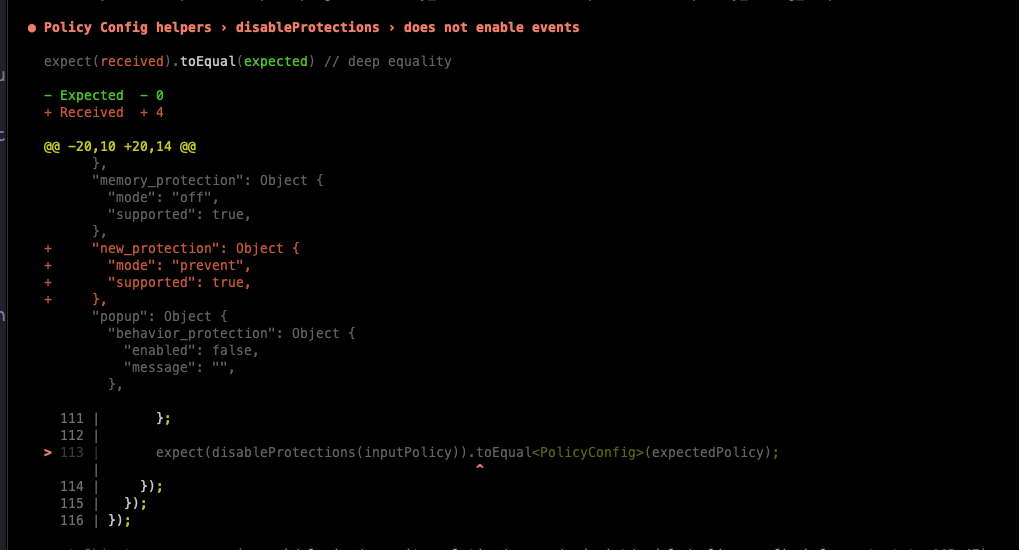
[Security Solution][Endpoint] Guided onboarding configures events only for endpoint policy#144087
Conversation
|
Pinging @elastic/security-onboarding-and-lifecycle-mgt (Team:Onboarding and Lifecycle Mgt) |
| * @param policy | ||
| * @returns | ||
| */ | ||
| export const disableProtections = (policy: PolicyConfig): PolicyConfig => { |
There was a problem hiding this comment.
I was thinking about your comment on slack that getCloudPolicyConfig does not have all protections disabled, and I'm wondering how we can enforce that all protections will be disabled in case more protections are added in the future since protections are not included under a specific object.
So I think, instead of a disabledProtections function, we could create a policyFactoryWithDisabledProtections, then Typescript would ensure every new field added on PolicyConfig is explicitly set on the policy:
For example (in policy_config.ts):
/**
* Return a policyFactory with all protections disabled`
*/
export const policyFactoryWithDisabledProtections = (): ReturnType<typeof policyFactory> => {
const policy = policyFactory();
return {
windows: {
events: {
...policy.windows.events
},
malware: {
mode: ProtectionModes.off,
blocklist: true,
},
ransomware: {
mode: ProtectionModes.off,
supported: false,
},
memory_protection: {
mode: ProtectionModes.off,
supported: false,
},
behavior_protection: {
mode: ProtectionModes.off,
supported: false,
},
popup: {
malware: {
message: '',
enabled: false,
},
ransomware: {
message: '',
enabled: false,
},
memory_protection: {
message: '',
enabled: false,
},
behavior_protection: {
message: '',
enabled: false,
},
},
logging: {
...policy.windows.logging
},
antivirus_registration: {
enabled: false,
},
attack_surface_reduction: {
credential_hardening: {
enabled: false,
},
},
},
mac: {
events: {
...policy.mac.events
},
malware: {
mode: ProtectionModes.off,
blocklist: true,
},
behavior_protection: {
mode: ProtectionModes.off,
supported: true,
},
memory_protection: {
mode: ProtectionModes.off,
supported: true,
},
popup: {
malware: {
message: '',
enabled: false,
},
behavior_protection: {
message: '',
enabled: false,
},
memory_protection: {
message: '',
enabled: false,
},
},
logging: {
...policy.mac.logging
},
},
linux: {
events: {
...policy.linux.events
},
malware: {
mode: ProtectionModes.off,
blocklist: false,
},
behavior_protection: {
mode: ProtectionModes.off,
supported: false,
},
memory_protection: {
mode: ProtectionModes.off,
supported: false,
},
popup: {
malware: {
message: '',
enabled: false,
},
behavior_protection: {
message: '',
enabled: false,
},
memory_protection: {
message: '',
enabled: false,
},
},
logging: {
...policy.linux.logging
},
},
};
};This way, we would still spread over specific fields, but new fields on the root would need to be manually added, and that would enforce the addition of new protection fields to the policy into this function.
Also, this way, the getCloudPolicyConfig() function would be able to reuse the policy.
There was a problem hiding this comment.
That was my biggest question, too: how to ensure that we won't forget to add new protections to disableProtections?
Actually, it is enforced: I added a PolicyConfig constant to the tests that will throw a type error if PolicyConfig is ever modified. See it here.
Why did I add it to the test? Mostly because I didn't want to interfere with the current logic. Now there is only one default config (all ON). And there are 3 modifiers: one for stripping of paid features, one for enabling the support for paid features, and the new one for disabling protections.
I think we can go with either having a constant config for every scenario, or having these modifiers that can be applied after each other. As subsets of the config are independent from each other (like events from protections), I think using modifiers is a better choice.
This means, that getCloudPolicyConfig() can reuse disableProtections() right now, because it only disables protections and does not touch anything else.
What do you think? Would you like me to add disableProtections() to getCloudPolicyConfig()?
There was a problem hiding this comment.
Hey, @gergoabraham just tested adding new protection and the test works great, nicely done! 🙌
There was a problem hiding this comment.
What do you think? Would you like me to add
disableProtections()togetCloudPolicyConfig()?
That makes sense to me, getCloudPolicyConfig inherits all policy defaults, then needs all protections off, and has policy.linux.events.session_data as true. If you can make that change that would be awesome!
 opauloh
left a comment
opauloh
left a comment
There was a problem hiding this comment.
Left a couple of suggestions, let me know what do you think
| malware: { | ||
| message: '', | ||
| enabled: true, | ||
| enabled: policy.mac.popup.malware.enabled, |
There was a problem hiding this comment.
@gergoabraham we should still not change this when we are looking at an unpaid license because part of the advantage of the license is that users can customize the message and toggle it on/off.
There was a problem hiding this comment.
@kevinlog thanks for the explanation, it makes sense now!
I've reverted the modification with an explanatory comment: 5b30c69
And switched the order of the logic, so license limitations are applied in the final step, so disableProtections won't override and disable malware popup: 570c16d
(Disabling malware popup when disabling protections shouldn't be a problem in practice though, I think, because after enabling the malware protection, the popup will be automatically enabled, but still, I think it is clearer to apply the limitations at the end.)
There was a problem hiding this comment.
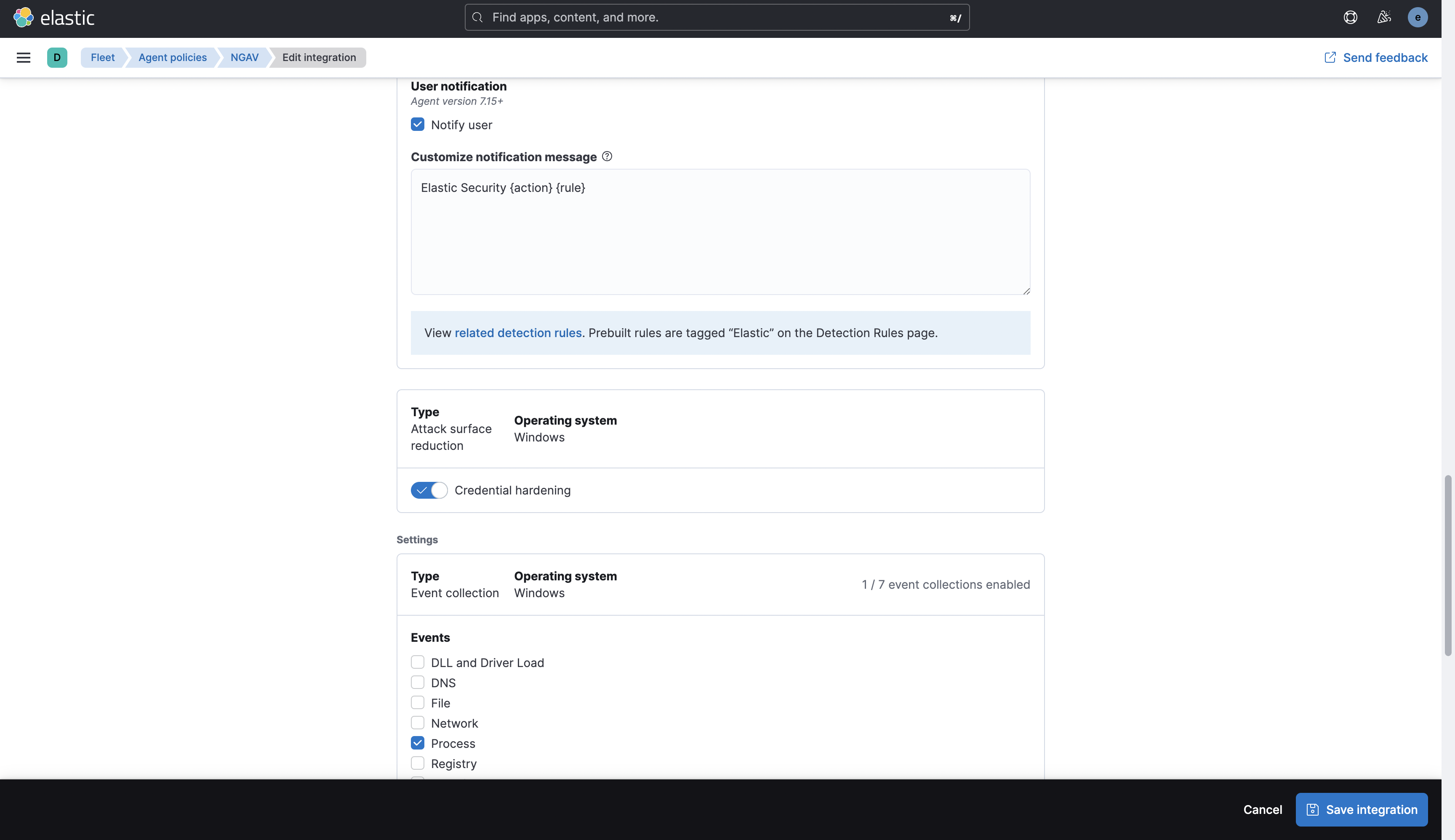
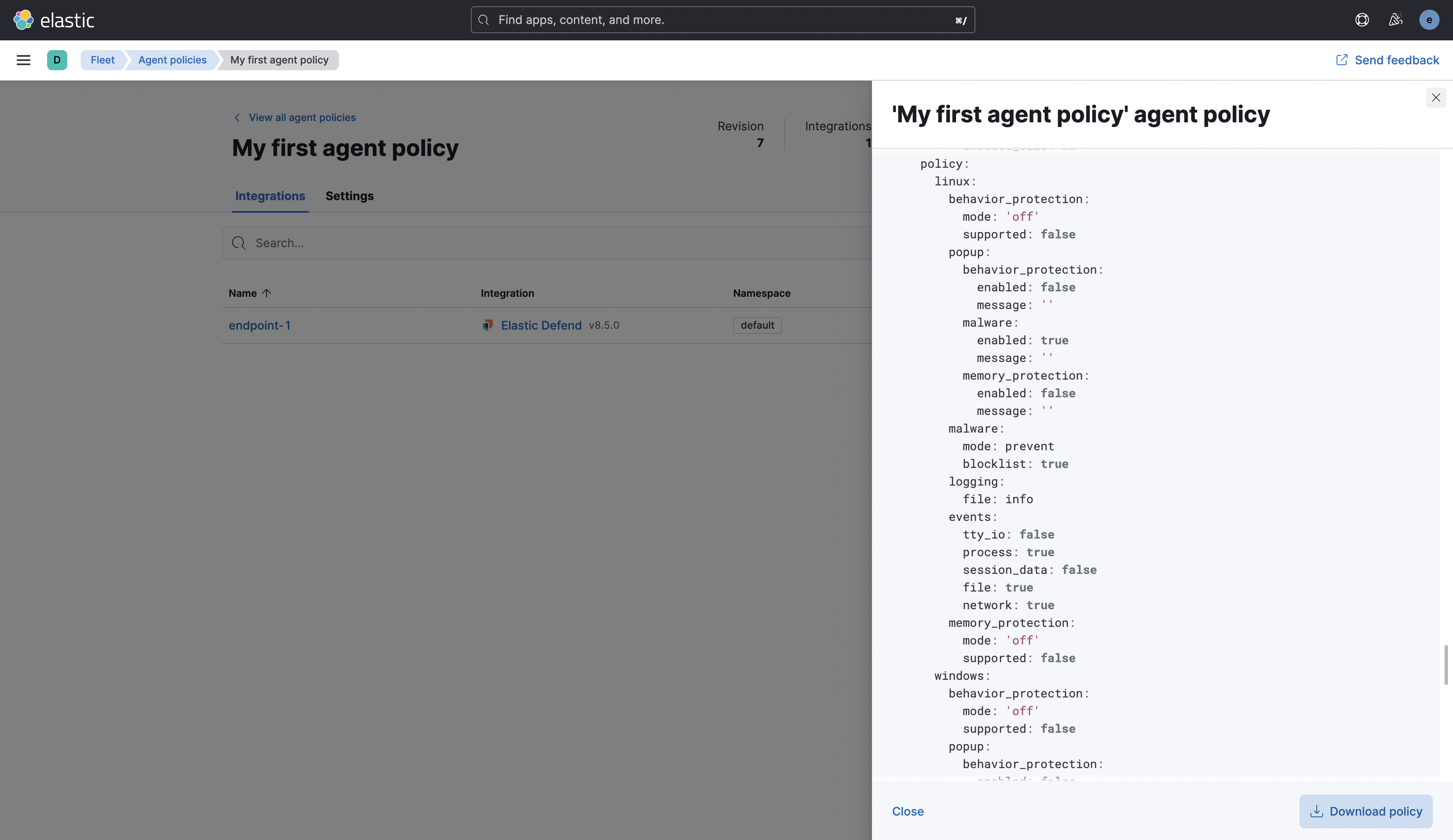
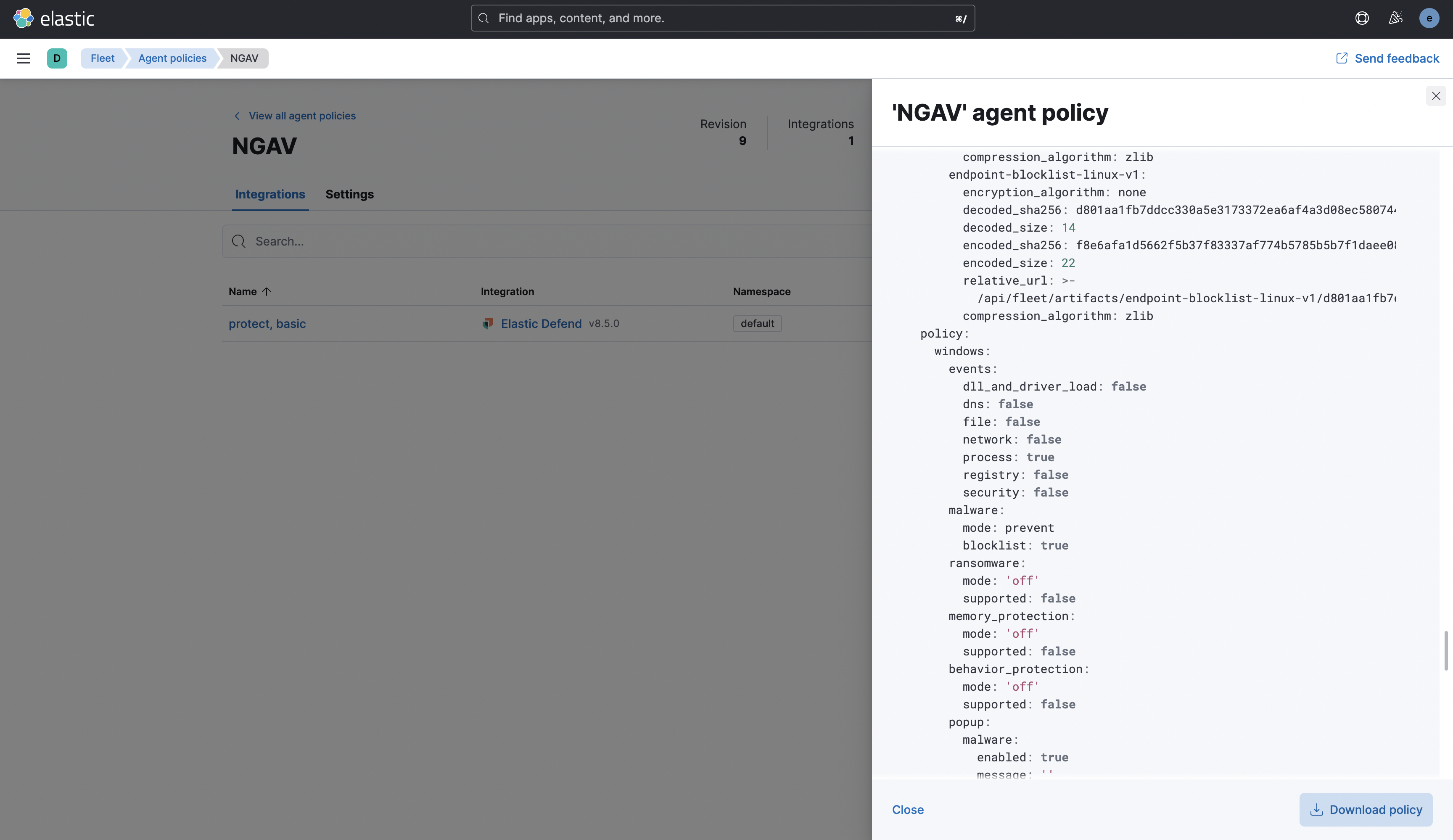
Thanks @gergoabraham ! The logic makes sense to me, we should just be sure to test the cases using the existing NGAV, EDR Essential, and EDR Complete with a basic license and ensure that everything is still working.
|
@elasticmachine merge upstream |
…s-events-only-for-endpoint-policy
💚 Build Succeeded
Metrics [docs]Unknown metric groupsESLint disabled in files
ESLint disabled line counts
Total ESLint disabled count
History
To update your PR or re-run it, just comment with: |
|
Thanks for this comprehensive test @kevinlog - I also tested how it handles when new protections are added and everything LGTM |
 opauloh
left a comment
opauloh
left a comment
There was a problem hiding this comment.
everything LGTM!
If you can make getCloudPolicyConfig use the disableProtections that would be great, feel free to add in a subsequent PR if you want.
@opauloh thanks for the review! I'll open a new PR for this ☝️ |
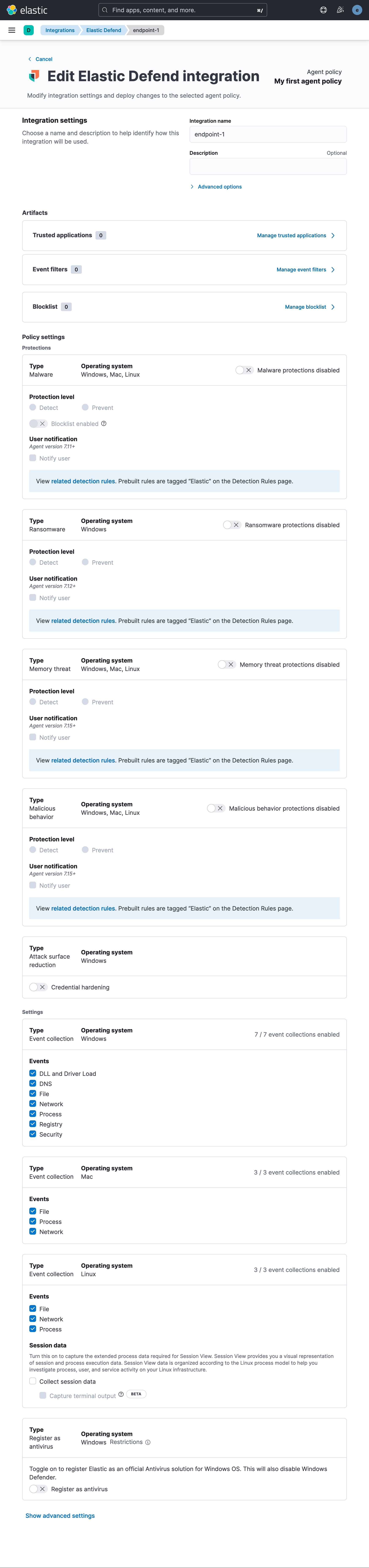
…int onboarding (#149588) ## Summary Added new configuration option for Elastic Defend integration's Traditional Endpoint environment: - Data Collection only configuration option - uses the already available config policy (added here #144087) - the default option is NGAV (as before) Test: - go to Management / Integrations - select Elastic Defend - press the 'Add Elastic Defend' button <img width="1321" alt="image" src="https://user-images.githubusercontent.com/39014407/214846703-9632f6e7-18a8-4312-a61d-8ee9255833e0.png"> ### Checklist - [x] [Unit or functional tests](https://www.elastic.co/guide/en/kibana/master/development-tests.html) were updated or added to match the most common scenarios --------- Co-authored-by: Kibana Machine <42973632+kibanamachine@users.noreply.github.com>
…int onboarding (elastic#149588) ## Summary Added new configuration option for Elastic Defend integration's Traditional Endpoint environment: - Data Collection only configuration option - uses the already available config policy (added here elastic#144087) - the default option is NGAV (as before) Test: - go to Management / Integrations - select Elastic Defend - press the 'Add Elastic Defend' button <img width="1321" alt="image" src="https://user-images.githubusercontent.com/39014407/214846703-9632f6e7-18a8-4312-a61d-8ee9255833e0.png"> ### Checklist - [x] [Unit or functional tests](https://www.elastic.co/guide/en/kibana/master/development-tests.html) were updated or added to match the most common scenarios --------- Co-authored-by: Kibana Machine <42973632+kibanamachine@users.noreply.github.com>
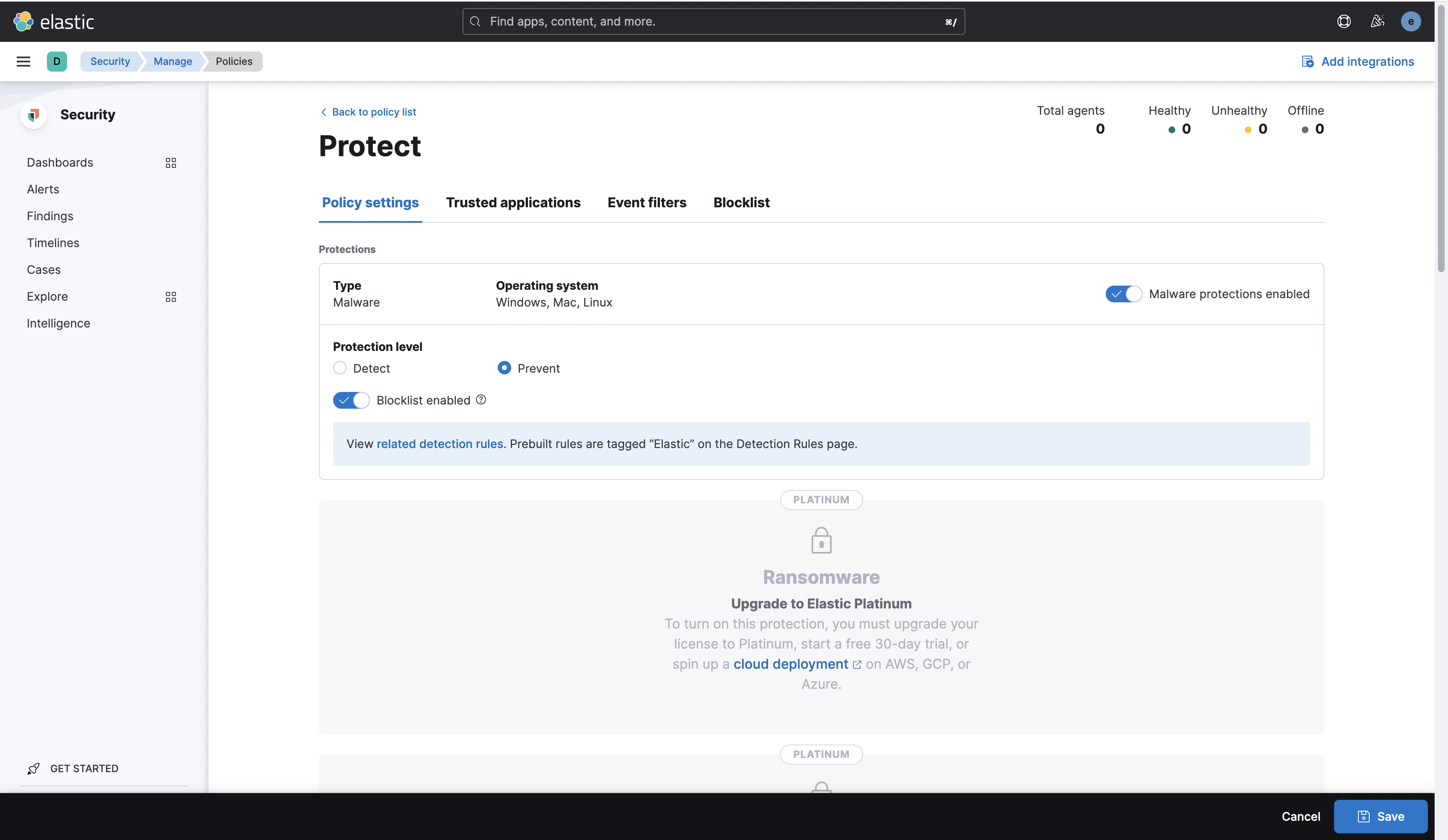
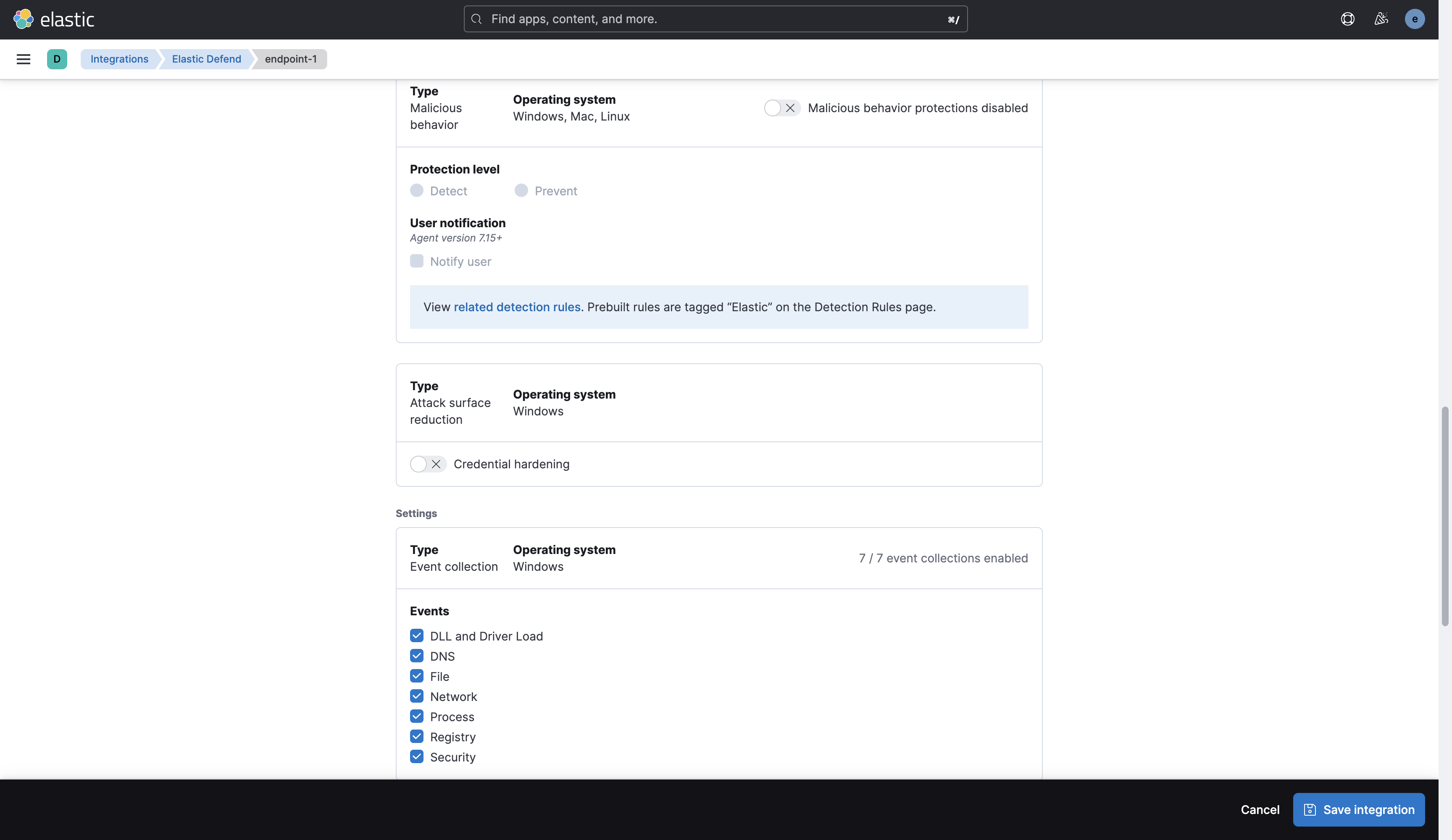
Summary
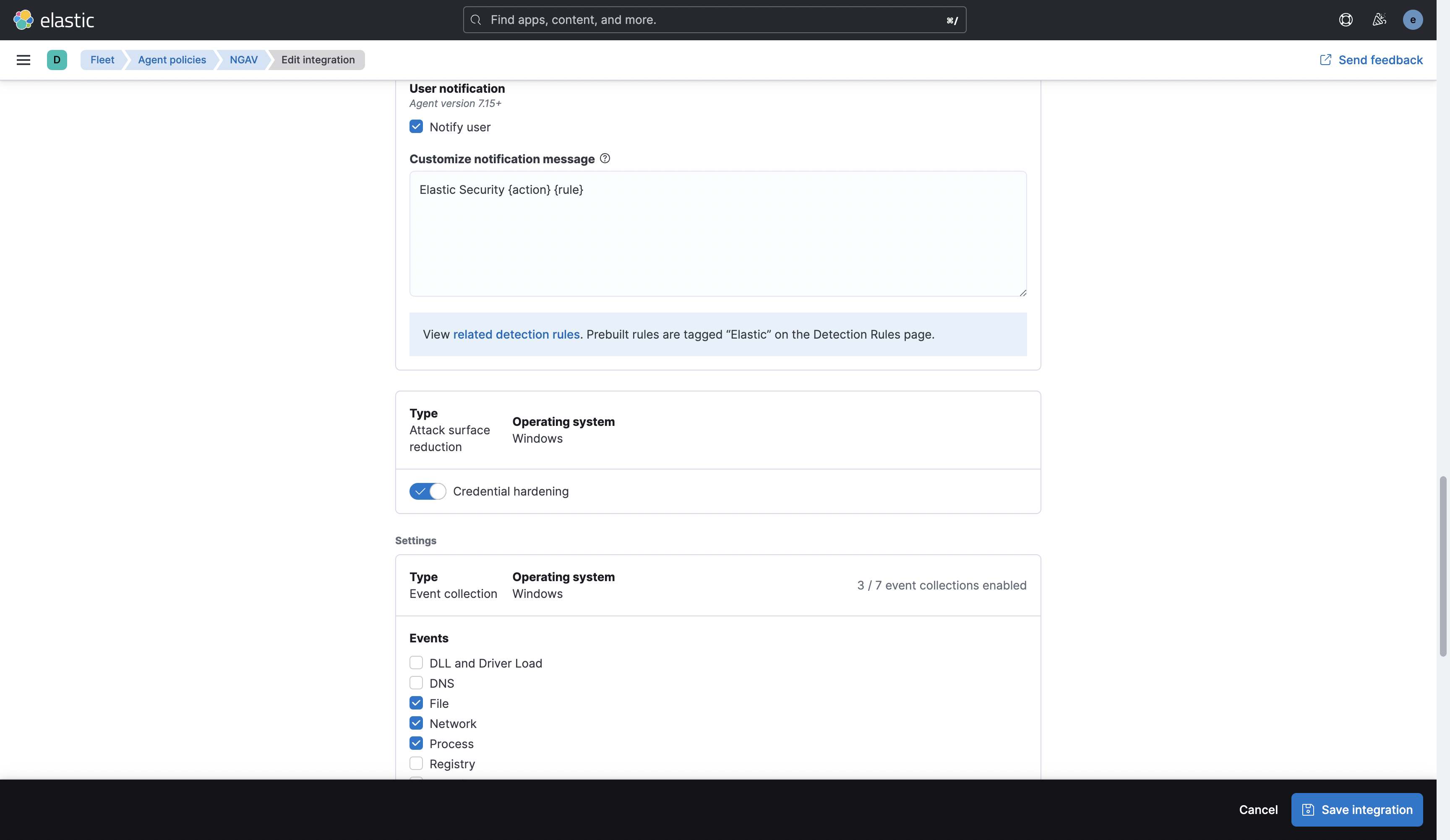
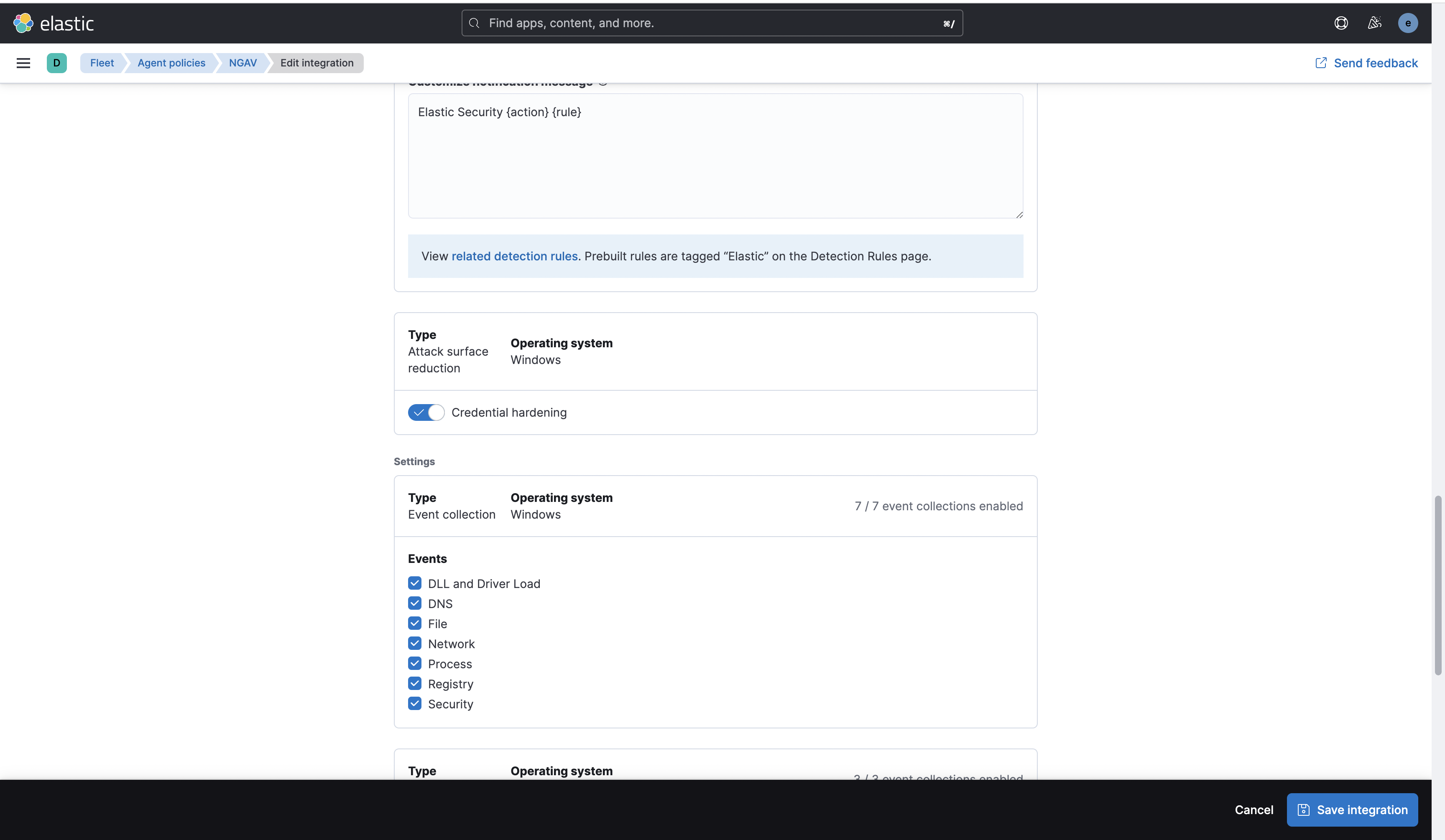
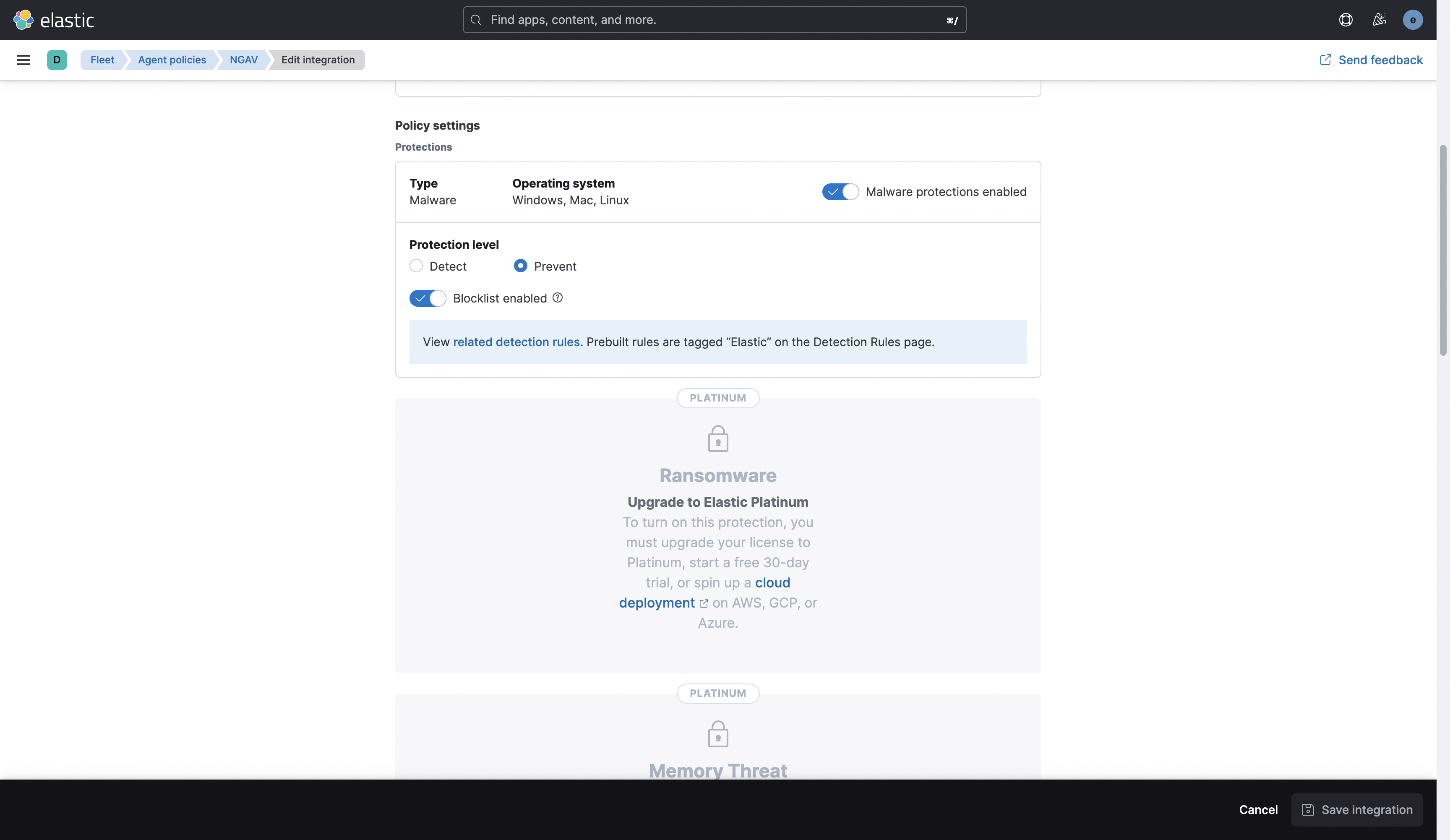
When Endpoint integration is added via the new guided onboarding, every protection is disabled in the endpoint policy. This does not have an effect on the
[ NGAV, EDRComplete, EDREssential]configs.To try out, add
useMultiPageLayoutquery param to the URL when adding Endpoint integration:localhost:5601/app/fleet/integrations/endpoint/add-integration?useMultiPageLayoutSee config result:
Checklist
Delete any items that are not applicable to this PR.