New integration for SonicWall firewall#3365
New integration for SonicWall firewall#3365adriansr merged 26 commits intoelastic:mainfrom adriansr:new_sonicwall
Conversation
|
Pinging @elastic/security-external-integrations (Team:Security-External Integrations) |
🌐 Coverage report
|
|
@adriansr is it possible to add a dashboard to avoid having to revisit down the line? Some potential resources on the dashboard: Top 10 Source IPs |
|
@adriansr is it also possible to include the support log types within the integration description, to set expectations as to which events are covered? e.g. System, Users, VPN, Firewall. Full list available on page 5 here: https://www.sonicwall.com/techdocs/pdf/sonicos-6-5-4-log-events-reference-guide.pdf |
|
sure @jamiehynds , will do |
This integration allows to receive syslog messages from SonicOS devices. Replaces the existing rsa2elk integration. Co-authored-by: jhaugh0 <jfhaugh@wol.org>
 efd6
left a comment
efd6
left a comment
There was a problem hiding this comment.
Minor comments only, otherwise LGTM.
| - add_locale: ~ | ||
| {{#if processors}} | ||
| {{processors}} | ||
| {{/if}} No newline at end of file |
| - name: sonicwall | ||
| type: group | ||
| fields: | ||
| - name: firewall |
There was a problem hiding this comment.
Worth a description of the data that would be here?
| description: Extracts optional port number from src nat field | ||
| ignore_missing: true | ||
| patterns: | ||
| - '^%{IPV4:source.nat.ip}:%{POSINT:source.nat.port}$' |
There was a problem hiding this comment.
This one is there to handle the (undocumented) case of the nat field being ip:port instead of ip. I've only observed this with IPv4, not sure if that can happen with IPv6 and what the format would be.
Just in case I added support for [ipv6]:port, which in my understanding is a common way of appending a port to an IPv6 address.
There was a problem hiding this comment.
I have a set of patterns that work for this, but it can happen in a later PR. (
)| @@ -0,0 +1,78 @@ | |||
| # SonicWall Firewall Integration | |||
|
|
|||
| This integration collects syslog messages from SonicWall firewalls. It has been tested with SonicOS 6.5 and 7.0. | |||
There was a problem hiding this comment.
Add a link to the vendor docs?
| - creation | ||
| outcome: success | ||
|
|
||
| message_codes: |
There was a problem hiding this comment.
For future maintenance a link to the origin for these would be helpful.
| } | ||
|
|
||
| # | ||
| # Extends message field with note |
| }, | ||
| "event": { | ||
| "code": "97", | ||
| "original": "10.0.0.1 id=firewall sn=12345678 time=\"2022-03-11 14:17:52 UTC\" fw=10.0.0.2 pri=6 c=1024 gcat=2 m=97 srcMac=12:34:56:78:90:ab src=10.0.0.4:41856:X0 srcZone=Trusted natSrc=10.0.0.2:8689 dstMac=ab:09:87:65:43:21 dst=89.160.20.112:443:X1 dstZone=Untrusted natDst=89.160.20.112:443 usr=\"Unknown (SSO failed)\" proto=tcp/https sent=104 rcvd=230 rule=\"15 (LAN-\u003eWAN)\" app=5 af_polid=4 ipscat=N/A appcat=\"PROXY-ACCESS\" appid=2900 dstname=89.160.20.112 arg=/ code=64 Category=\"Not Rated\" note=\"Policy: cfsZonePolicy0, Info: 6148 \" n=2520325 fw_action=\"NA\" dpi=1 op=0", |
There was a problem hiding this comment.
It looks like no message is written when there is a note, but no msg. Maybe promote the note to a message in this case?
 P1llus
left a comment
P1llus
left a comment
There was a problem hiding this comment.
LGTM, added some comments that are more questions rather than fixes.
Awesome job on the documentation and dashboarding as well! :)
| @@ -0,0 +1,20 @@ | |||
| host: "{{syslog_host}}:{{syslog_port}}" | |||
There was a problem hiding this comment.
I know that @taylor-swanson has been doing some changes to allow for both TCP and UDP for all our firewall integrations, would it be worthwhile to add a similar one here?
There was a problem hiding this comment.
In this case, the SonicWall only supports UDP so I kept it simple. I see they've received requests for tcp+ssl but the latest version is still udp-only.
https://community.sonicwall.com/technology-and-support/discussion/1774/syslog-over-secure-tcp
| @@ -0,0 +1,6 @@ | |||
| # newer versions go on top | |||
| - version: "0.6.0" | |||
There was a problem hiding this comment.
Is it correct for the initial version to be 0.6.0 rather than 0.1.0?
There was a problem hiding this comment.
You're right. The integrations docs require the use of 0.1.0 for a new package.
https://github.com/elastic/integrations/blob/main/docs/tips_for_building_integrations.md#manifest-files
| type: constant_keyword | ||
| description: Data stream dataset. | ||
| - name: data_stream.namespace | ||
| type: constant_keyword |
There was a problem hiding this comment.
Do we not add in event.module and event.dataset anymore? For example:
- name: event.module
type: constant_keyword
description: Event module
value: o365
- name: event.dataset
type: constant_keyword
description: Event dataset
value: o365.audit
There was a problem hiding this comment.
Given that elastic-package doesn't add those when creating a data_stream, I though those were not needed anymore now that we have the data_stream.* fields. But it's worth adding them






What does this PR do?
This integration (
sonicwall_firewall) allows to receive syslog messages from SonicOS devices.Replaces the existing rsa2elk integration (
sonicwall).Uses logs and some ideas from #2729 by @jhaugh0.
Checklist
changelog.ymlfile.Author's Checklist
Related issues
Screenshots
Dashboard:
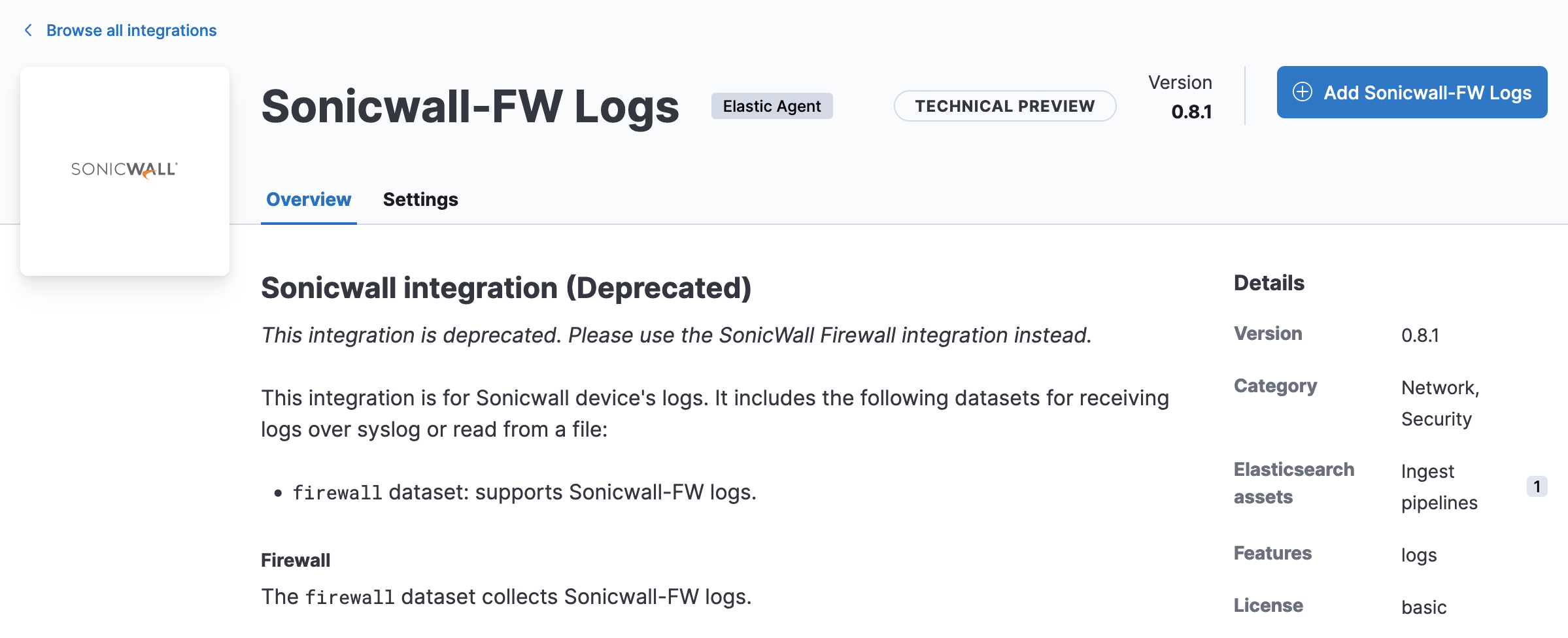
Deprecated package: