Boost CLI onLogin pref by proxyClient injection#25137
Boost CLI onLogin pref by proxyClient injection#25137smallinsky wants to merge 2 commits intomasterfrom
Conversation
d8bfabf to
c8ac84d
Compare
c8ac84d to
1799ef9
Compare
|
@rosstimothy Let me know what do you think about this solution where a proxyClient is initialised in top flow and then propagated by WithProxyClient func so we can fully levrage the proxy.CurrentCluster() caching. |
Nice! What do you think about making the clients explicit arguments in functions that require connections to a cluster instead of using functional options? Processing the options is a bit verbose, although I suppose a helper method to get the client from the options might eliminate that. |
72aa3d6 to
d3c0f69
Compare
I'm not big fan of this approach without doing complete alignment because we will create a lot of vague functions with nil parameter like
yea, I have updated the code applying this approach in: d3c0f69 |
Yeah I think this only makes sense if we convert all usages so that passing in |
|
@smallinsky I took the alternate approach of explicitly requiring an |
@rosstimothy |
Experimental
What
Make the tsh login function more robust by forwarding proxyClient and leveraging the proxyClient cache. .
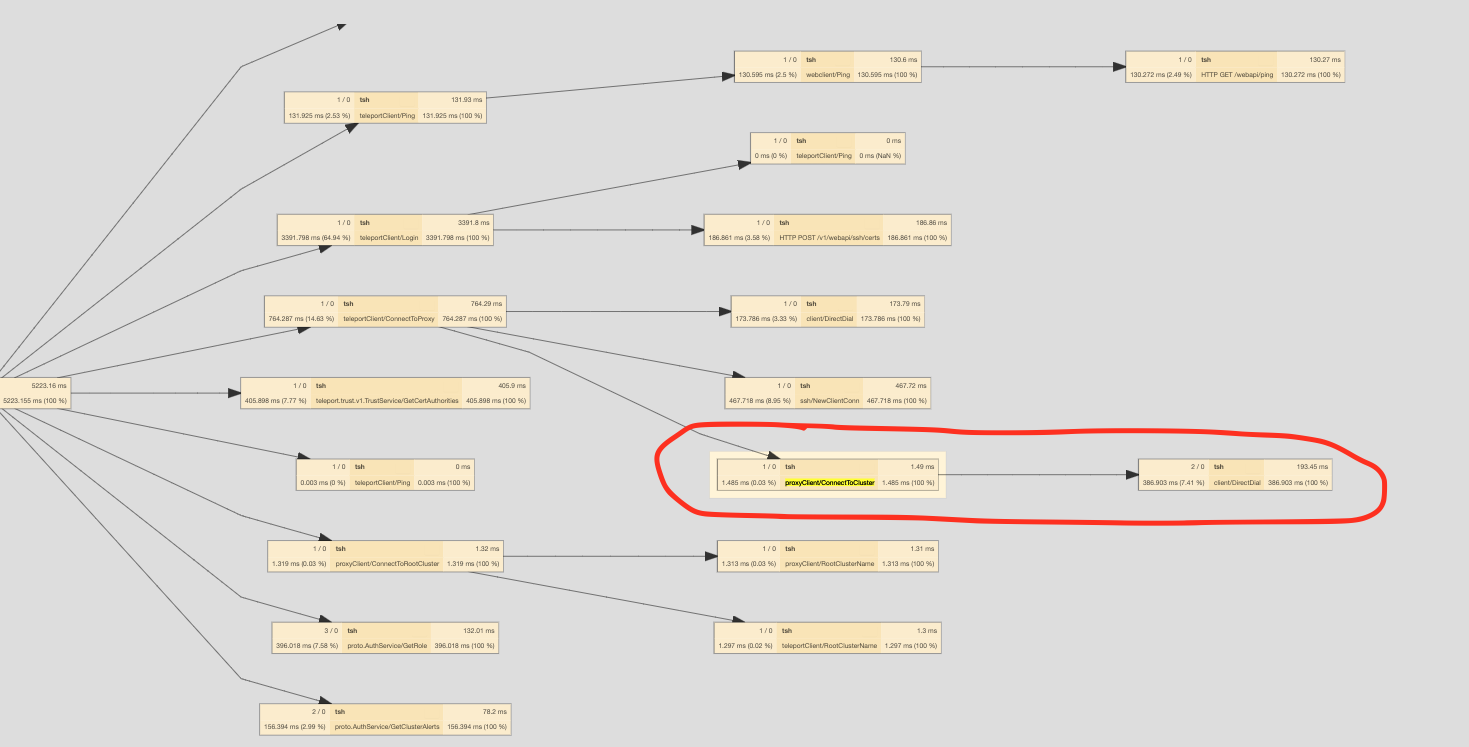
before 4.348 s ± 0.151 s :
3x Remote Connect To Cluster Calls:
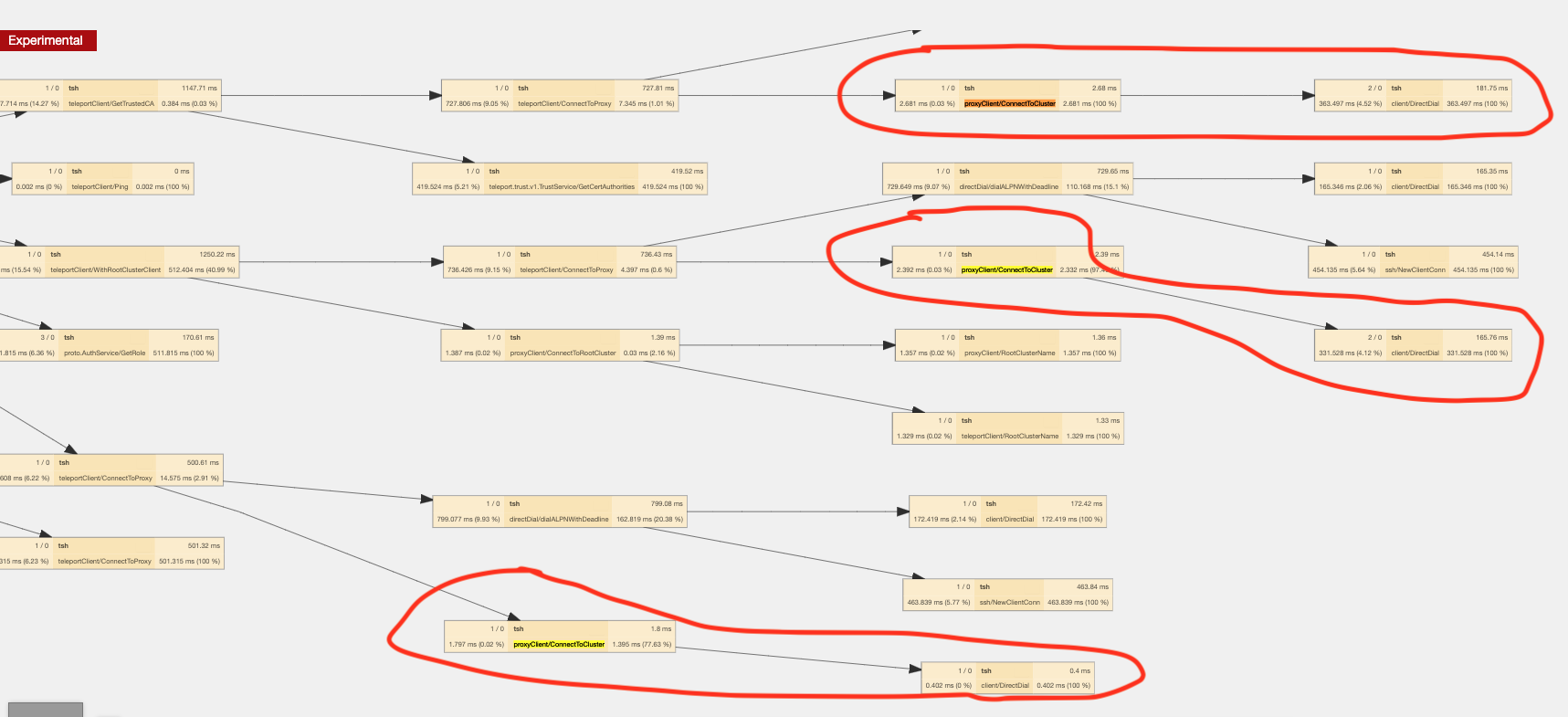
after 2.303 s ± 0.073 s:
1x Remote Connect To Cluster Call: