[Security Solution][Endpoint] Reuse disableProtections function for cloud policies#144460
Conversation
|
Pinging @elastic/security-onboarding-and-lifecycle-mgt (Team:Onboarding and Lifecycle Mgt) |
|
Hey @gergoabraham Thank you for adding Regarding the questions:
You're correct about these ones. That shouldn't be a problem. There is no need to disable the blocklist or the popup.
Actually, we ended up disabling everything just for safety. If @kevinlog can confirm that the |
This is correct. The You are both correct that |
|
@kevinlog @opauloh thanks a lot for the thoughts! I've reverted the disabling of the Here is how a cloud policy look like now with the current version: {
"windows": {
"events": {
"dll_and_driver_load": true,
"dns": true,
"file": true,
"network": true,
"process": true,
"registry": true,
"security": true
},
"malware": { "mode": "off", "blocklist": false },
"ransomware": { "mode": "off", "supported": true },
"memory_protection": { "mode": "off", "supported": true },
"behavior_protection": { "mode": "off", "supported": true },
"popup": {
"malware": { "message": "", "enabled": false },
"ransomware": { "message": "", "enabled": false },
"memory_protection": { "message": "", "enabled": false },
"behavior_protection": { "message": "", "enabled": false }
},
"logging": { "file": "info" },
"antivirus_registration": { "enabled": false },
"attack_surface_reduction": { "credential_hardening": { "enabled": false } }
},
"mac": {
"events": { "process": true, "file": true, "network": true },
"malware": { "mode": "off", "blocklist": false },
"behavior_protection": { "mode": "off", "supported": true },
"memory_protection": { "mode": "off", "supported": true },
"popup": {
"malware": { "message": "", "enabled": false },
"behavior_protection": { "message": "", "enabled": false },
"memory_protection": { "message": "", "enabled": false }
},
"logging": { "file": "info" }
},
"linux": {
"events": {
"process": true,
"file": true,
"network": true,
"session_data": true,
"tty_io": false
},
"malware": { "mode": "off", "blocklist": false },
"behavior_protection": { "mode": "off", "supported": true },
"memory_protection": { "mode": "off", "supported": true },
"popup": {
"malware": { "message": "", "enabled": false },
"behavior_protection": { "message": "", "enabled": false },
"memory_protection": { "message": "", "enabled": false }
},
"logging": { "file": "info" }
}
}
Notes:
|
 opauloh
left a comment
opauloh
left a comment
There was a problem hiding this comment.
Looks great, thanks @gergoabraham !!
 ashokaditya
left a comment
ashokaditya
left a comment
There was a problem hiding this comment.
Checked it out. Works as expected. 🚢 it
|
@elasticmachine merge upstream |
💛 Build succeeded, but was flaky
Failed CI StepsTest Failures
Metrics [docs]Unknown metric groupsESLint disabled in files
ESLint disabled line counts
Total ESLint disabled count
History
To update your PR or re-run it, just comment with: |
Summary
We got two implementations for disabling protections, one for Traditional Endpoints environment and one for Cloud Workloads environment. It would be great to use the same implementation for both, this PR wants to check whether
disableProtections()implemented for Traditional Endpoints (added in #144087) can be used for Cloud Workloads, too.Pros:
credential_hardeningprotection on Windows,PolicyConfig, type error will make sure thatdisableProtections()will be updated❓ Questions, issues
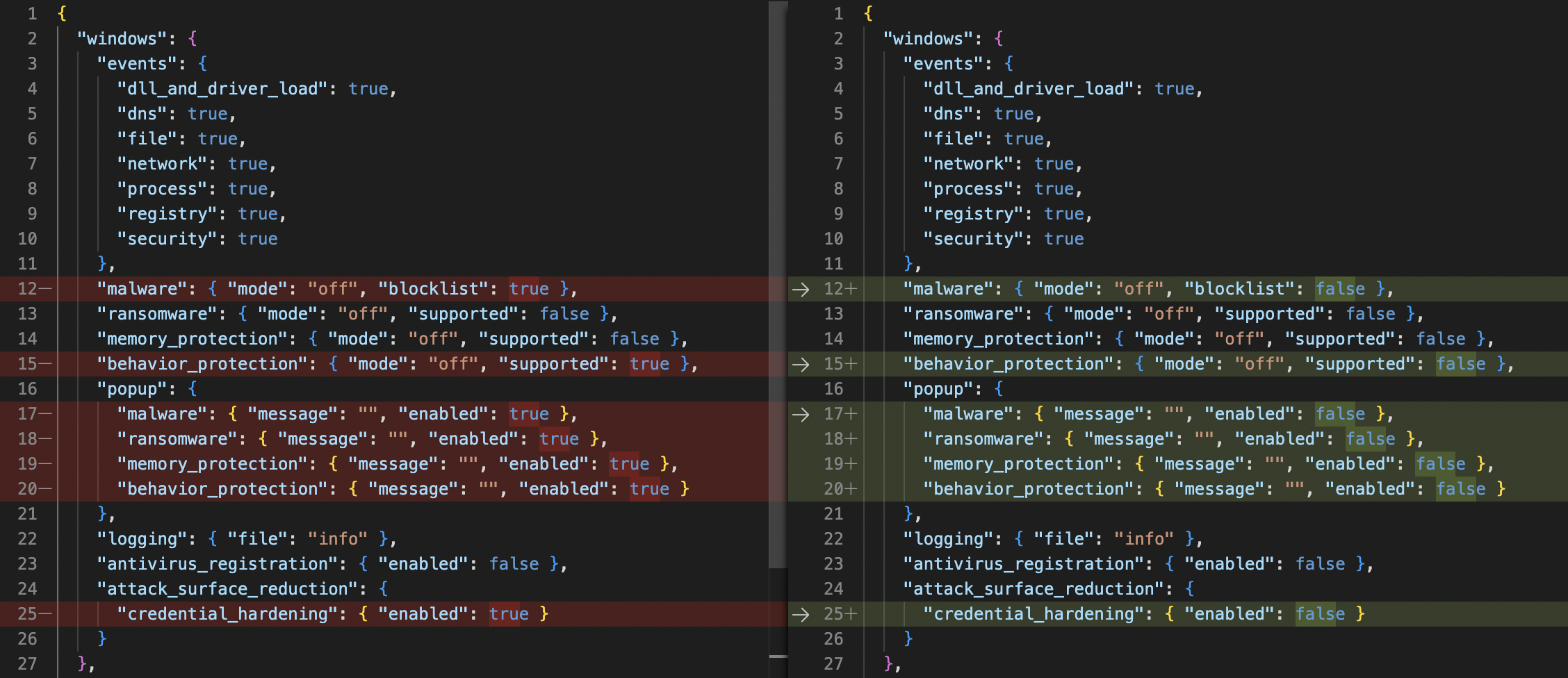
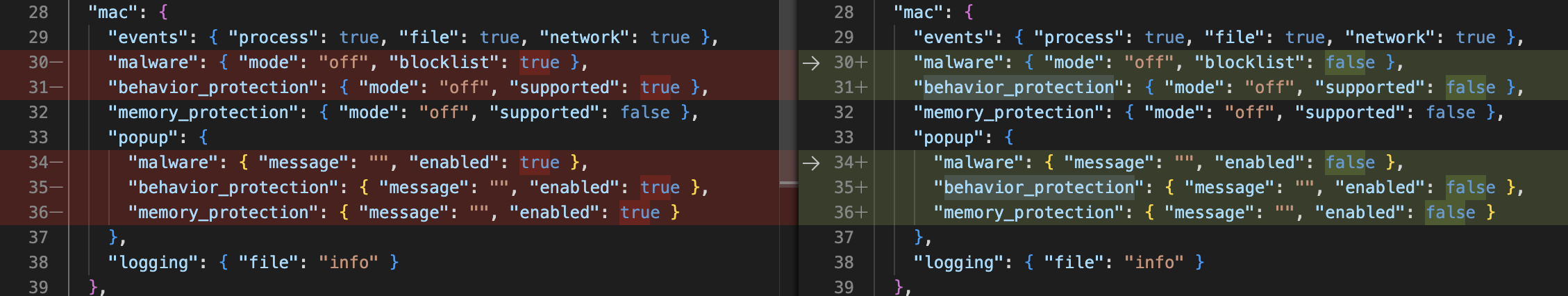
There are some differences between the original cloud policy and the one created by
disableProtections(), and I'd like to understand the differences, and whether it's worth to usedisableProtections()at all, if it needs so many modifications.policy.*.malware.blocklistare set tofalse- as malware itself is disabled, this shouldn't be a problem. Or can it be?policy.*.behavior_protection.supportedare set tofalse- how should thesupportedfields look like? According to @kevinlog, they should describe the support by license, so I assume they should be untouched bydisableProtections(), but in the original cloud policy some are disabled, some are not.policy.*.popup.*.enabledare set tofalse- if protections are disabled, these should not matter. Or do they?@kevinlog, @opauloh could you please help me out with these questions? ☝️
Here is the difference for Windows, the original policy is on the left, the new one is on the right:
Mac and Linux are similar:
Checklist