Updates to pre-built Security ML jobs#154596
Conversation
 pjhampton
left a comment
pjhampton
left a comment
There was a problem hiding this comment.
Looks good from a security data analytics perspective
...ins/ml/server/models/data_recognizer/modules/security_auth/ml/suspicious_login_activity.json
Outdated
Show resolved
Hide resolved
...er/models/data_recognizer/modules/security_network/ml/high_count_by_destination_country.json
Outdated
Show resolved
Hide resolved
...erver/models/data_recognizer/modules/security_windows/ml/v3_windows_anomalous_user_name.json
Outdated
Show resolved
Hide resolved
...server/models/data_recognizer/modules/security_windows/ml/v3_windows_rare_metadata_user.json
Outdated
Show resolved
Hide resolved
...ver/models/data_recognizer/modules/security_windows/ml/v3_windows_rare_user_runas_event.json
Outdated
Show resolved
Hide resolved
...ls/data_recognizer/modules/security_windows/ml/v3_windows_rare_user_type10_remote_login.json
Outdated
Show resolved
Hide resolved
|
Pinging @elastic/ml-ui (:ml) |
 peteharverson
left a comment
peteharverson
left a comment
There was a problem hiding this comment.
Added a few suggestions for minor edits to job and detector descriptions, but otherwise overall looks good.
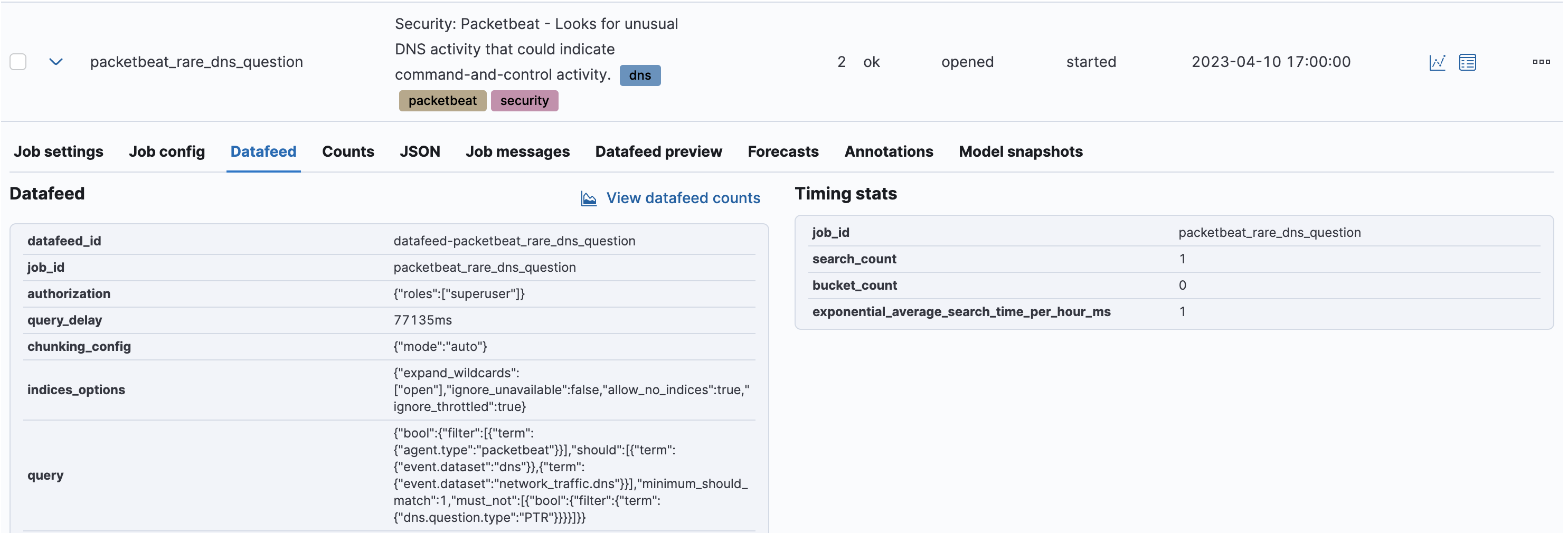
Tested creation of most of these jobs in the ML UI:
- Security: Authentication
- Security: Cloudtrail
- Security: Linux
- Security: Packetbeat
- Security: Windows
...ins/ml/server/models/data_recognizer/modules/security_auth/ml/auth_rare_hour_for_a_user.json
Outdated
Show resolved
Hide resolved
...l/server/models/data_recognizer/modules/security_auth/ml/auth_rare_source_ip_for_a_user.json
Outdated
Show resolved
Hide resolved
x-pack/plugins/ml/server/models/data_recognizer/modules/security_auth/ml/auth_rare_user.json
Outdated
Show resolved
Hide resolved
|
@elasticmachine merge upstream |
| "time_field": "@timestamp" | ||
| }, | ||
| "custom_settings": { | ||
| "job_tags": { |
There was a problem hiding this comment.
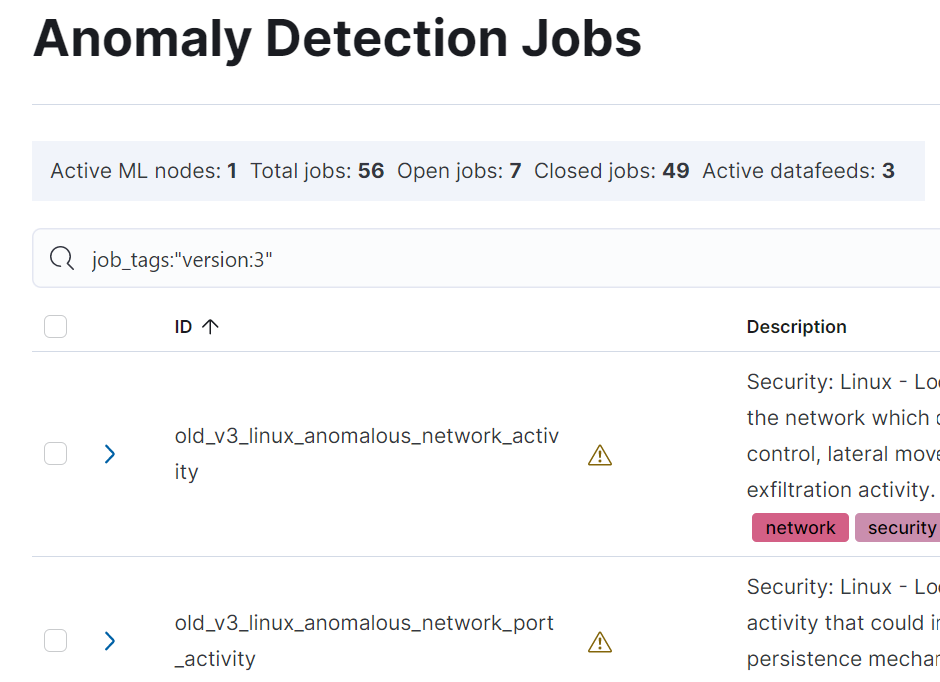
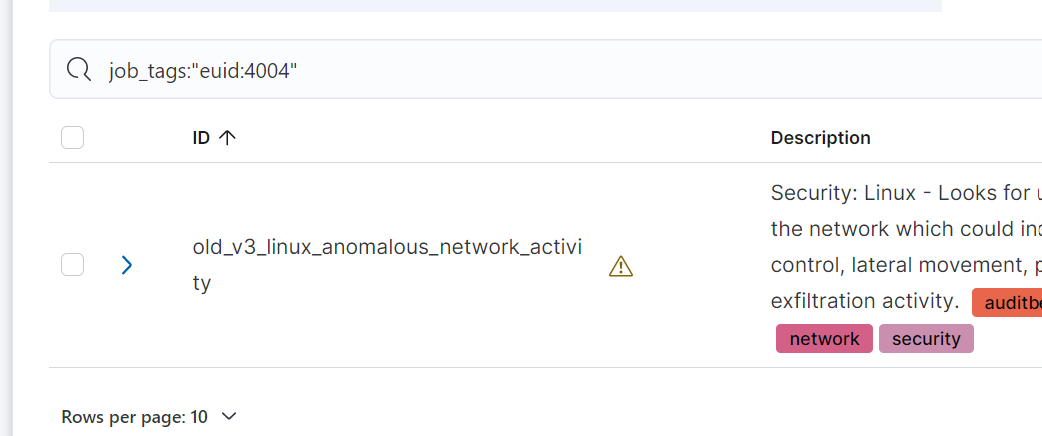
@ajosh0504 as mentioned, note that the purpose of these job_tags properties was to allow searching on these properties in the ML jobs list, for example for jobs with specific versions
or specific euid:
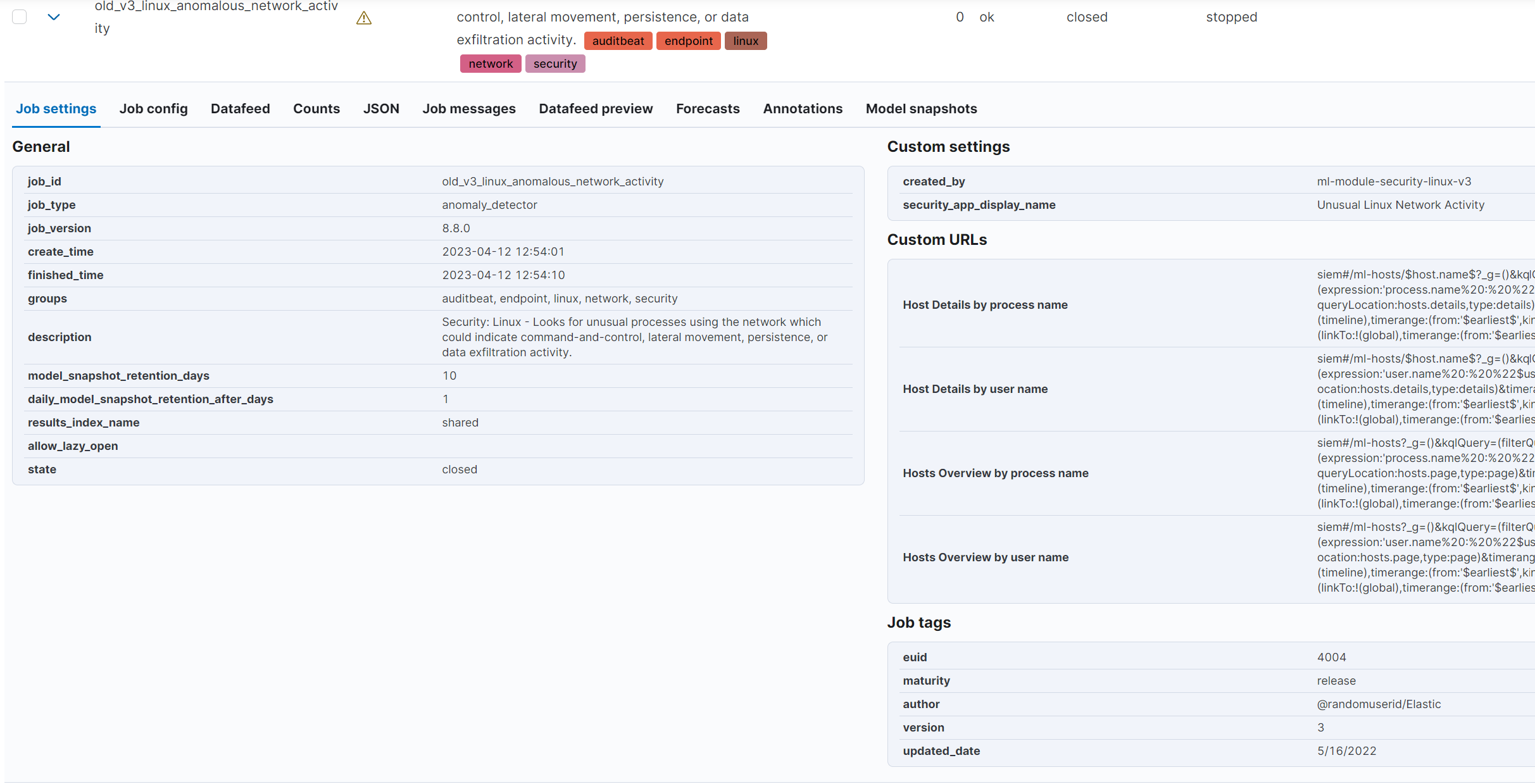
and these tags are also displayed in a dedicated section in the expanded job row:
See original issue, and the support that was added for them in 7.14: #102099
Note that the Logs UI use an alternative approach for versioning jobs - https://github.com/elastic/kibana/blob/main/x-pack/plugins/ml/server/models/data_recognizer/modules/logs_ui_categories/ml/log_entry_categories_count.json#L38, but this job_revision property is not searchable in the ML job management page.
I am ok with you removing these job_tags if they are no longer providing value, but wanted to provide context on why we originally added them to many of the security jobs.
There was a problem hiding this comment.
@peteharverson Thanks for providing context. My thoughts on the above:
- Afaik we aren't using these fields internally.
- In terms of searching in the UI, I'm not sure how much of a value searching for v3 jobs is providing. Typically, we see our users upgrading to the latest version of jobs, rather than keeping both old as well as new jobs. Also having versions only for some jobs is a bit odd, given that other jobs (that don't have the version tags) have also undergone updates. I would like to have some versioning for all jobs, but I'd like to discuss this further outside of this PR, given that we are unofficially already several versions along across all our modules.
- I don't understand the value provided by the
euidfield, specifically given that it is retained when the job is cloned. I'd understand if it was a unique identifier for a job so as to distinguish between different copies of the same job, but that not being the case, I don't see a ton of value in it.
There was a problem hiding this comment.
I'm happy to defer to you on this one @ajosh0504 and remove these job_tags.
The thinking behind euid was that this field couldn't (easily) be changed by the user, whereas they are able to completely change the job ID when cloning, so it could be used to track how many of this type of job had been created.
Makes sense to address a way to version all the security jobs outside of this PR.
 peteharverson
left a comment
peteharverson
left a comment
There was a problem hiding this comment.
Changes look good for ML.
|
@pheyos Tagging you to see if anything at y'all's end needs updating given the changes in this PR. |
💚 Build Succeeded
Metrics [docs]Unknown metric groupsESLint disabled line counts
Total ESLint disabled count
History
To update your PR or re-run it, just comment with: cc @ajosh0504 |
 pheyos
left a comment
pheyos
left a comment
There was a problem hiding this comment.
Thanks for the heads-up @ajosh0504! Indeed, we'll have to do some follow-up adjustments to our tests in the ML QA framework once your PR is merged , I'll take care of that.

Summary
This PR makes the following updates to the pre-built Security ML jobs:
security-packetbeatcompatible with Agentdetector_descriptionfield for almost all jobsjob_revisioncustom setting similar to the Logs jobs. Moving forward, this number will be updated each time a job is updated. We are starting with 4 since thelinuxandwindowsjobs are at v3 right nowmanaged:truetag to indicate that these jobs are pre-configured by Elastic and so users will see the warnings added in this PR if users choose to delete, or modify these jobs