[Defend for containers] cloud_defend plugin UI boilerplate#151533
[Defend for containers] cloud_defend plugin UI boilerplate#151533mitodrummer merged 35 commits intoelastic:mainfrom
Conversation
…mmer/kibana into cloud_defend_manage_ui_bootstrap
 JordanSh
left a comment
JordanSh
left a comment
There was a problem hiding this comment.
Changes in cloud security posture LGTM 👌
…mmer/kibana into cloud_defend_manage_ui_bootstrap
 semd
left a comment
semd
left a comment
There was a problem hiding this comment.
@mitodrummer The implementation overall looks great!
I wrote a couple of comments.
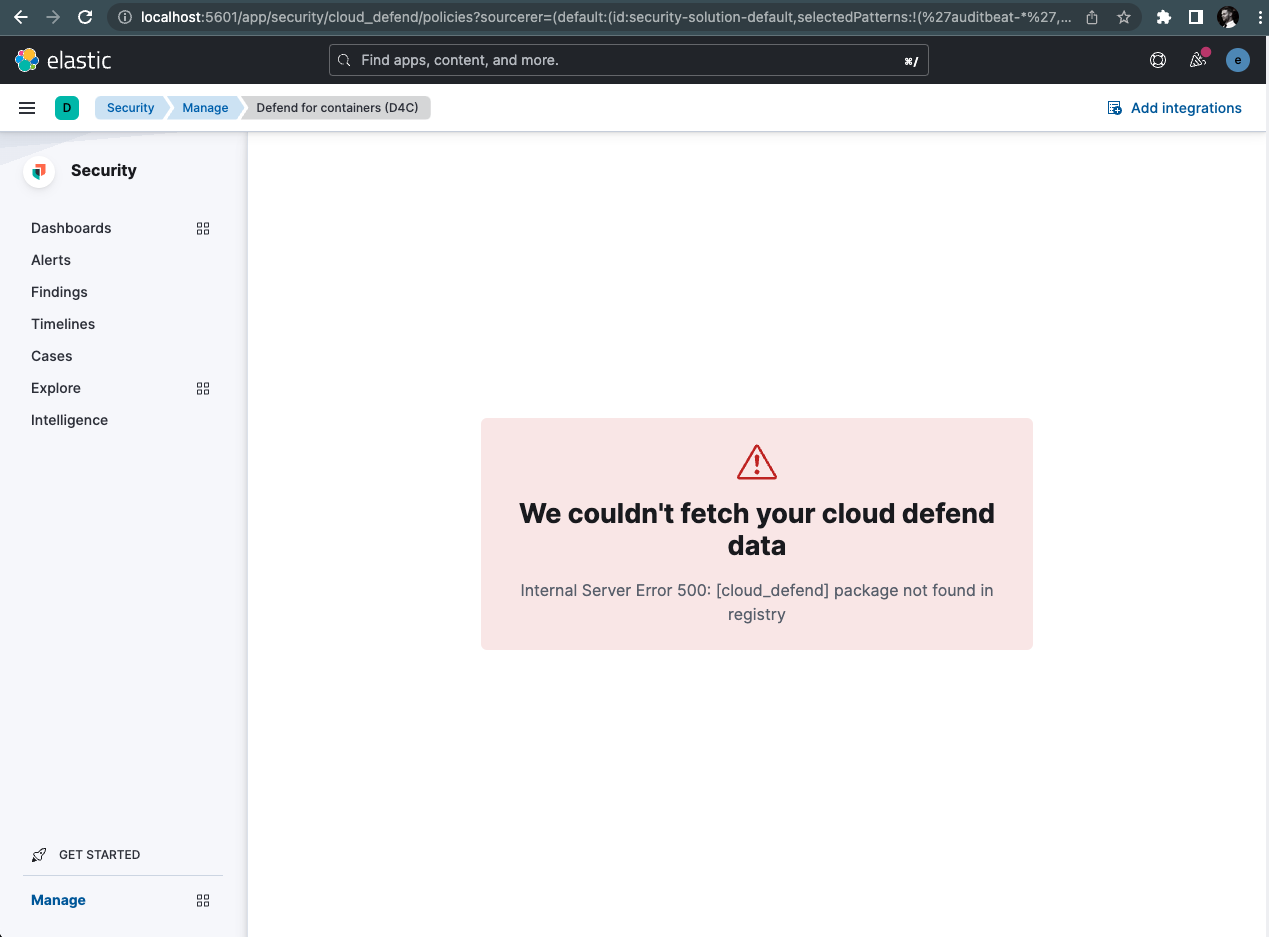
Also, when testing it I am seeing this error when I do not have the package installed:
And the server throws:
[ERROR][plugins.cloudDefend] PackageNotFoundError: [cloud_defend] package not found in registry
at fetchFindLatestPackageOrThrow (index.ts:150:11)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at async Promise.all (index 2)
at getCloudDefendStatus (status.ts:110:7)
at status.ts:183:24
at Router.handle (router.ts:192:30)
at handler (router.ts:147:13)
at exports.Manager.execute .
...
Is there any onboarding screen? Otherwise, probably we should check if cloud_defend is enabled and hide all links if not.
x-pack/plugins/security_solution/public/common/links/app_links.ts
Outdated
Show resolved
Hide resolved
x-pack/plugins/security_solution/public/cloud_defend/routes.tsx
Outdated
Show resolved
Hide resolved
Yea, next step is to sort out some stuff with our integration and getting an updated version to EPR. That should fix the issue you are seeing. This is happening since our package is "beta" (e.g version < 1.0.0). I have updates queued to push out our first 1.0.0 version this week, so should be resolved soon. |
💛 Build succeeded, but was flaky
Failed CI StepsTest Failures
Metrics [docs]Module Count
Public APIs missing comments
Async chunks
Public APIs missing exports
Page load bundle
Unknown metric groupsAPI count
async chunk count
ESLint disabled in files
ESLint disabled line counts
Total ESLint disabled count
History
To update your PR or re-run it, just comment with: |
Okay sounds good, but the question is: |
This is handled now by the cloud_defend_page component. It will show empty state with button to install integration if not installed, and also handle license checks. |
Great! Just FYI, if we ever have to make a cloud_defend link inaccessible under some condition, it has to be done here: Thanks! |
…51533) ## Summary This PR aims to create a footprint in the "security_solution" manage page for the new cloud_defend integration (and kibana plugin). Most of the changes are taken from the cloud_security_posture plugin architecture. The following additions have been made: - "Cloud security posture" category in manage page now includes a link to a new "Defend for containers" policies page (I originally created a new category for cloud_defend, but having two full categories with a single link is kind of a waste of real estate). - Cloud defend page wrapper to handle empty states, and the flows for when the integration is not yet installed, or user doesn't have cloud enterprise subscription. - Basic policies page to serve as a baseline for future detail around each cloud_defend integration (e.g selector / response / alert counts). - Application router and sub plugin tie'ins to security_solution. *Apologies in advance for the large PR :)* ### Screenshots Manage link  Policies page  ### Checklist Delete any items that are not applicable to this PR. - [x] Any text added follows [EUI's writing guidelines](https://elastic.github.io/eui/#/guidelines/writing), uses sentence case text and includes [i18n support](https://github.com/elastic/kibana/blob/main/packages/kbn-i18n/README.md) - [x] [Unit or functional tests](https://www.elastic.co/guide/en/kibana/master/development-tests.html) were updated or added to match the most common scenarios - [x] Any UI touched in this PR is usable by keyboard only (learn more about [keyboard accessibility](https://webaim.org/techniques/keyboard/)) - [x] Any UI touched in this PR does not create any new axe failures (run axe in browser: [FF](https://addons.mozilla.org/en-US/firefox/addon/axe-devtools/), [Chrome](https://chrome.google.com/webstore/detail/axe-web-accessibility-tes/lhdoppojpmngadmnindnejefpokejbdd?hl=en-US)) - [x] This renders correctly on smaller devices using a responsive layout. (You can test this [in your browser](https://www.browserstack.com/guide/responsive-testing-on-local-server)) - [x] This was checked for [cross-browser compatibility](https://www.elastic.co/support/matrix#matrix_browsers) --------- Co-authored-by: kibanamachine <42973632+kibanamachine@users.noreply.github.com>
Summary
This PR aims to create a footprint in the "security_solution" manage page for the new cloud_defend integration (and kibana plugin). Most of the changes are taken from the cloud_security_posture plugin architecture. The following additions have been made:
Apologies in advance for the large PR :)
Screenshots
Manage link

Policies page

Checklist
Delete any items that are not applicable to this PR.