Conversation
| module DocumentCaptureConcern | ||
| def override_document_capture_step_csp | ||
| return if params[:step] != 'document_capture' | ||
| return if IdentityConfig.store.suppress_content_security_policy |
There was a problem hiding this comment.
From @zachmargolis: this methods opens up the policy, does it still cause problems for the accessibiltiy tool on this step if we leave it in?
There was a problem hiding this comment.
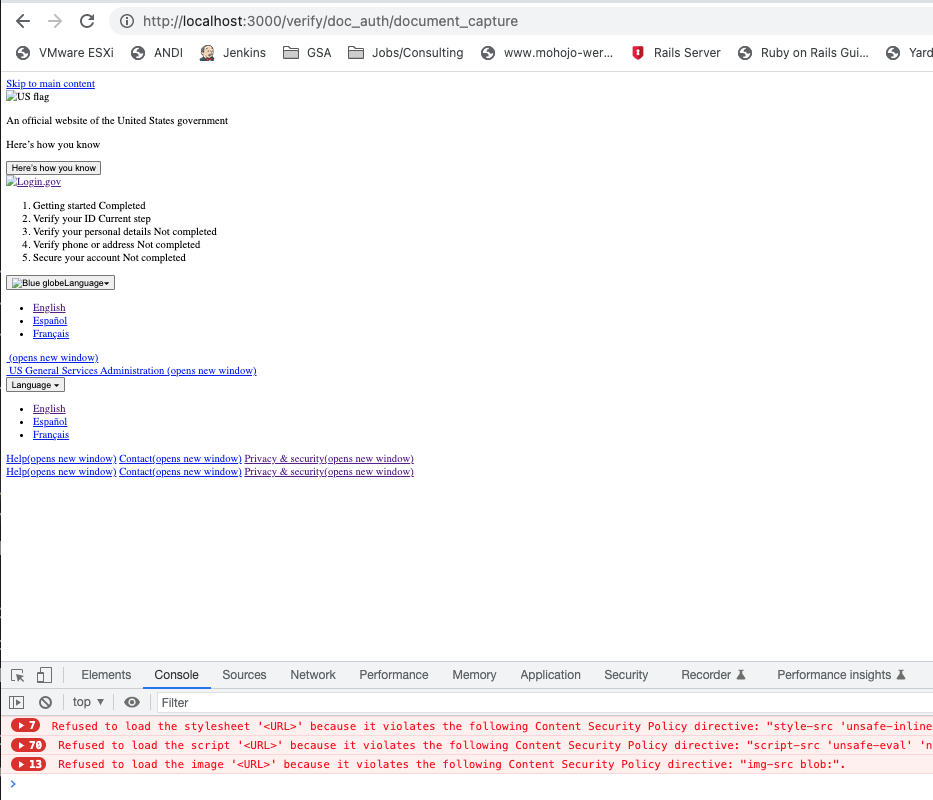
ANDI (anyhow) cannot be loaded/used without line 5, despite the open policy. The reason the opening up the policy here doesn't work, is because of lines 8-10 where policy.xxx_src == :self. policy.xxx_src would need to allow all domains (i.e. policy.xxx_src == '*'). ANDI (for example) executes the following:
javascript:void((function(){andiScript=document.createElement('script');
andiScript.setAttribute('src','https://www.ssa.gov/accessibility/andi/andi.js');
document.body.appendChild(andiScript)})());
|
Copying from #6705 (comment)
|
Apologies for not addressing this, but unfortunately,
The idea is to use it with an AWS sandbox that everyone can use and share; although, we could also use it locally of course. |
|
I put a lot of value in the CSP, so I'd rather see it enforced in more places than in fewer (e.g. local development). One reason is that local development can currently give a false sense of confidence that a feature relying on a CSP bypass will work, only for it to break once it reaches a deployed environment (previously #5852, #4813, #4429, and likely soon again in #6694). As proposed, a fear I'd have is that we'd not know of these issues 'til they start affecting real users in production. Personally, I'd rather see one of:
|
The very idea behind this flipper is to explicitly turn CSP off to open up the possibility to use tools that are helpful, yet otherwise would be unavailable for use; tools that have nothing to do with CSP. 508 tools for example. No one should have any sense of security, false or otherwise, when utilizing this flipper. No one should be using a specific sandbox, unless they know what the sandbox is used for and anyone who would want to test anything to do with CSP on a box that has CSP turned off, probably shouldn't be there to begin with :). The other tools you listed, are (from what I saw) mostly automated tools that require a lot of set up, and much more than a developer may need, as it is in our situation. I'm okay with option 2 (Or, limit its usage to personal sandbox environments, not common ones like dev or int); however, it was Zach's suggestion to place this on a sandbox, and I think it's a good one. If we have to limit this to option 2, I'm okay with that. |
I dug in a bit, and I think the approach is a bit riskier than is necessary. The ANDI bookmarklet in question only tries to inject the WAVE, Accessibility Insights, or Deque offer alternatives that should only take a few clicks to install and inspect elements or potential accessibility issues. With the complexity/risk present here, I think one of the aforementioned alternatives should be pursued. |
If IdentityConfig.store.suppress_content_security_policy is true. changelog: Accessibility, Internal, Add config to suppress content security policy in AWS sandbox (LG-7191)
Inside blocks/procs; use next instead.
8deccd4 to
7de9824
Compare
|
It looks like the ticket for this got cancelled? Is this PR still open for review? |
|
i agree there are times when i need it locally and do something similar in the code. |
|
Looks like this PR hasn't been updated in a bit, I'm going to close it out to keep the list of open PRs small |
It was closed due to the aforementioned concerns. I personally didn't share the same concerns as this would be sandboxed, either locally or on a literal AWS sandbox. While this flipper was not meant to be tool-specific, other tools were offered in lieu of ANDI (which was what prompted this PR). A cursory of the tools offered weren't as intuitive or user-friendly IMHO; but, in all fairness, I didn't have time to dig too deeply into them, which may speak to the intuitiveness/user-friendliness of the tools offered, but like I mentioned, this may be an unfair assessment on my part. |
I see no problem with having that flipper available, even if (albeit) simply for local dev use. We'll probably resort to passing a patch around since some members on our team are familiar with and like the ANDI 508 tool :( |
https://cm-jira.usa.gov/browse/LG-7191
Suppress content security policy (CSP) if IdentityConfig.store.suppress_content_security_policy is true.
ONLY to be set to true on an AWS sandbox or during local development!
508 tools that rely on javascript execution (ANDI for example) are unable to execute in the development environment due to Content Security Policy (CSP) policies.
Creating/setting IdentityConfig.store.suppress_content_security_policy in an AWS sandbox will allow developers to turn CSP off, allowing these valuable tools to run.