Add rate limiting to unauthenticated routes#19593
Conversation
 codingllama
left a comment
codingllama
left a comment
There was a problem hiding this comment.
Add rate limiting to unauthenticated routes and fix a bug in the rate limiter logic.
Sorry, what was the bug?
|
@codingllama The rate limiter was checking the remote IP address AND port. Multiple requests using something like curl would never trigger the rate limiter because each new request would come from a different remote port. |
Well spotted. Thanks for the fix! |
Co-authored-by: Alan Parra <alan.parra@goteleport.com>
2c9125a to
3d60c4d
Compare
|
@sfreiberg See the table below for backport results.
|
|
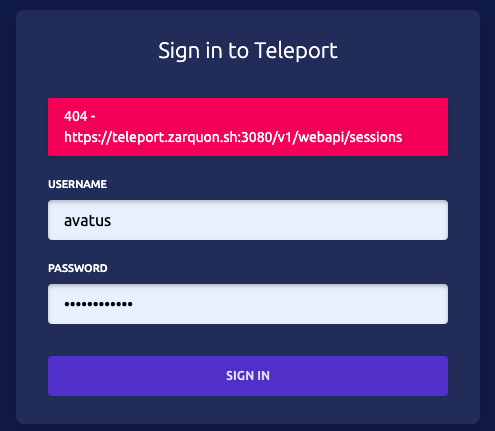
I missed this in the review (was testing not this part I guess?) but this broke logging in via the webapi. results in the web login form giving the error Apparently the old "REMOVE IN 5.1" comment wasn't quite accurate. Adding this line back in fixes the login issue h.POST("/webapi/sessions", httplib.WithCSRFProtection(h.createWebSession))Although I suppose the frontend change to call the new endpoint would probably be a better fix. |
|
I've put up a PR here on the webapps repo for a fix so we can roll with this code and actually deprecate this endpoint. Would love a set of eyes and any historical info around this part of the code base |
|
Yep, cleaning up those "DELETE IN" lines without double-checking can be a risky move. I almost pointed it out, but OTOH we do want people to address them. Thanks for following up on it. |
|
Apologies for this. I remember explicitly testing this locally before I committed but must have forgot to restart the server. In retrospect I should have done this in a separate PR and only on master. Also for these kinds of comments we should open an issue and link to it in the comment so that history is easy for anybody to find. |
|
@sfreiberg Is there a reason why |
|
@Joerger I filled this issue to track the additional rate limit gap you mentioned: https://github.com/gravitational/teleport-private/issues/403 Let me know if I can help with that change as part of #21005 |
Purpose
Add rate limiting to unauthenticated routes and fix a bug in the rate limiter logic.
Implementation