Fix redirect when not presenting FIDO#2651
Merged
Conversation
**Why**: The 2FA options list for login does not display FIDO when it is not supported. However the code bypasses the selection list and takes you to the preferred option that you have configured. A redirect was added to take the user back to the selection list but it was added to the setup js and not the authenticate js **How**: In webauthn-authenticate.js, redirect to /login/two_factor/options when the user is on the webauthn login screen and FIDO is not supported.
Contributor
Author
|
See notes on #2642 |
Contributor
Author
brodygov
previously approved these changes
Nov 9, 2018
brodygov
approved these changes
Nov 9, 2018
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
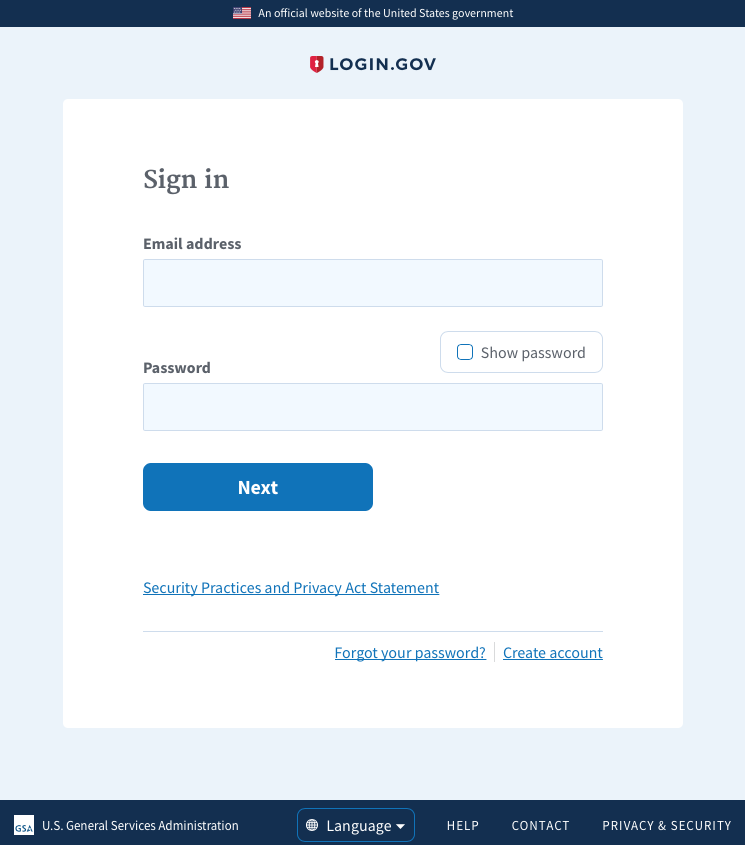
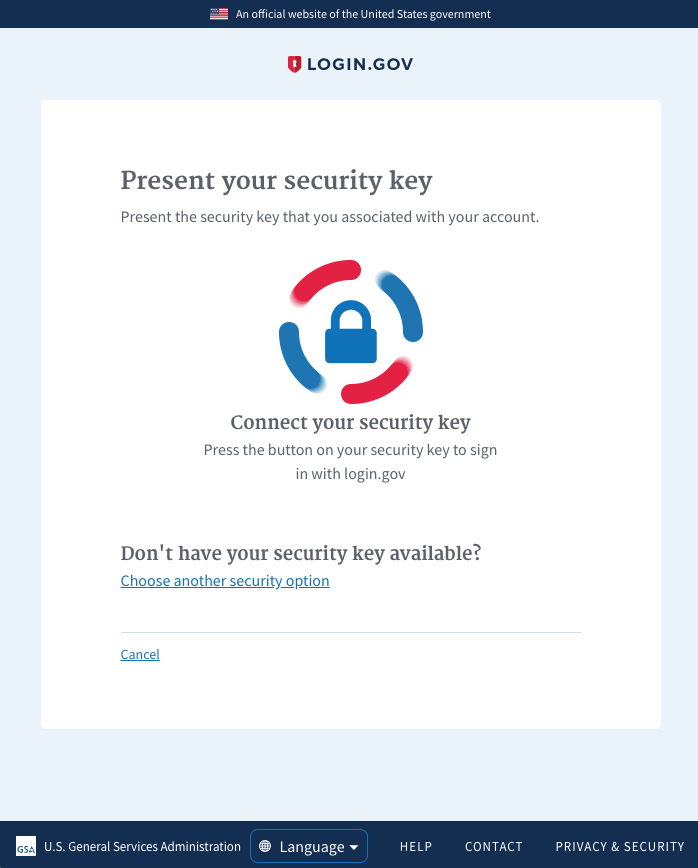
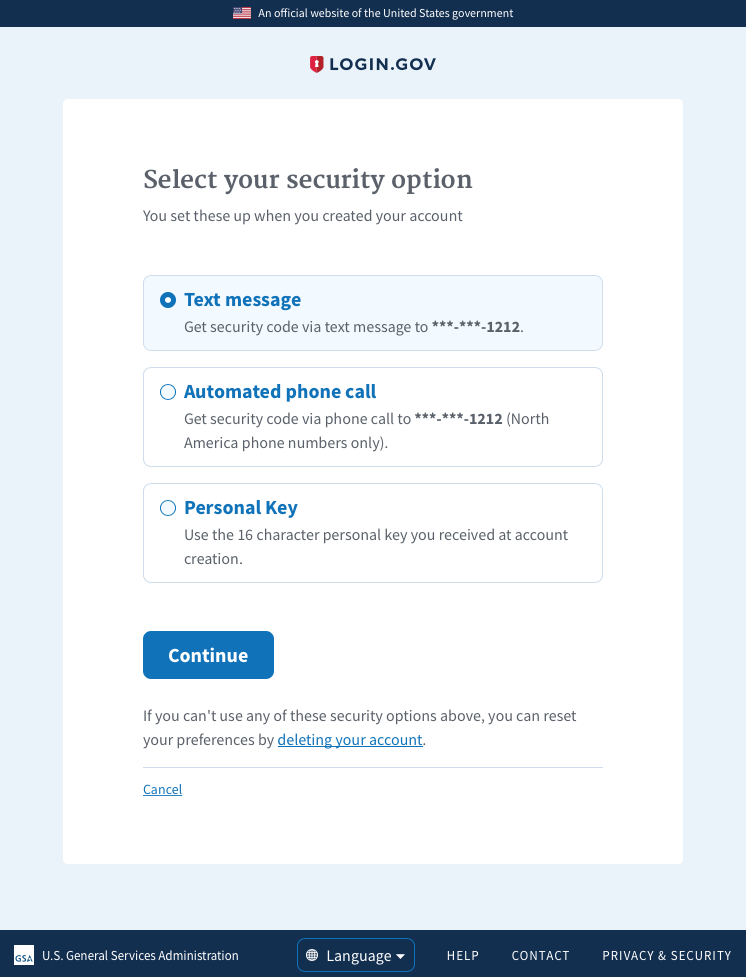
Why: The 2FA options list for login does not display FIDO when it is not supported. However the code bypasses the selection list and takes you to the preferred option that you have configured. A redirect was added to take the user back to the selection list but it was added to the setup js and not the authenticate js
How: In webauthn-authenticate.js, redirect to /login/two_factor/options when the user is on the webauthn login screen and FIDO is not supported.
Hi! Before submitting your PR for review, and/or before merging it, please
go through the checklists below. These represent the more critical elements
of our code quality guidelines. The rest of the list can be found in
CONTRIBUTING.md
Controllers
authenticated, make sure to add
before_action :confirm_two_factor_authenticatedas the first callback.
Database
Unsafe migrations are implemented over several PRs and over several
deploys to avoid production errors. The strong_migrations gem
will warn you about unsafe migrations and has great step-by-step instructions
for various scenarios.
Indexes were added if necessary. This article provides a good overview
of indexes in Rails.
Verified that the changes don't affect other apps (such as the dashboard)
When relevant, a rake task is created to populate the necessary DB columns
in the various environments right before deploying, taking into account the users
who might not have interacted with this column yet (such as users who have not
set a password yet)
Migrations against existing tables have been tested against a copy of the
production database. See LG-228 Make migrations safer and more resilient #2127 for an example when a migration caused deployment
issues. In that case, all the migration did was add a new column and an index to
the Users table, which might seem innocuous.
Encryption
Routes
state or result in destructive behavior).
Session
user_sessionhelperinstead of the
sessionhelper so the data does not persist beyond the user'ssession.
Testing
and invalid inputs.