cisco_asa: add handling of AAA operations#3740
Conversation
🌐 Coverage report
|
|
Pinging @elastic/security-external-integrations (Team:Security-External Integrations) |
eabc150 to
b7f5320
Compare
|
@efd6 seems like even.outcome always "success" but for failed authentications it should be "failure". |
|
@leweafan Yeah, this can be confusing. Success is always a contextual thing; from the perspective of the attempting authenticator, a failure to auth is a failure, but if this entity is malicious it is a success for the people who matter. So in the ECS definition you can see
The entity that produced the event is the device and it must have confidence in its decisions, so all authentications that have a definitive answer are successful. If there were a failure due to a network or identity store problem, those would be failures. You can use It looks like there is some confusion/ambiguity around this. I am looking into it further. |
|
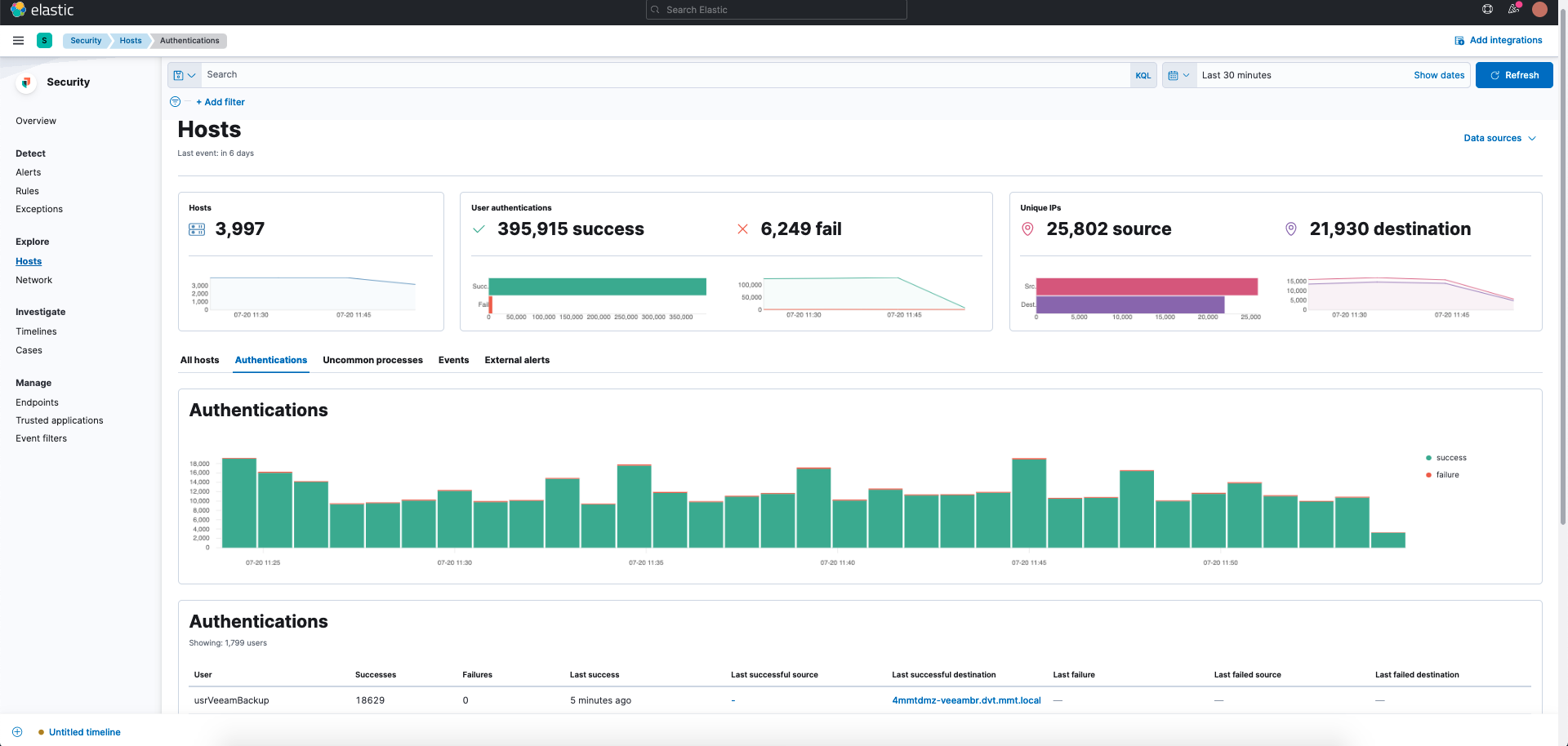
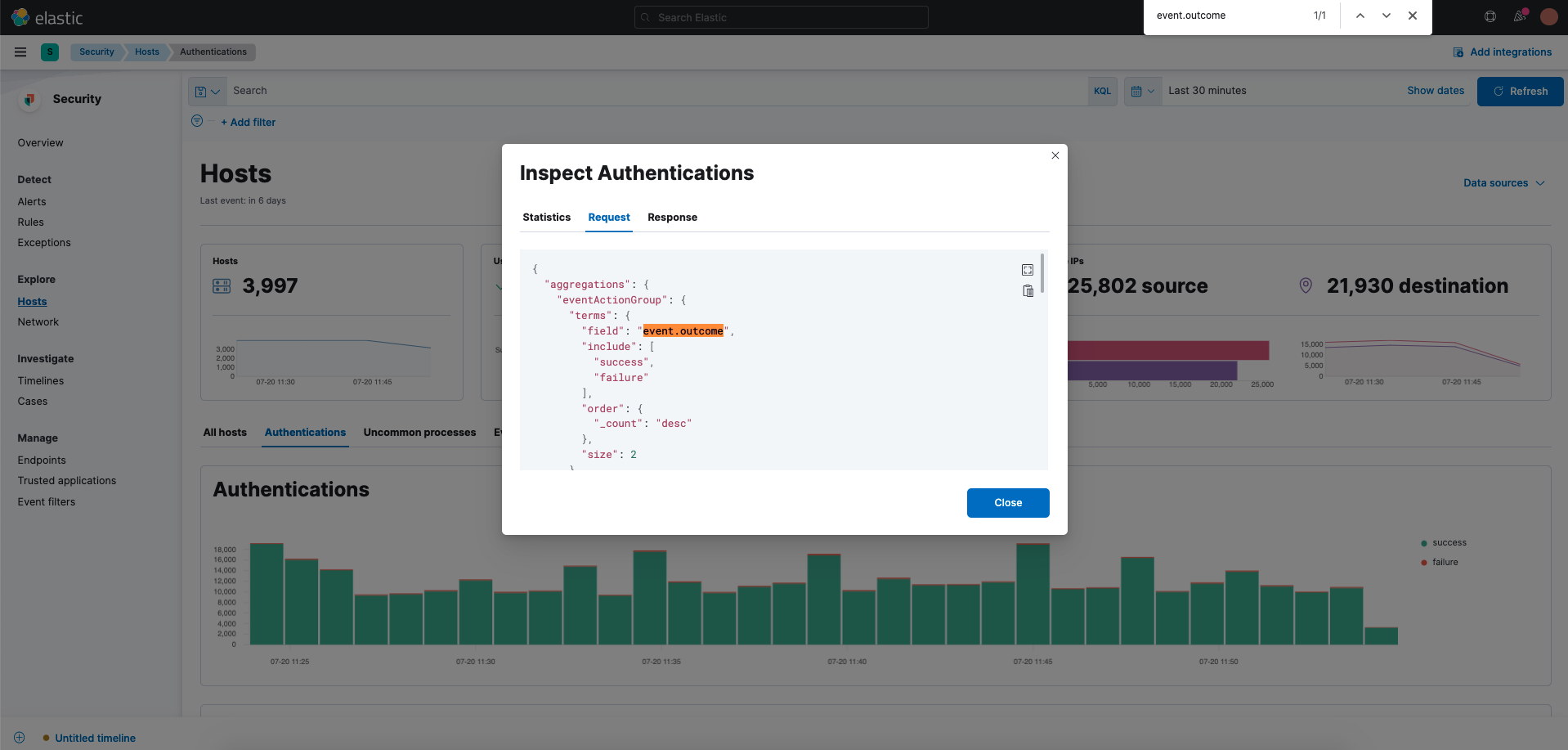
@efd6 event.outcome is very important for SIEM cause if we go to Sercurity -> Hosts -> Authentications there is a graph for successful and failed attempts and a table representation with users their 'Successes'/'Failures'/'Last failure'/'Last failed source'/'Last failed destination' that depend on event.outcome = "failure". Please find screenshots in attachments. |
|
Yes, having had a look at the background discussion, this appears to be the original intention. I will make this change. |
|
@efd6 answered a minute before to andrewkroh about checkpoint version in another issue elastic/beats#32230 |
|
@leweafan Thanks for that, I was also thinking you might like to confirm the orientation of success/failure in that PR. |
|
@efd6 looks good |
|
/test |






What does this PR do?
This adds handling of authentication fields for Cisco ASA AAA message types.
Checklist
changelog.ymlfile.Author's Checklist
How to test this PR locally
Related issues
Screenshots