LG-6204/LG-6220: capture user pii in a signed JWT and pass to frontend#6282
Merged
LG-6204/LG-6220: capture user pii in a signed JWT and pass to frontend#6282
Conversation
b8e353a to
f60f3d0
Compare
zachmargolis
reviewed
May 2, 2022
f60f3d0 to
96d37d9
Compare
c47f69e to
31c1a35
Compare
aduth
reviewed
May 5, 2022
Comment on lines
37
to
38
Contributor
There was a problem hiding this comment.
I seem to recall you mentioning we might not need this?
Suggested change
| data[:issuer] = service_provider.issuer if service_provider |
Contributor
Author
There was a problem hiding this comment.
Yup - I completely removed the SP from the tokenizer in 8a4cac1cb ee036db05 b3501a7f9
app/controllers/verify_controller.rb
Outdated
Contributor
There was a problem hiding this comment.
Separately, we should start thinking about how to only include the user bundle and remove personalKey. That being said, we'll probably still need it as long as personal key is the only enabled step, if we ship it before others.
Contributor
Author
There was a problem hiding this comment.
Yup, eventually we won't even need the bundle - this is all temporary.
8a4cac1 to
ee036db
Compare
aduth
reviewed
May 5, 2022
app/javascript/packs/verify-flow.tsx
Outdated
Comment on lines
52
to
65
Contributor
There was a problem hiding this comment.
As discussed in our working session, really tempting to pull in Lodash here:
Suggested change
| const camelCase = (string: string) => | |
| string.replace(/[^a-z]([a-z])/gi, (_match, nextLetter) => nextLetter.toUpperCase()); | |
| const jwtData = JSON.parse(atob(initialValues.userBundleToken.split('.')[1])); | |
| const pii = Object.fromEntries( | |
| Object.entries(jwtData.pii).map(([key, value]) => [camelCase(key), value]), | |
| ); | |
| import { mapKeys, camelCase } from 'lodash-es'; | |
| const jwtData = JSON.parse(atob(initialValues.userBundleToken.split('.')[1])); | |
| const pii = mapKeys(jwtData.pii, camelCase); |
ee036db to
b3501a7
Compare
Co-authored-by: Andrew Duthie <andrew.duthie@gsa.gov>
b3501a7 to
32854ae
Compare
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
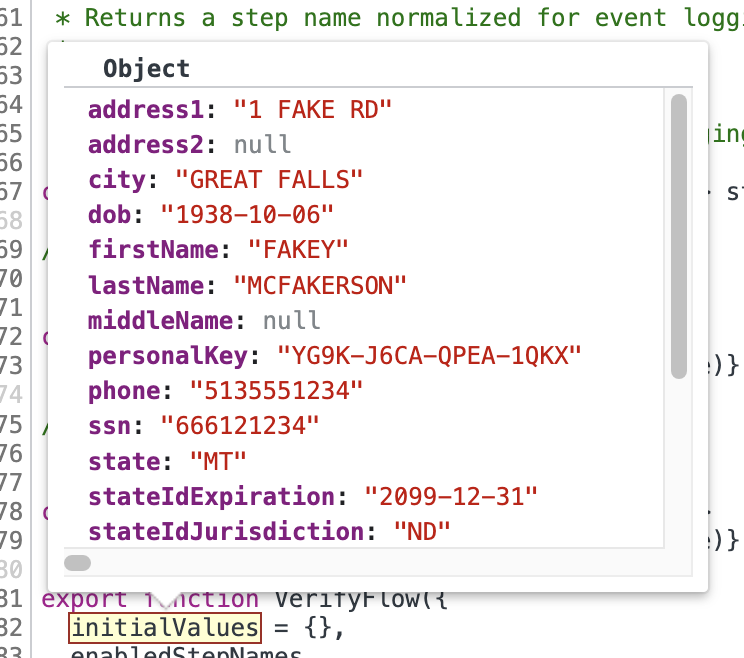
Captures the current state of the user's pii (and a few other session state variables) and packs them in a JWT that is used to initialize the React app for the new IdV flow.
As we work our way back in the flow from the end, we will eventually be managing the user PII in the client, though we will be passing the JWT back and forth since it will contain the verified data and will be signed by the server.
The pii in the JWT is added to the initial values that are given to the React app.