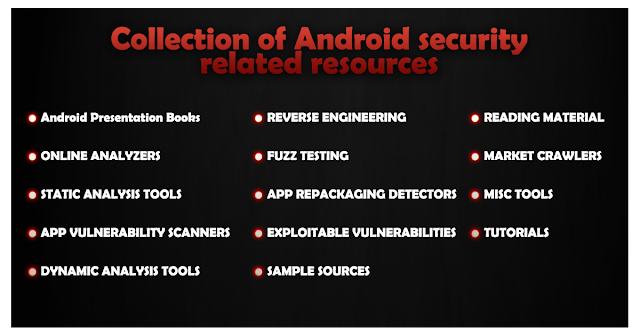
A collection of android security related resources.
A lot of work is happening in academia and industry on tools to perform dynamic analysis, static analysis and reverse engineering of android apps.
##Books
- http://amzn.to/2jkFvjg Android Security Internals: An In-Depth Guide to Android's Security Architecture
- http://amzn.to/2jkK0uf Android Security: Attacks and Defenses
- http://amzn.to/2jLHqd6 Android Security Cookbook
- http://amzn.to/2jLL5HR Android Hacker's Handbook
- http://amzn.to/2jLPY3L Android Forensics: Investigation, Analysis and Mobile Security for Google Android
- http://amzn.to/2ipWhhu Android Apps Security
- http://amzn.to/2iq3nCk Android Malware and Analysis
- http://amzn.to/2jkBlrR Mobile Forensic Investigations: A Guide to Evidence Collection, Analysis, and Presentation
- http://amzn.to/2jkJIU7 The Mobile Application Hacker's Handbook
- http://amzn.to/2iyIXW8 Android Application Security Essentials
- http://amzn.to/2jLJvWs Learning Pentesting for Android Devices
- Dexter
- Tracedroid
- Visual Threat
- Mobile Malware Sandbox
- MobiSec Eacus
- Appknox - not free
- IBM Security AppScan Mobile Analyzer - not free
- NVISO ApkScan
- AVC UnDroid
- Fireeye- max 60MB 15/day
- habo 10/day
- Virustotal-max 128MB
- Fraunhofer App-ray - not free
- AppCritique - Upload your Android APKs and receive comprehensive free security assessments.
- Androwarn - detect and warn the user about potential malicious behaviours developped by an Android application.
- ApkAnalyser
- APKInspector
- Droid Intent Data Flow Analysis for Information Leakage
- DroidLegacy
- Several tools from PSU
- Smali CFG generator
- FlowDroid
- Android Decompiler – not free
- PSCout - A tool that extracts the permission specification from the Android OS source code using static analysis
- Amandroid
- SmaliSCA - Smali Static Code Analysis
- CFGScanDroid - Scans and compares CFG against CFG of malicious applications
- Madrolyzer - extracts actionable data like C&C, phone number etc.
- SPARTA - verifies (proves) that an app satisfies an information-flow security policy; built on the Checker Framework
- ConDroid - Performs a combination of symoblic + concrete execution of the app
- QARK - QARK by LinkedIn is for app developers to scan app for security issues
- AndroBugs
- Nogotofail
- Devknox - Autocorrect security issues as if it was spell check from your IDE
- Android DBI frameowork
- Androl4b- A Virtual Machine For Assessing Android applications, Reverse Engineering and Malware Analysis
- Android Malware Analysis Toolkit - (linux distro) Earlier it use to be an online analyzer
- Mobile-Security-Framework MobSF - Mobile Security Framework is an intelligent, all-in-one open source mobile application (Android/iOS) automated pen-testing framework capable of performing static, dynamic analysis and web API testing.
- AppUse – custom build for pentesting
- Cobradroid – custom image for malware analysis
- ViaLab Community Edition
- Droidbox
- Mercury
- Drozer
- Xposed - equivalent of doing Stub based code injection but without any modifications to the binary
- Inspeckage - Android Package Inspector - dynamic analysis with api hooks, start unexported activities and more. (Xposed Module)
- Android Hooker - Dynamic Java code instrumentation (requires the Substrate Framework)
- ProbeDroid - Dynamic Java code instrumentation
- Android Tamer - Virtual / Live Platform for Android Security Professionals
- DECAF - Dynamic Executable Code Analysis Framework based on QEMU (DroidScope is now an extension to DECAF)
- CuckooDroid - Android extension for Cuckoo sandbox
- Mem - Memory analysis of Android (root required)
- Crowdroid – unable to find the actual tool
- AuditdAndroid – android port of auditd, not under active development anymore
- Android Security Evaluation Framework - not under active development anymore
- Android Reverse Engineering – ARE (android reverse engineering) not under active development anymore
- Aurasium – Practical security policy enforcement for Android apps via bytecode rewriting and in-place reference monitor.
- Android Linux Kernel modules
- Appie - Appie is a software package that has been pre-configured to function as an Android Pentesting Environment.It is completely portable and can be carried on USB stick or smartphone.This is a one stop answer for all the tools needed in Android Application Security Assessment and an awesome alternative to existing virtual machines.
- StaDynA - a system supporting security app analysis in the presence of dynamic code update features (dynamic class loading and reflection). This tool combines static and dynamic analysis of Android applications in order to reveal the hidden/updated behavior and extend static analysis results with this information.
- DroidAnalytics - incomplete
- Vezir Project - Virtual Machine for Mobile Application Pentesting and Mobile Malware Analysis
- MARA - Mobile Application Reverse engineering and Analysis Framework
- NowSecure Lab Automated - Enterprise tool for mobile app security testing both Android and iOS mobile apps. Lab Automated features dynamic and static analysis on real devices in the cloud to return results in minutes.
Taintdroid- requires AOSP compilation
- Smali/Baksmali – apk decompilation
- emacs syntax coloring for smali files
- vim syntax coloring for smali files
- AndBug
- Androguard – powerful, integrates well with other tools
- Apktool – really useful for compilation/decompilation (uses smali)
- Android Framework for Exploitation
- Bypass signature and permission checks for IPCs
- Android OpenDebug – make any application on device debuggable (using cydia substrate).
- Dare – .dex to .class converter
- Dex2Jar - dex to jar converter
- Enjarify - dex to jar converter from Google
- Dedexer
- Fino
- Frida - inject javascript to explore applications and a GUI tool for it
- Indroid – thread injection kit
- IntentSniffer
- Introspy
- Jad - Java decompiler
- JD-GUI - Java decompiler
- CFR - Java decompiler
- Krakatau - Java decompiler
- Procyon - Java decompiler
- FernFlower - Java decompiler
- Redexer – apk manipulation
- Smali viewer
ZjDroid,fork/mirror- Simplify Android deobfuscator
- Bytecode viewer
- Radare2
- Radamsa Fuzzer
- Honggfuzz
- An Android port of the melkor ELF fuzzer
- Media Fuzzing Framework for Android
- AndroFuzz
- FSquaDRA - a tool for detection of repackaged Android applications based on app resources hash comparison.
- Open Source database
- Drebin
- Admire
- MalGenome - contains 1260 malware samples categorized into 49 different malware families, free for research purpose.
- VirusTotal Malware Intelligence Service - powered by VirusTotal,not free
- Google play crawler (Python)
- Google play crawler (Node) - get app details and download apps from official Google Play Store.
- Aptoide downloader (Node) - download apps from Aptoide third-party Android market
- Appland downloader (Node) - download apps from Appland third-party Android market
- APK-Downloader
- AXMLPrinter2 - to convert binary XML files to human-readable XML files
- adb autocomplete
- Dalvik opcodes
- Opcodes table for quick reference
- ExploitMe Android Labs - for practice
- GoatDroid - for practice
- mitmproxy
- dockerfile/androguard
- Android Vulnerability Test Suite - android-vts scans a device for set of vulnerabilities
Please have a look at