-
-
Notifications
You must be signed in to change notification settings - Fork 37.2k
Replace pbkdf2 with bcrypt #16071
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Replace pbkdf2 with bcrypt #16071
Changes from all commits
2536c58
4148124
492efca
99f8035
5726600
e160a79
560b829
21895ff
542788f
File filter
Filter by extension
Conversations
Jump to
Diff view
Diff view
There are no files selected for viewing
| Original file line number | Diff line number | Diff line change |
|---|---|---|
|
|
@@ -2,6 +2,7 @@ aiohttp==3.4.0 | |
| astral==1.6.1 | ||
| async_timeout==3.0.0 | ||
| attrs==18.1.0 | ||
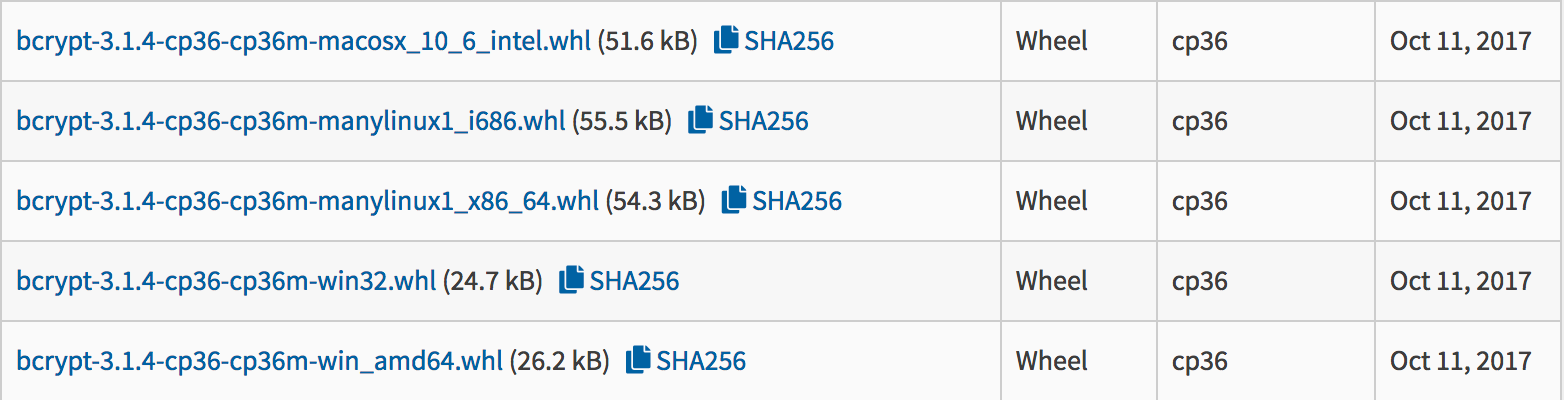
| bcrypt==3.1.4 | ||
|
||
| certifi>=2018.04.16 | ||
| jinja2>=2.10 | ||
| PyJWT==1.6.4 | ||
|
|
||
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
We'll need a migration path. We can only do the migration while a user is logging in. Verify with old pattern -> if ok, migrate to new salt.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
added