService.getWorkspaceAccessRequestsService(rootClusterUri); |
There was a problem hiding this comment.
Can be replaced with workspacesService.getActiveWorkspaceAccessRequestsService() (also in lines 42-44)
| draftState: (draft: { | ||
| isAccessRequestsBarCollapsed: boolean; | ||
| pendingAccessRequest: PendingAccessRequest; | ||
| assumed: Record<string, AccessRequest>; |
There was a problem hiding this comment.
Hmm is there any benefit of saving access requests in an object instead of an array? Because of that we have to use Object.keys() in a lot of places.
There was a problem hiding this comment.
I thought about this same thing tbh. I believe its because when adding a resource, we must check the type + name since the name isn't guaranteed to be unique (imagine a node named teleport and a db named teleport), however, I am storing by the ID anyway and I'm not sure it has the same issue? Sort of a relic of the past but, either either Object.keys in places, or array.filter/map in others to get counts+types in other places.
There was a problem hiding this comment.
So the key has structure type-resourceName?
| const changeSelectedClusterWarning = | ||
| 'Resources from different clusters cannot be combined in an access request. Current items selected will be cleared. Are you sure you want to continue?'; | ||
|
|
||
| export default function ChangeResourceDialog({ |
There was a problem hiding this comment.
This component is used with a name <ConfirmChangeDialog> and sits inside ConfirmClusterChangeDialog.tsx, that's a bit confusing :p
Using one name will improve readability.
| Object.keys(pendingAccessRequest.node).length + | ||
| Object.keys(pendingAccessRequest.db).length + | ||
| Object.keys(pendingAccessRequest.app).length + | ||
| Object.keys(pendingAccessRequest.kube_cluster).length + | ||
| Object.keys(pendingAccessRequest.windows_desktop).length; |
There was a problem hiding this comment.
The same code we have in useAccessRequestsButton. I'd see it in the accessRequestsService.
|
|
||
| import { NavigationItem } from './NavigationItem'; | ||
|
|
||
| export function NavigationMenuContainer() { |
There was a problem hiding this comment.
Is this component needed? I'd use early return in NavigationMenu if activeRootCluster is empty.
| if (!docService) { | ||
| return; | ||
| } | ||
| const doc = docService.createAccessRequestDocument({ clusterUri, state }); | ||
| docService.add(doc); | ||
| docService.open(doc.uri); |
There was a problem hiding this comment.
This logic should live in navigationItems:
{
title: 'New Access Request',
Icon: <Add fontSize={2} />
onNavigate: () => {...}
},NavigationItem doesn't need to know about docService or anything like that.
There was a problem hiding this comment.
I agree, because we may need to do something special per item eventually. How is navigationItems supposed to be aware of the doc service? I'm a bit lost there, can you point to an existing pattern similar to this?
There was a problem hiding this comment.
I'm thinking about something like this:
function getNavigationItems(documentsService: DocumentsService): {
title: string;
Icon: JSX.Element;
onNavigate(): void;
}[] {
return [
{
title: 'New Access Request',
Icon: <Add fontSize={2} />,
onNavigate: () => documentsService.open(....),
},
{
title: 'Review Access Requests',
Icon: <OpenBox fontSize={2} />,
onNavigate: () => documentsService.open(....)
},
]};and then:
<Flex flexDirection="column">
{getNavigationItems(documentsService).map((item, index) => (There was a problem hiding this comment.
This is awesome thank you. yes, absolutely the best path to go with.
There was a problem hiding this comment.
This came out great! Wonderful suggestion
| }; | ||
|
|
||
| export type ReviewAccessRequestParams = { | ||
| state: string; |
There was a problem hiding this comment.
What are the possible states?
| { | ||
| title: 'New Access Request', | ||
| Icon: <Add fontSize={2} />, | ||
| state: 'creating', | ||
| }, | ||
| { | ||
| title: 'Review Access Requests', | ||
| Icon: <OpenBox fontSize={2} />, | ||
| state: 'reviewing', | ||
| }, |
There was a problem hiding this comment.
Re: feature detection in Connect, do we plan to do that before the release of access requests?
There was a problem hiding this comment.
I believe that is to be a fast-follow
| } | ||
| } | ||
|
|
||
| async fetchServers(params: ServerSideParams) { |
There was a problem hiding this comment.
The callsites that call these new methods from clustersService need to wrap the calls to those methods in retryWithRelogin.
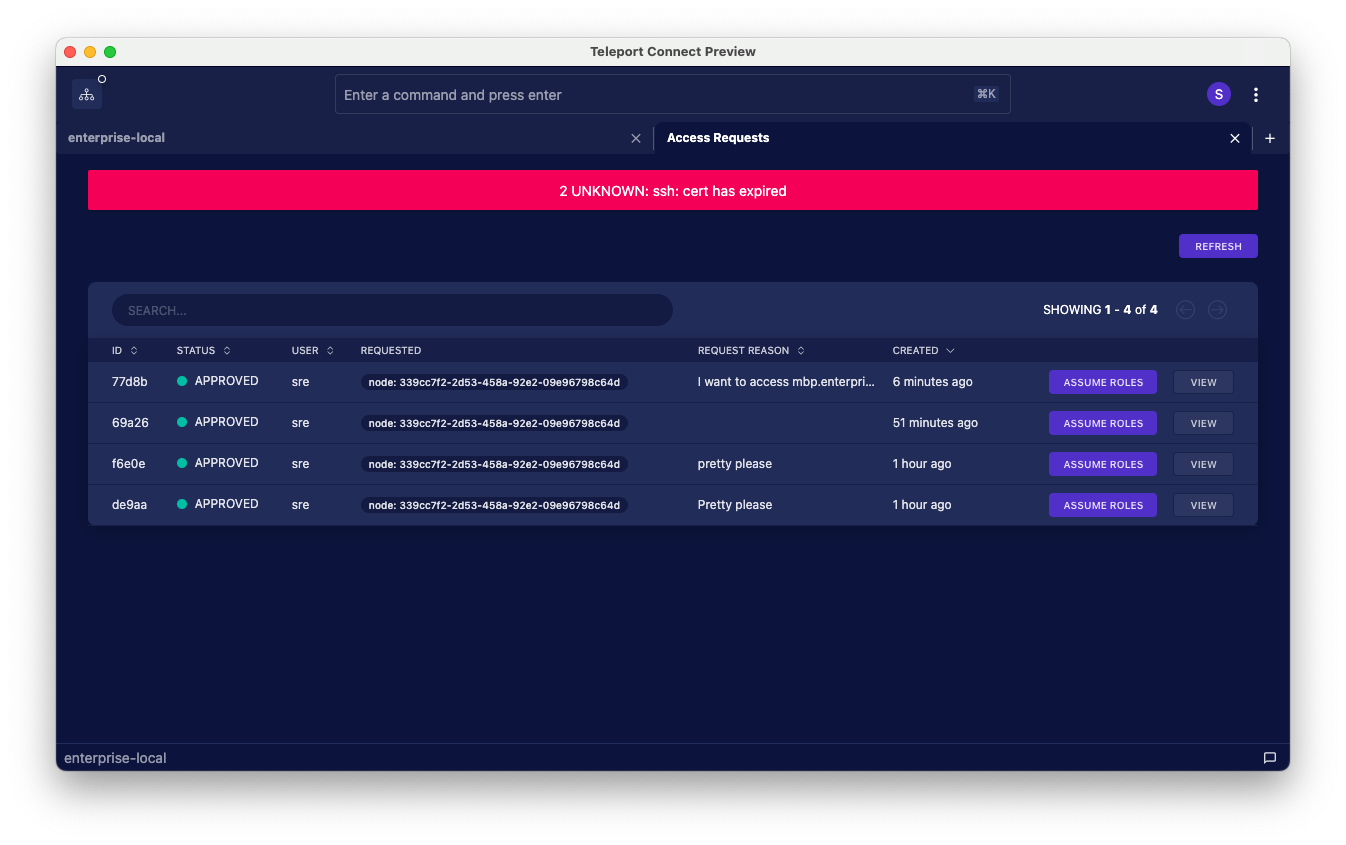
When I came back to the running dev version of Electron, I saw this:
I think this couldn't happen by itself because AFAIK Connect just doesn't decide to make a request by itself, I must've went from the view request "page" to the list of all requests.
In any case, the general rule is that the backend handlers that use RetryWithRelogin need to be wrapped with retryWithRelogin on the frontend for the whole system to take effect.
Look up how other places in the frontend app do this. retryWithRelogin needs to tightly wrap the call to ClustersService.
You might have a problem with passing a meaningful value as the resourceUri argument to retryWithRelogin. In case of, for example, listing all resources, I don't think you'll have a meaningful resource URI to pass there. In that case, that argument is used only to get the root cluster URI, so you can just pass the cluster URI (if it's a leaf cluster URI, retryWithRelogin will extract the root cluster URI from it automatically).
There was a problem hiding this comment.
Ok, i wrapped the requests. Funnily enough, that fetchServers seems to have been vestigial from before the `getAllServers' and 'getServers' distinction as it isn't used anywhere in the codebase atm.
|
I think we are ready to the merge. The only thing that still puzzles me is the state we store on the disk (surprise 🙂). I didn’t realize that
const assumedAccessRequests = (
cluster.loggedInUser.activeRequestsList.length
? await this.client.getAccessRequests(clusterUri)
: []
The only downside of this is that My main motivation is to store as little state as possible in |
* init webapps.e ref * update web.e * added imported components * udpated to correct imported types * webapps.e update * readme update and lint fix * removed extra console logs * sub head fix for webe * reattached webape head * fixed tests * added access request change confirm dialog * null check * webappe * count to accessRequestSerivce, import/export names, small fixes * fixed imports and createrequest params * updated imports from removed containers in teleterm-e * optional params for reuse outside of ClusterLogout * webapps.e ref update * update webapps.e ref * webapps.e ref update * webapps.e ref update and navigation item update * webapps.e update * align sync button center to match access request size * added accessRequestsSerice tests * updating webapps.e * created accessRequests object on workspace type and cleanup * added requestId to documentaccessrequest type and webapps.e update * protobuf updates changing created/expires from string to timestamppb * webappse update and review feedback * updated protos with comments * changing delete/review access request responses to void * updated getaccessrequests to not include ID * protobuf updates * webappse update * update to resource tables styles * update to standard access_request_id field in RPCs * webappse upddate * updated tests and added types * updated webappse * clusterService method for getrequestableroles, retryWithRelogin for fetch, webappse update * webappse update * story fixes * added kubes support to tsh * proto files * update webappse * Provide `WorkspaceContext` for documents in each workspace * updating webappse * webappse update * accessrequestservice fix for resoruces * updated webapps.e after master merge * removed extra data from persisted state for assumed access requests * update webappse * protobuf files * lint fixes * adding getWorkspaces stub to fix tests * webappse update * webappse snapshots update * protobuf updates Co-authored-by: Grzegorz Zdunek <grzegorz.zdunek@goteleport.com>
* [Connect] Add Document Access Requests (#1203) * init webapps.e ref * update web.e * added imported components * udpated to correct imported types * webapps.e update * readme update and lint fix * removed extra console logs * sub head fix for webe * reattached webape head * fixed tests * added access request change confirm dialog * null check * webappe * count to accessRequestSerivce, import/export names, small fixes * fixed imports and createrequest params * updated imports from removed containers in teleterm-e * optional params for reuse outside of ClusterLogout * webapps.e ref update * update webapps.e ref * webapps.e ref update * webapps.e ref update and navigation item update * webapps.e update * align sync button center to match access request size * added accessRequestsSerice tests * updating webapps.e * created accessRequests object on workspace type and cleanup * added requestId to documentaccessrequest type and webapps.e update * protobuf updates changing created/expires from string to timestamppb * webappse update and review feedback * updated protos with comments * changing delete/review access request responses to void * updated getaccessrequests to not include ID * protobuf updates * webappse update * update to resource tables styles * update to standard access_request_id field in RPCs * webappse upddate * updated tests and added types * updated webappse * clusterService method for getrequestableroles, retryWithRelogin for fetch, webappse update * webappse update * story fixes * added kubes support to tsh * proto files * update webappse * Provide `WorkspaceContext` for documents in each workspace * updating webappse * webappse update * accessrequestservice fix for resoruces * updated webapps.e after master merge * removed extra data from persisted state for assumed access requests * update webappse * protobuf files * lint fixes * adding getWorkspaces stub to fix tests * webappse update * webappse snapshots update * protobuf updates Co-authored-by: Grzegorz Zdunek <grzegorz.zdunek@goteleport.com> * webapps.e update Co-authored-by: Grzegorz Zdunek <grzegorz.zdunek@goteleport.com>
This method wasn't used anywhere since #1203 got merged.
This method wasn't used anywhere since #1203 got merged.
* Remove ClustersService methods related to apps I had problems with the new types and apps because I didn't create a separate type for app URI. So I decided to remove it all because it isn't used anyway. * Remove WorkspacesService.getWorkspacesDocumentsServices This method wasn't used anywhere since #1203 got merged.
* Remove ClustersService methods related to apps I had problems with the new types and apps because I didn't create a separate type for app URI. So I decided to remove it all because it isn't used anyway. * Remove WorkspacesService.getWorkspacesDocumentsServices This method wasn't used anywhere since #1203 got merged.
* Remove ClustersService methods related to apps I had problems with the new types and apps because I didn't create a separate type for app URI. So I decided to remove it all because it isn't used anyway. * Remove WorkspacesService.getWorkspacesDocumentsServices This method wasn't used anywhere since #1203 got merged.
teleport PR
Original description can be found here.
This PR has all the proto file changes so the files changed number is a bit bloated but still quite large.
and a neat little video to show off the basic flow/features
Untitled.mov
Fixes gravitational/teleport#15169