Conversation
monfresh
reviewed
Jun 14, 2018
| key_handle = nil | ||
| @kmu.wait_for(:output, /Key Handle: \d+/) do |_process, matching| | ||
| matching.matched =~ /Key Handle: (\d+)/ | ||
| key_handle = Regexp.last_match[1] |
Contributor
There was a problem hiding this comment.
Code Climate says lines 101 and 102 are not tested.
monfresh
reviewed
Jun 14, 2018
| @kmu << "listUsers\n" | ||
| user_id = nil | ||
| @kmu.wait_for(:output, /\d+\s+CU\s+#{@idp_username}/) do |_process, matching| | ||
| user_id = matching.matched.split[0] |
Contributor
There was a problem hiding this comment.
Code Climate says line 54 is not tested.
cb6e8d0 to
d852f30
Compare
8788d58 to
d76591b
Compare
Contributor
Author
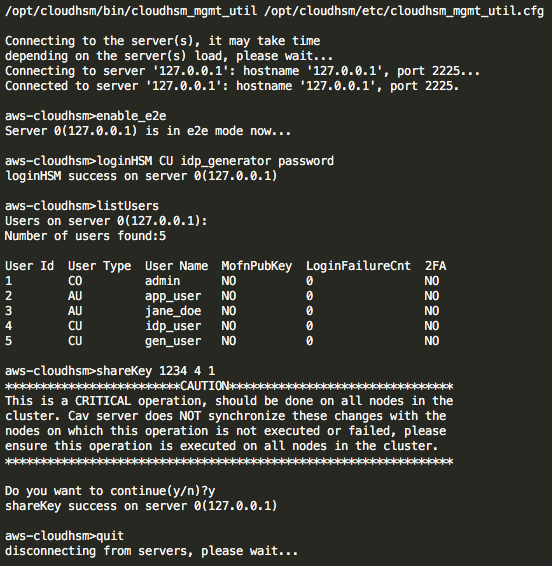
…o generated keys **Why**: To separate the key creator from the IDP user **How**: Create the CloudhsmKeySharer script to interface to cloudhsm_mgmt_util using the credentials and key handle output by the CloudhsmKeyGenerator. Use the greenletters gem to automate interaction with the commandline utility and obscure the password.
2677dd1 to
2eba64e
Compare
jgsmith-usds
approved these changes
Aug 9, 2018
| end | ||
|
|
||
| def login_to_hsm | ||
| @kmu << "loginHSM CU #{@username} #{@password}\n" |
Contributor
There was a problem hiding this comment.
We need to document that all of these interpolated arguments should never have spaces in them.
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
Why: To separate the key creator from the IDP user
How: Create the CloudhsmKeySharer script to interface to cloudhsm_mgmt_util using the credentials and key handle output by the CloudhsmKeyGenerator. Use the greenletters gem to automate interaction with the commandline utility and obscure the password.
Hi! Before submitting your PR for review, and/or before merging it, please
go through the following checklist:
For DB changes, check for missing indexes, check to see if the changes
affect other apps (such as the dashboard), make sure the DB columns in the
various environments are properly populated, coordinate with devops, plan
migrations in separate steps.
For route changes, make sure GET requests don't change state or result in
destructive behavior. GET requests should only result in information being
read, not written.
For encryption changes, make sure it is compatible with data that was
encrypted with the old code.
For secrets changes, make sure to update the S3 secrets bucket with the
new configs in all environments.
Do not disable Rubocop or Reek offenses unless you are absolutely sure
they are false positives. If you're not sure how to fix the offense, please
ask a teammate.
When reading data, write tests for nil values, empty strings,
and invalid formats.
When calling
redirect_toin a controller, use_url, not_path.When adding user data to the session, use the
user_sessionhelperinstead of the
sessionhelper so the data does not persist beyond the user'ssession.
When adding a new controller that requires the user to be fully
authenticated, make sure to add
before_action :confirm_two_factor_authenticated.