aws auth use default creds when none are supplied#17932
aws auth use default creds when none are supplied#17932Vad1mo merged 2 commits intogoharbor:mainfrom caleblloyd:aws-auth-use-creds-default
Conversation
 Vad1mo
left a comment
Vad1mo
left a comment
There was a problem hiding this comment.
This looks good to me, any idea or guide how to easily test this on AWS?
|
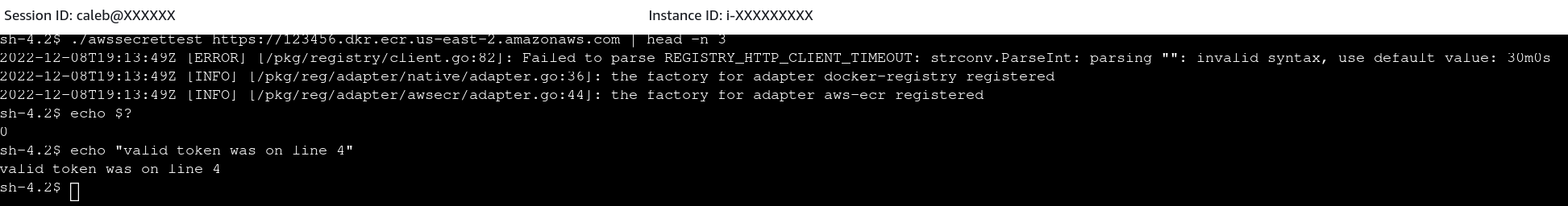
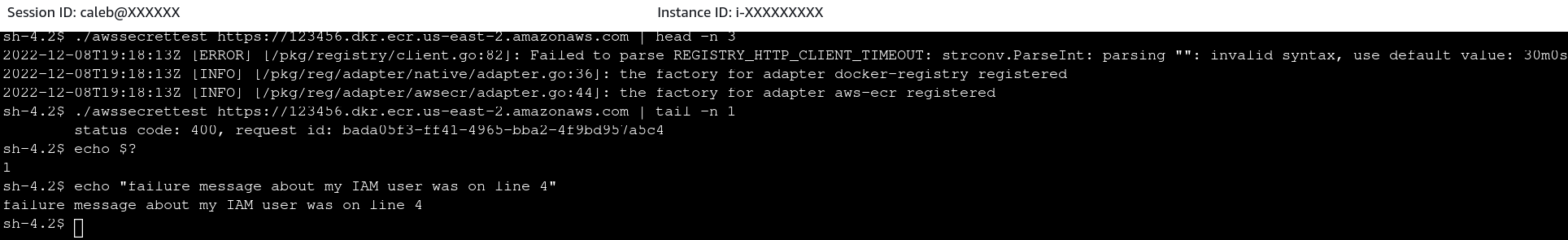
A little tough to unit test because you need actual creds to run through the SDK. But I purpose-built a couple test binaries in branches on my fork. This run demonstrates that Before, the I also tested Good/Bad static creds after the change and there are no regressions there. Before Change:Test source: https://github.com/caleblloyd/harbor/tree/aws-test-before-change/src/awssecrettest Auto DetectAfter Change:Test source: https://github.com/caleblloyd/harbor/tree/aws-test-after-change/src/awssecrettest Auto DetectWith Bad Static Token:With Good Static Token: |
|
Hey @Vad1mo, are you the other reviewer on this PR? We're really excited to get this released |
|
Hi @caleblloyd @Vad1mo, what is the status on this PR? |
|
Will close and re-open the PR so we can try to unblock GH actions! |
Codecov Report
@@ Coverage Diff @@
## main #17932 +/- ##
==========================================
- Coverage 66.41% 66.41% -0.01%
==========================================
Files 1012 1012
Lines 108684 108682 -2
Branches 2676 2676
==========================================
- Hits 72186 72184 -2
+ Misses 32534 32531 -3
- Partials 3964 3967 +3
Flags with carried forward coverage won't be shown. Click here to find out more.
|
|
@caleblloyd, seems the test fail, can you rebase and we try again. We merge if it becomes green. |
|
Yes I will rebase, I also had a change in here to upgrade
So I will remove the |
|
Opened #18134 requesting the dependency update |
|
@caleblloyd looks like test coverage decreased by 0.01% and failed the checks. Can we do anything about it? |
Signed-off-by: Caleb Lloyd <caleblloyd@gmail.com>
|
All the checks were green, but it was complaining that the commit was not signed, so I have re-pushed the same code except with a signed commit now. I think the workflows may need to be manually approved again because I am a first-time contributor? |
Signed-off-by: Caleb Lloyd <caleblloyd@gmail.com> Co-authored-by: Vadim Bauer <vb@container-registry.com> Signed-off-by: Maksym <maksym@container-registry.com>
Signed-off-by: Caleb Lloyd <caleblloyd@gmail.com> Co-authored-by: Vadim Bauer <vb@container-registry.com> Signed-off-by: Stephan Hohn <stephan.hohn@tech11.com>
Signed-off-by: Caleb Lloyd <caleblloyd@gmail.com> Co-authored-by: Vadim Bauer <vb@container-registry.com>
Comprehensive Summary of your change
Harbor should not assume that if AWS Credentials are not defined that the user wants to use
ec2rolecreds. Rather, it should allow the AWS SDK to resolve credentials by passingnilCredentials:https://docs.aws.amazon.com/sdk-for-go/v1/developer-guide/configuring-sdk.html#specifying-credentials
This should be backwards compatible because the defualt provider chain does look for:
4. If your application is running on an Amazon EC2 instance, IAM role for Amazon EC2.Issue being fixed
Fixes #15007
Related to #17962
Please indicate you've done the following: